- Pagină de pornire
- /
- Articol


Informații de referință privind porturile pentru Webex Calling
 În acest articol
În acest articol Feedback?
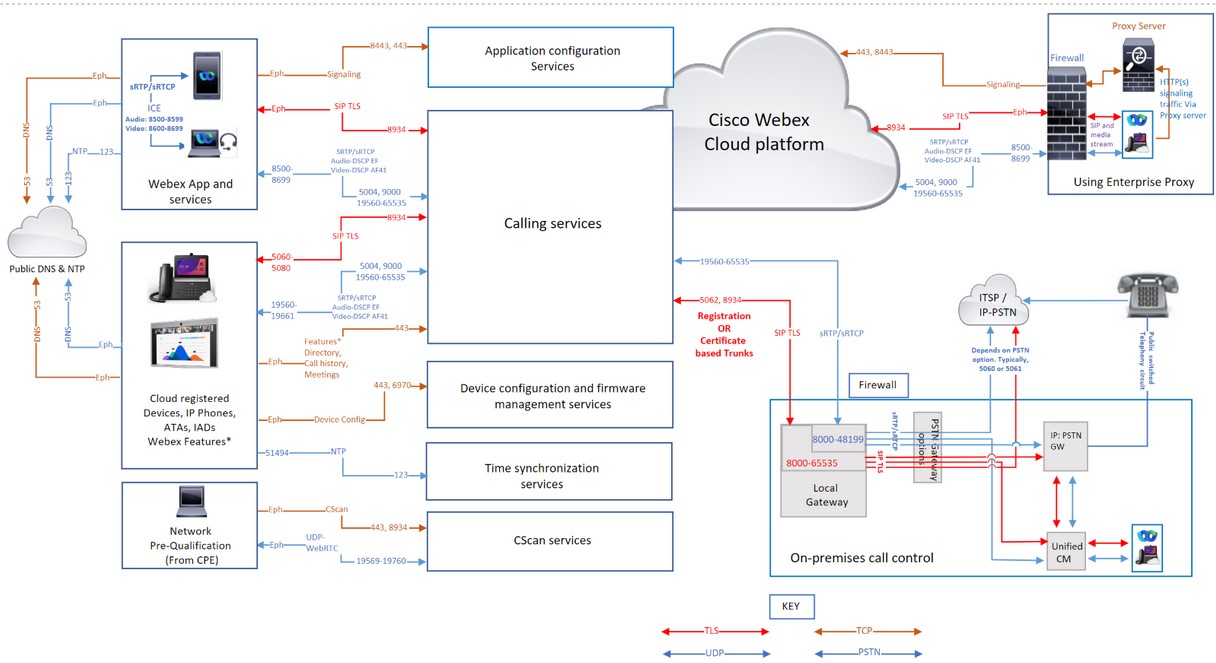
Feedback?Acest articol este destinat administratorilor de rețea, în special administratorilor de firewall și securității proxy care utilizează serviciile Webex Calling în cadrul organizației lor. Descrie cerințele de rețea și listează adresele, porturile și protocoalele utilizate pentru conectarea telefoanelor, a aplicației Webex și a gateway-urilor către serviciile Webex Calling.
Un firewall și un proxy configurați corect sunt esențiale pentru o implementare Calling reușită. Webex Calling utilizează SIP și HTTPS pentru semnalizarea apelurilor și adresele și porturile asociate pentru media, conexiunea la rețea și conectivitatea gateway-ului, deoarece Webex Calling este un serviciu global.
Nu toate configurațiile de firewall necesită deschiderea porturilor. Totuși, dacă executați reguli de tip „inside-to-out”, trebuie să deschideți porturi pentru protocoalele necesare pentru a permite accesul serviciilor.
Traducerea adreselor de rețea (NAT)
Funcționalitățile de traducere a adreselor de rețea (NAT) și de traducere a adreselor de port (PAT) sunt aplicate la granița dintre două rețele pentru a traduce spațiile de adrese sau pentru a preveni coliziunea spațiilor de adrese IP.
Organizațiile utilizează tehnologii de gateway, cum ar fi firewall-uri și proxy-uri, care oferă servicii NAT sau PAT pentru a oferi acces la internet aplicațiilor Webex App sau dispozitivelor Webex care se află într-un spațiu de adresă IP privat. Aceste gateway-uri fac ca traficul de la aplicațiile sau dispozitivele interne către internet să pară că provine de la una sau mai multe adrese IP rutabile public.
-
Dacă implementați NAT, nu este obligatoriu să deschideți un port de intrare pe firewall.
-
Validați dimensiunea pool-ului NAT necesară pentru conectivitatea aplicației sau dispozitivelor atunci când mai mulți utilizatori ai aplicației și dispozitive accesează Webex Calling & Servicii compatibile cu Webex care utilizează NAT sau PAT. Asigurați-vă că sunt atribuite adrese IP publice adecvate pool-urilor NAT pentru a preveni epuizarea porturilor. Epuizarea porturilor contribuie la imposibilitatea conectării utilizatorilor și dispozitivelor interne la serviciile Webex Calling și Webex Aware.
-
Definiți perioade de legare rezonabile și evitați manipularea SIP pe dispozitivul NAT.
-
Configurați un timeout NAT minim pentru a asigura funcționarea corectă a dispozitivelor. Exemplu: Telefoanele Cisco trimit un mesaj de reîmprospătare REGISTER la fiecare 1-2 minute.
-
Dacă rețeaua dvs. implementează NAT sau SPI, setați un timeout mai mare (de cel puțin 30 de minute) pentru conexiuni. Această perioadă de expirare permite o conectivitate fiabilă, reducând în același timp consumul bateriei dispozitivelor mobile ale utilizatorilor.
Gateway-ul nivelului de aplicație SIP
Dacă un router sau un firewall este compatibil cu SIP, ceea ce înseamnă că este activat SIP Application Layer Gateway (ALG) sau un dispozitiv similar, vă recomandăm să dezactivați această funcționalitate pentru funcționarea corectă a serviciului. Deși tot traficul Webex Calling este criptat, anumite implementări SIP ALG pot cauza probleme cu traversarea firewall-ului. Prin urmare, vă recomandăm să dezactivați SIP ALG pentru a asigura un serviciu de înaltă calitate.
Consultați documentația producătorului relevant pentru pașii de dezactivare a SIP ALG pe anumite dispozitive.
Asistență proxy pentru Webex Calling
Organizațiile implementează un firewall de internet sau un proxy de internet și un firewall pentru a inspecta, restricționa și controla traficul HTTP care iese și intră în rețeaua lor. Protejându-și astfel rețeaua de diverse forme de atacuri cibernetice.
Organizațiile configurează adesea servere proxy ca singura rută pentru redirecționarea traficului de internet bazat pe HTTP către firewall-ul companiei. Această configurație permite firewall-ului să restricționeze traficul de internet de ieșire, permițând doar traficul care provine de la serverul proxy.
Proxy-urile îndeplinesc mai multe funcții de securitate, cum ar fi:
-
Permiteți sau blocați accesul la anumite adrese URL.
-
Autentificarea utilizatorului
-
IP-ul address/domain/hostname/URI căutarea reputației
-
Decriptarea și inspecția traficului
La configurarea funcției proxy, aceasta se aplică tuturor aplicațiilor care utilizează protocolul HTTP.
Aplicația Webex și aplicațiile pentru dispozitive Webex includ următoarele:
-
Servicii Webex
-
Proceduri de activare a dispozitivelor clientului (CDA) utilizând platforma de provisioning Cisco Cloud, cum ar fi GDS, activarea dispozitivelor EDOS, provisioning & integrarea în cloud-ul Webex.
-
Autentificare certificat
-
Actualizări de firmware
-
Rapoarte de stare
-
Încărcări PRT
-
Servicii XSI
Nu modificați și nu ștergeți valorile antetului HTTP pe măsură ce trec prin proxy sau firewall, cu excepția cazului în care acest lucru este permis de aceste instrucțiuni altering-header-values. Modificarea sau eliminarea antetelor HTTP în afara acestor instrucțiuni poate afecta accesul la serviciile Webex Calling și Webex-Aware și poate cauza pierderea accesului aplicațiilor și dispozitivelor Webex.
Dacă este configurată o adresă de server proxy, atunci numai traficul de semnalizare (HTTP/HTTPS) este trimis către serverul proxy. Clienții care utilizează SIP pentru a se înregistra la serviciul Webex Calling și suporturile media asociate nu sunt trimiși la proxy. Prin urmare, permiteți acestor clienți să treacă direct prin firewall.
Opțiuni proxy acceptate, configurare & Tipuri de autentificare
Tipurile de proxy acceptate sunt:
-
Proxy explicit (cu inspecție sau fără inspecție) - Configurați clienții, fie Aplicație, fie Dispozitiv, cu proxy explicit pentru a specifica serverul de utilizat.
-
Proxy transparent (fără inspecție) - Clienții nu sunt configurați să utilizeze o adresă specifică de server proxy și nu necesită modificări pentru a funcționa cu un proxy fără inspecție.
-
Proxy transparent (inspecție) - Clienții nu sunt configurați să utilizeze o adresă specifică de server proxy. Nu sunt necesare modificări ale configurației HTTP; cu toate acestea, clienții dvs., fie că este vorba de aplicație, fie de dispozitive, au nevoie de un certificat rădăcină pentru a avea încredere în proxy. Echipa IT folosește proxy-urile de inspecție pentru a aplica politici privind site-urile web de vizitat și tipurile de conținut care nu sunt permise.
Configurați manual adresele proxy pentru dispozitivele Cisco și aplicația Webex folosind:
-
Sistem de operare platformă
-
Interfața dispozitivului
-
Descoperit automat folosind mecanisme Web Proxy, cum ar fi:
-
Descoperire automată a proxy-ului web (WPAD) - Protocol de descoperire automată a proxy-ului web
-
Fișiere de configurare automată proxy (PAC) - Fișiere de configurare automată proxy
-
În timp ce configurați tipurile de produse preferate, alegeți dintre următoarele configurații Proxy & tipuri de autentificare din tabel:
|
Produs |
Configurare proxy |
Tip de autentificare |
|---|---|---|
|
Webex pentru Mac |
Manuală, WPAD, PAC |
Fără autentificare, Basic, NTLM,† |
|
Webex pentru Windows |
Manuală, WPAD, PAC, GPO |
Fără autentificare, De bază, NTLM, †, Negociere † |
|
Webex pentru iOS |
Manuală, WPAD, PAC |
Fără autentif., de bază, de tip digest, NTLM |
|
Webex pentru Android |
Manuală, PAC |
Fără autentif., de bază, de tip digest, NTLM |
|
Webex Web App |
Acceptat prin sistemul de operare |
Fără autentificare, De bază, Digest, NTLM, Negociere † |
|
Dispozitive Webex |
WPAD, PAC sau manuală |
Fără autentif., de bază, de tip digest |
|
Telefoane IP Cisco |
Manuală, WPAD, PAC |
Fără autentif., de bază, de tip digest |
|
Webex Video Mesh Node |
Manual |
Fără autentif., de bază, de tip digest, NTLM |
Pentru legendele din tabel:
-
†Autentificare NTLM Mac - Nu este necesar ca mașina să fie conectată la domeniu, utilizatorul trebuie să introducă o parolă
-
†Autentificare Windows NTLM - Acceptată numai dacă o mașină este conectată la domeniu
-
Negociază †- Kerberos cu autentificare de rezervă NTLM.
-
Pentru a conecta un dispozitiv Cisco Webex Board, Desk sau Room Series la un server proxy, consultați Conectarea dispozitivului Board, Desk sau Room Series la un server proxy.
-
Pentru telefoanele IP Cisco, consultați Configurarea unui server proxy ca exemplu de configurare a serverului proxy și a setărilor.
Pentru No Authentication, configurați clientul cu o adresă proxy care nu acceptă autentificarea. Când utilizați Proxy Authentication, configurați cu acreditări valide. Proxy-urile care inspectează traficul web pot interfera cu conexiunile de soclu web. Dacă apare această problemă, ocolirea neinspecției traficului către *.Webex.com s-ar putea rezolva problema. Dacă vedeți deja alte intrări, adăugați punct și virgulă după ultima intrare, apoi introduceți excepția Webex.
Setări proxy pentru sistemul de operare Windows
Microsoft Windows acceptă două biblioteci de rețea pentru traficul HTTP (WinINet și WinHTTP) care permit configurarea proxy. WinINet este un superset al WinHTTP.
-
WinInet este conceput pentru aplicații client desktop cu un singur utilizator
-
WinHTTP este conceput în principal pentru aplicații multiutilizator, bazate pe server
Când selectați între cele două, alegeți WinINet pentru setările de configurare proxy. Pentru detalii, consultați wininet-vs-winhttp.
Consultați Configurați o listă de domenii permise pentru accesarea Webex în rețeaua corporativă pentru detalii despre următoarele:
-
Pentru a ne asigura că utilizatorii se conectează la aplicații doar folosind conturi dintr-o listă predefinită de domenii.
-
Utilizați un server proxy pentru a intercepta solicitările și a limita domeniile permise.
Inspecția proxy și fixarea certificatelor
Aplicația și dispozitivele Webex validează certificatele serverelor atunci când stabilesc sesiunile TLS. Verificările certificatelor, cum ar fi emitentul certificatului și semnătura digitală, se bazează pe verificarea lanțului de certificate până la certificatul rădăcină. Pentru a efectua verificările de validare, aplicația și dispozitivele Webex utilizează un set de certificate CA rădăcină de încredere instalate în depozitul de încredere al sistemului de operare.
Dacă ați implementat un proxy cu inspecție TLS pentru a intercepta, decripta și inspecta traficul de apeluri Webex. Asigurați-vă că certificatul prezentat de proxy (în loc de certificatul serviciului Webex) este semnat de o autoritate de certificare, iar certificatul rădăcină este instalat în depozitul de încredere al aplicației Webex sau al dispozitivului Webex.
-
Pentru aplicația Webex - Instalați certificatul CA utilizat pentru semnarea certificatului de către proxy în sistemul de operare al dispozitivului.
-
Pentru dispozitivele Webex Room și telefoanele IP multiplatformă Cisco - Deschideți o solicitare de service cu echipa TAC pentru a instala certificatul CA.
Acest tabel prezintă aplicația Webex și dispozitivele Webex care acceptă inspecția TLS de către serverele proxy
|
Produs |
Acceptă CA-uri de încredere personalizate pentru inspecția TLS |
|---|---|
|
Aplicația Webex (Windows, Mac, iOS, Android, Web) |
Da |
|
Dispozitive Webex Room |
Da |
|
Telefoane Cisco IP Multiplatform (MPP) |
Da |
Configurarea firewall-ului
Cisco oferă asistență pentru serviciile Webex Calling și Webex Aware în centrele de date securizate Cisco și Amazon Web Services (AWS). Amazon și-a rezervat subrețelele IP pentru uzul exclusiv al Cisco și a securizat serviciile situate în aceste subrețele în cadrul cloud-ului privat virtual AWS.
Configurați firewall-ul pentru a permite comunicarea dintre dispozitivele, aplicațiile aplicației și serviciile conectate la internet să își îndeplinească corect funcțiile. Această configurație permite accesul la toate serviciile cloud, numele de domeniu, adresele IP, porturile și protocoalele Webex Calling și Webex Aware acceptate.
Adăugați pe lista albă sau acces liber la următoarele, astfel încât serviciile Webex Calling și Webex Aware să funcționeze corect.
-
Cel/Cea/Cei/Cele URLs/Domains menționate în secțiunea Domeniile și adresele URL pentru Webex Calling Services și subrețelele IP, porturile și protocoalele enumerate în secțiunea Subrețelele IP pentru Webex Calling Services sunt utilizate în mai multe scopuri, inclusiv semnalizarea apelurilor, traficul media către și de la Webex Calling, sincronizarea Network Time Protocol (NTP) și testarea disponibilității rețelei CScan pentru acele subrețele IP.
-
Dacă organizația dvs. utilizează suita Webex de servicii de colaborare în cloud, inclusiv Webex Meetings, Messaging, Webex Attendant Console, conexiunea de peering prin rețea privată Webex Edge Connect la backbone-ul Webex și alte servicii conexe, asigurați-vă că subrețelele IP, domeniile și adresele URL specificate în articolele Cerințe de rețea pentru serviciile Webex, Webex Edge Connectși Cerințe de rețea pentru consola Attendant sunt permise prin rețeaua dvs. Acest lucru este necesar pentru a garanta conectivitatea și funcționalitatea corespunzătoare a acestor servicii Webex.
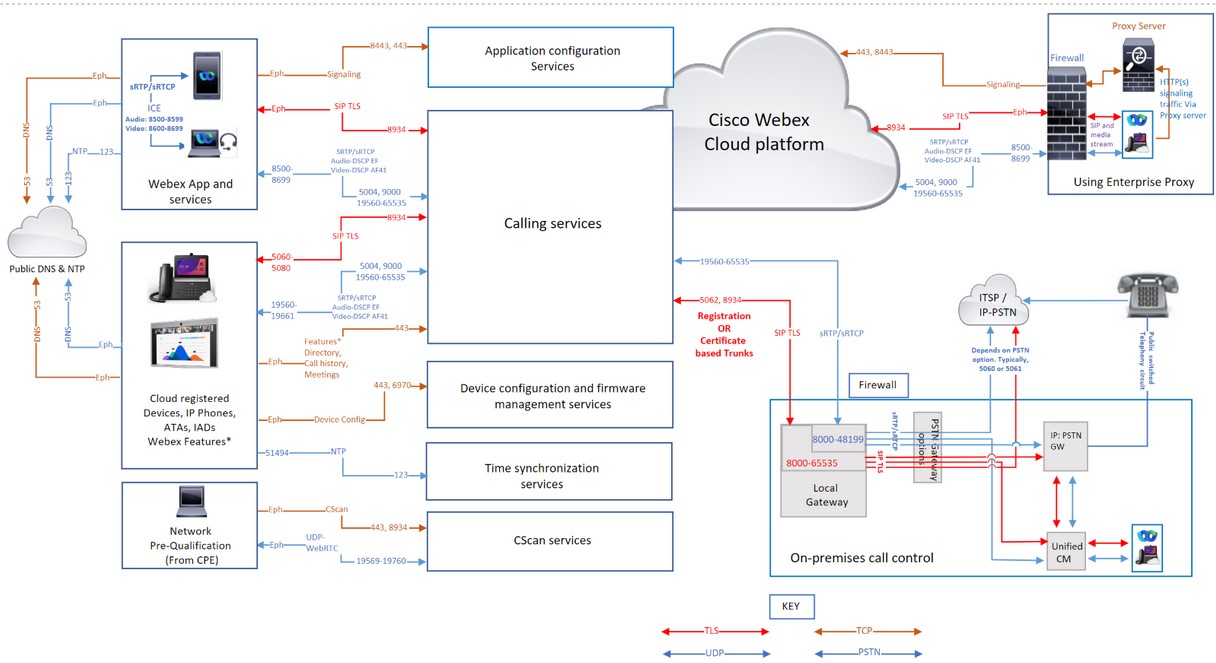
Traficul de apeluri Webex prin proxy-uri și firewall-uri
Dacă utilizați doar un firewall, filtrarea traficului Webex Calling folosind doar adrese IP nu este acceptată, deoarece unele dintre grupurile de adrese IP sunt dinamice și se pot modifica oricând. Cisco nu recomandă filtrarea unui subset de adrese IP în funcție de o anumită regiune geografică sau de un anumit furnizor de servicii cloud. Filtrarea după regiune poate cauza o degradare gravă a experienței de apelare.
Cisco nu întreține grupuri de adrese IP care se schimbă dinamic, prin urmare nu este listat în acest articol. Actualizați-vă regulile în mod regulat; neactualizarea listei de reguli pentru firewall ar putea afecta experiența utilizatorilor.
Dacă firewall-ul dvs. nu este compatibil Domain/URL filtrare, apoi utilizați o opțiune de server proxy Enterprise. Această opțiune filters/allows de URL/domain traficul de semnalizare HTTP către serviciile Webex Calling și Webex Aware din serverul proxy, înainte de a-l redirecționa către firewall.
În timp ce utilizați opțiunea serverului proxy al companiei pentru filtrare Domain/URLs, Rețineți că nu este conceput pentru a gestiona audio și video interactiv, ci doar pentru traficul de semnalizare HTTPS. Folosiți întotdeauna:
-
Filtrare bazată pe porturi și subrețea IP pentru semnalizarea apelurilor & Media
-
Domain/URL filtrarea este pentru traficul de semnalizare HTTP(s)
Pentru Webex Calling, UDP este protocolul de transport preferat de Cisco pentru media și recomandă utilizarea exclusivă a SRTP în locul UDP. TCP și TLS ca protocoale de transport pentru media nu sunt acceptate pentru Webex Calling în mediile de producție. Natura orientată pe conexiune a acestor protocoale afectează calitatea mediilor în cazul pierderilor de rețea. Dacă aveți întrebări legate de protocolul de transport, trimiteți un tichet de asistență.
Domenii și adrese URL pentru serviciile Webex Calling
O * afișat la începutul unei adrese URL (de exemplu, *.webex.com) indică faptul că serviciile din domeniul de nivel superior și din toate subdomeniile sunt accesibile.
|
Domeniu/URL |
Descriere |
Aplicațiile și dispozitive Webex care utilizează aceste domenii/URL-uri |
|---|---|---|
|
Serviciile Cisco Webex Calling și Webex Aware | ||
|
*.broadcloudpbx.com |
Microservicii de autorizare Webex pentru lansare încrucișată de la Control Hub la Portalul de administrare apelant. |
Control Hub |
|
*.broadcloud.com.au |
Servicii de apelare Webex în Australia. |
Toate |
|
*.broadcloud.eu |
Servicii de apelare Webex în Europa. |
Toate |
|
*.broadcloudpbx.net |
Apelarea serviciilor de configurare și gestionare a clienților. |
Webex Apps |
|
*.webex.com *.cisco.com |
Apeluri Webex de bază & Servicii Webex Aware
Când un telefon se conectează la o rețea pentru prima dată sau după o resetare la setările din fabrică fără opțiuni DHCP setate, acesta contactează un server de activare a dispozitivului pentru alocarea fără atingere. Telefoanele noi utilizează activate.cisco.com, iar telefoanele cu versiuni de firmware anterioare versiunii 11.2(1) continuă să utilizeze webapps.cisco.com pentru configurare. Descărcați firmware-ul dispozitivului și actualizările regionale de la binaries.webex.com. Permiteți telefoanelor Cisco Multiplatform (MPP) mai vechi de versiunea 12.0.3 să acceseze sudirenewal.cisco.com prin portul 80 pentru a reînnoi Certificatul instalat de producător (MIC) și pentru a avea un Identificator unic securizat de dispozitiv (SUDI). Pentru detalii, consultați Notificare de teren. Dacă nu utilizați un server proxy și utilizați doar un firewall pentru a filtra adresele URL, adăugați |
Toate |
|
*.ucmgmt.cisco.com |
Servicii de apelare Webex |
Control Hub |
|
*.wbx2.com și *.ciscospark.com |
Folosit pentru conștientizarea cloud-ului pentru a contacta Webex Calling & Servicii Webex Aware în timpul și după integrare. Aceste servicii sunt necesare pentru
|
Toate |
|
*.webexapis.com |
Microservicii Webex care gestionează aplicațiile Webex App și dispozitivele Webex.
|
Toate |
|
*.webexcontent.com |
Serviciile de mesagerie Webex legate de stocarea generală a fișierelor, inclusiv:
|
Servicii de mesagerie Webex Apps. Stocarea fișierelor folosind webexcontent.com a fost înlocuită de clouddrive.com în octombrie 2019 |
|
*.accompany.com |
Integrarea informațiilor despre oameni |
Aplicațiile Webex |
|
Servicii Webex suplimentare (Domenii terțe) | ||
|
*.appdynamics.com *.eum-appdynamics.com |
Urmărirea performanței, captarea erorilor și a blocărilor, valorile sesiunii. |
Aplicația Webex, aplicația web Webex |
|
*.sipflash.com |
Servicii de gestionare a dispozitivelor. Actualizări de firmware și scopuri de integrare securizată. |
Webex Apps |
|
*.walkme.com *.walkmeusercontent.com |
Client de orientare a utilizatorilor Webex. Oferă tururi de onboarding și utilizare pentru utilizatorii noi. Pentru mai multe informații despre WalkMe, faceți clic aici. |
Webex Apps |
|
*.google.com *.googleapis.com |
Notificări către aplicațiile Webex pe dispozitivele mobile (Exemplu: mesaj nou, când se răspunde la apel) Pentru subrețele IP, consultați aceste linkuri Serviciul Google Firebase Cloud Messaging (FCM) Serviciul de notificări push Apple (APNS) Pentru APNS, Apple listează subrețelele IP pentru acest serviciu. | Aplicația Webex |
|
api.wxc.e911cloud.com wxc.e911cloud.com |
Integrarea serviciului de urgență 911 (E911) (RedSky) cu Webex Calling Telefonul și clientul Webex comunică cu serviciul RedSky utilizând portul 443 Consultați articolul Integrarea serviciului e911 cu Webex Calling pentru detalii. |
Aplicația Webex, Dispozitive |
|
*.quovadisglobal.com *.digicert.com *.identrust.com *.godaddy.com |
Această funcție este utilizată pentru a verifica „Lista de certificate revocate” pentru certificatele de securitate. Lista de revocare a certificatelor garantează că niciun certificat compromis nu poate fi utilizat pentru a intercepta traficul Webex securizat care are loc pe portul TCP 80. Webex Calling acceptă atât capsarea CRL, cât și cea OCSP pentru a determina starea revocării certificatelor. Deși capsarea OCSP reduce necesitatea ca aplicația Webex să contacteze autoritățile de certificare, dispozitivele pot contacta în continuare direct autoritățile de certificare. Acest proces validează identitatea hardware-ului, efectuează autentificarea rețelei 802.1X sau descarcă CRL-uri dacă un răspuns capsat nu este disponibil sau este nevalid. | Toate |
Subrețele IP pentru serviciile de apelare Webex
Semnalizare HTTPS - Stabilirea sesiunii pentru serviciile Webex Calling și Webex Aware se bazează pe adrese URL și nu pe adrese IP. Reţea firewalls/proxies trebuie să permită accesul la Domains/URLs de asemenea, nu doar intervalul IP.
|
Subrețele IP pentru serviciile Webex Calling*† | ||
|---|---|---|
|
(1) Semnalizare apeluri, Media, NTP & CScan | ||
|
23.89.0.0/16 |
62.109.192.0/18 |
85.119.56.0/23 |
|
128.177.14.0/24 |
128.177.36.0/24 |
135.84.168.0/21 |
|
139.177.64.0/21 |
139.177.72.0/23 |
144.196.0.0/16 |
|
150.253.128.0/17 |
163.129.0.0/17 |
170.72.0.0/16 |
|
170.133.128.0/18 |
185.115.196.0/22 |
199.19.196.0/23 |
|
199.19.199.0/24 |
199.59.64.0/21 | |
|
(2) Configurarea dispozitivelor și gestionarea firmware-ului (dispozitive Cisco) | ||
|
3.14.211.49 |
3.20.185.219 |
3.130.87.169 |
|
3.134.166.179 |
52.26.82.54 |
62.109.192.0/18 |
|
72.163.10.96/27 |
72.163.15.64/26 |
72.163.15.128/26 |
|
72.163.24.0/23 |
72.163.10.128/25 |
173.37.146.128/25 |
|
173.36.127.0/26 |
173.36.127.128/26 |
173.37.26.0/23 |
|
173.37.149.96/27 |
192.133.220.0/26 |
192.133.220.64/26 |
|
(3) Configurarea aplicației Webex | ||
|
62.109.192.0/18 |
64.68.96.0/19 |
150.253.128.0/17 |
|
207.182.160.0/19 | ||
|
Scopul conexiunii | Adrese sursă | Porturi sursă | Protocol | Adrese de destinație | Porturi de destinație | Note | |
|---|---|---|---|---|---|---|---|
| Semnalizarea apelurilor către Webex Calling (SIP TLS) | Local Gateway extern (NIC) | 8000-65535 | TCP | Consultați Subrețele IP pentru serviciile de apelare Webex (1). | 5062, 8934 |
Aceste IPs/ports sunt necesare pentru semnalizarea apelurilor SIP-TLS de ieșire de la gateway-uri locale, dispozitive și aplicații Webex (sursă) către Webex Calling Cloud (destinație). Portul 5062 (obligatoriu pentru trunchiul bazat pe certificat). Și portul 8934 (necesar pentru trunchiul bazat pe înregistrare) | |
| Dispozitive | 5060-5080 | 8934 | |||||
| Seria Room | De scurtă durată | ||||||
| Aplicația Webex | Efemer (OS dependent) | ||||||
| Semnalizarea apelurilor de la Webex Calling (SIP TLS) către gateway-ul local |
Interval de adrese de apelare Webex. ConsultațiSubrețele IP pentru serviciile de apelare Webex (1) | 8934 | TCP | IP sau intervale IP alese de client pentru gateway-ul local | Port sau interval de porturi ales de client pentru gateway-ul local |
Se aplică gateway-urilor locale bazate pe certificate. Este necesar să se stabilească o conexiune de la Webex Calling la un gateway local. Un gateway local bazat pe înregistrare funcționează pe reutilizarea unei conexiuni create de gateway-ul local. Portul de destinație este ales de client Configurați trunchiurile | |
| Apelați media către Webex Calling (STUN, SRTP/SRTCP, T38, DTLS) | Local Gateway NIC extern | 8000-48199†* | UDP | Consultați Subrețele IP pentru serviciile de apelare Webex (1). |
5004, 9000, 8500—8699, 19560—65535 (SRTP prin UDP) |
| |
| Dispozitive†* | 19560-19661 | ||||||
| Seria Room†* | Audio 52050-52099 Video52200-52299 | ||||||
|
Dispozitive VG400 ATA | 19560-19849 | ||||||
| Aplicația Webex†* |
Audio: 8500-8599 Video: 8600-8699 | ||||||
|
WebRTC | Efemer (Conform politicii browserului) | ||||||
| Apel media de la Webex Calling (SRTP/SRTCP, T38) |
Interval de adrese de apelare Webex. ConsultațiSubrețele IP pentru serviciile de apelare Webex (1) | 19560-65535 (SRTP prin UDP) | UDP | IP sau interval IP ales de client pentru gateway-ul local | Intervalul de porturi media ales de client pentru gateway-ul local |
Se aplică gateway-urilor locale bazate pe certificate | |
| Semnalizarea apelurilor către gateway-ul PSTN (SIP TLS) | NIC intern al Gateway-ului local | 8000-65535 | TCP | ITSP PSTN GW sau UNIFIED CM | Depinde de pstn opțiune (de exemplu, de obicei, 5060 sau 5061 pentru UNIFIED CM) | ||
| Apelați media către gateway-ul PSTN (SRTP/SRTCP) | NIC intern al Gateway-ului local | 8000-48199†* | UDP | ITSP PSTN GW sau UNIFIED CM | Depinde de opțiunea PSTN (de exemplu, de obicei 5060 sau 5061 pentru Unified CM) | ||
| Configurarea dispozitivului și gestionarea firmware-ului (dispozitive Cisco) | Dispozitive de apelare Webex | De scurtă durată | TCP |
ConsultațiSubrețele IP pentru serviciile de apelare Webex (2) | 443, 6970, 80 |
Necesar din următoarele motive:
| |
| Configurarea aplicației Webex | Aplicații Webex App | De scurtă durată | TCP |
ConsultațiSubrețele IP pentru serviciile de apelare Webex (3) | 443, 8443 | Folosit pentru autentificarea brokerului de ID-uri, serviciile de configurare a aplicației Webex pentru clienți, accesul web bazat pe browser pentru autoservire ȘI accesul la interfața administrativă. Portul TCP 8443 este utilizat de aplicația Webex în configurația Cisco Unified CM pentru descărcarea configurației. Doar clienții care utilizează configurarea pentru a se conecta la Webex Calling trebuie să deschidă portul. | |
| Sincronizarea timpului dispozitivului (NTP) | Dispozitive de apelare Webex | De scurtă durată | UDP | Consultați Subrețele IP pentru serviciile de apelare Webex (1). | 123 †* | Aceste adrese IP sunt necesare pentru sincronizarea timpului pentru dispozitive (telefoane MPP, ATA-uri și ATA-uri SPA) | |
|
Rezoluția sistemului de nume de domeniu (DNS) | Dispozitive Webex Calling, aplicația Webex și dispozitivele Webex | De scurtă durată | UDP și TCP | Definit de gazdă | 53†* | Folosit pentru căutări DNS pentru a descoperi adresele IP ale serviciilor Webex Calling în cloud. Chiar dacă căutările DNS tipice se fac prin UDP, unele pot necesita TCP, dacă răspunsurile la interogare nu le pot încăpea în pachetele UDP. | |
| Protocol de timp de rețea (NTP- Network Time Protocol) | Aplicația Webex și dispozitivele Webex | 123 | UDP | Definit de gazdă | 123 | Sincronizarea timpului | |
| CScan | Instrument de precalificare pentru Webex Calling, disponibilitatea pentru rețeaua web | De scurtă durată | TCP | Consultați Subrețele IP pentru serviciile de apelare Webex (1). | 8934 și 443 | Instrument de precalificare pentru pregătirea rețelei bazat pe web pentru Webex Calling. Accesați cscan.webex.com pentru mai multe informații. | |
| UDP | 19569-19760 | ||||||
| Apeluri Webex suplimentare & Servicii Webex Aware (Terțe) | |||||||
| Notificări push, servicii APNS și FCM | Aplicații Webex Calling | De scurtă durată | TCP |
Consultați subrețelele IP menționate sub linkuri | 443, 2197, 5228, 5229, 5230, 5223 | Notificări către aplicațiile Webex pe dispozitivele mobile (Exemplu: Când primiți un mesaj nou sau când se răspunde la un apel) | |
-
†* Intervalul de porturi media ale gateway-ului local este configurabil cu interval-port-rtp.
-
†* Porturi media pentru dispozitive și aplicații care sunt atribuite dinamic în intervalelede porturi SRTP. Porturile SRTP sunt porturi cu numerotare pară, iar portului SRTCP corespunzător i se alocă portul cu numerotare impară consecutivă.
-
Dacă este configurată o adresă de server proxy pentru aplicațiile și dispozitivele dvs., traficul de semnalizare este trimis către proxy. Fișierele media transportate SRTP prin UDP curg direct către firewall în loc de serverul proxy.
-
Dacă utilizați servicii NTP și DNS în rețeaua companiei dvs., trebuie să permiteți în continuare DNS de ieșire (UDP/TCP 53) și trafic NTP (UDP 123) prin firewall-ul dvs. pentru serviciile Webex Calling și Webex Aware. În timp ce DNS-ul intern gestionează căutările locale, pentru serviciile Webex, dispozitivele și aplicațiile trebuie să rezolve FQDN-urile de servicii externe și înregistrările SRV. Dispozitive precum telefoanele IP ajung adesea la serverele NTP publice sau la serverele de timp proprii ale Webex Calling pentru a-și menține ceasurile interne sincronizate, ceea ce este esențial pentru securitatea și înregistrarea apelurilor.
Dimensiunea MTU pentru Webex Calling & Servicii Webex Aware
Unitatea Maximă Transmisibilă (MTU) este cea mai mare dimensiune pe care un pachet IP o poate transmite printr-o legătură de rețea fără a fi nevoie de fragmentare. Pot apărea probleme dacă MTU-ul nu este setat la valorile implicite. Webex Calling recomandă menținerea dimensiunii MTU implicite de 1500 de octeți pentru toate pachetele IP din rețeaua dvs.
Pentru serviciile Webex Calling și Webex Aware, dacă un pachet necesită fragmentare, setați bitul Don't Fragment (DF) pentru a necesita comunicarea ICMP.
Calitatea serviciilor (QoS)/Type Termeni și condiții de serviciu (Termeni și condiții)
Vă permite să activați etichetarea pachetelor de la dispozitivul sau clientul local către platforma cloud Webex Calling. QoS vă permite să prioritizați traficul în timp real față de alt trafic de date. Activarea acestei setări modifică marcajele QoS pentru aplicațiile și dispozitivele care utilizează semnalizare SIP și media.
| Adrese sursă | Tipul de trafic | Adrese de destinație | Porturi sursă | Porturi de destinație | Clasa și valoarea DSCP |
|---|---|---|---|---|---|
| Aplicația Webex | Audio |
Referiți subrețele IP, domenii și adrese URL pentru serviciile Webex Calling | 8500-8599 | 8500-8599, 19560-65535 | Expediere rapidă (46) |
| Aplicația Webex | Video | 8600-8699 | 8600-8699, 19560-65535 | Expediere garantată 41 (34) | |
| Aplicația Webex | Semnalizare | Efemer (OS dependent) | 8934 | CS0 (0) | |
| Dispozitive Webex (MPP-uri și camere) | Audio și video | 19560-19661 | 19560-65535 |
Expediere rapidă (46) & Expediere garantată 41 (34) | |
| Dispozitive Webex | Semnalizare | 5060-5080 | 8934 | Selector de clasă 3 (24) |
-
Creați un profil QoS separat pentru Audio și Video/Share deoarece au un interval de porturi sursă diferit pentru a marca traficul diferit.
-
Pentru clienții Windows: Pentru a activa diferențierea porturilor sursă UDP pentru organizația dvs., contactați echipa locală de cont. Fără activare, nu puteți face diferența între sunet și Video/Share utilizând politicile Windows QoS (GPO) deoarece porturile sursă sunt aceleași pentru audio/video/share. Pentru detalii, consultați Activarea intervalelor de porturi sursă media pentru aplicația Webex
-
Pentru dispozitivele Webex, configurați modificările setărilor QoS din setările dispozitivului Control Hub. Pentru detalii, consultați Configurare & modificarea setărilor dispozitivului în Webex-Calling
Webex Meetings/Messaging - Cerințe de rețea
Pentru clienții care utilizează Webex Suite de servicii de colaborare în cloud, produsele înregistrate în cloud Webex, integrați dispozitivele MPP în Webex Cloud pentru servicii precum Istoricul apelurilor, Căutarea în director, Întâlniri și Mesagerie. Asigurați-vă că Domains/URLs/IP Addresses/Ports menționate în acest articol sunt deschise Cerințe de rețea pentru serviciile Webex.
Cerințe de rețea pentru Webex for Government
Pentru clienții care au nevoie de lista de domenii, adrese URL, intervale de adrese IP și porturi pentru serviciile Webex for Government, informațiile pot fi găsite aici: Cerințe de rețea pentru Webex for Government
Cerințe de rețea pentru Webex Attendant Console
Pentru clienții care utilizează consola participantului - recepționeri, participanți și operatori, asigurați-vă Domains/URLs/IP Addresses/Ports/Protocols sunt deschise Cerințe de rețea pentru consola participantului
Introducere în Webex Calling Local Gateway
Pentru clienții care utilizează soluția Local Gateway cu Webex Calling pentru interoperabilitate PSTN bazată pe sediul companiei și SBC-uri terțe, citiți articolul Introducere în Local Gateway
Referințe
Pentru a afla noutățile din Webex Calling, consultați Noutățile din Webex Calling
Pentru cerințele de securitate pentru Webex Calling, consultați articolul
Optimizarea media pentru apeluri Webex cu Interactive Connectivity Establishment (ICE) Articol
Istoricul reviziilor documentelor
|
Dată |
Am făcut următoarele modificări acestui articol |
|---|---|
|
28 martie 2026 |
Am actualizat linkul către documentația Firebase Cloud Messaging (FCM). |
|
4 martie 2026 |
Portul sursă pentru sincronizarea orei dispozitivului (NTP) a fost modificat de la 51494 la Efemer în secțiunea Subrețele IP pentru serviciile de apelare Webex. |
|
23 februarie 2026 |
Scopul detaliilor conexiunii este actualizat în subrețeaua IP pentru Webex Calling Următoarele adrese URL suplimentare de la terți sunt incluse:
Actualizări editoriale pentru a îmbunătăți articolul și a facilita citirea acestuia |
|
5 decembrie 2025 |
A fost adăugată utilizarea subrețelelor IP, porturilor și protocoalelor listate în secțiunea Subrețele IP pentru serviciile de apelare Webex. |
|
24 octombrie 2025 |
Calitatea imaginii a fost îmbunătățită și linkul nefuncțional către serviciul Google Firebase Cloud Messaging (FCM) a fost remediat. |
|
15 septembrie 2025 |
|
|
10 aprilie 2025 |
Text inclus pentru a evidenția dimensiunea MTU pentru serviciile Webex Calling și Webex Aware |
|
27 martie 2025 |
Subrețeaua IP actualizată pentru serviciile de apelare Webex 62.109.192.0/18 pentru a face față extinderii pieței Webex Calling în regiunea Arabiei Saudite. |
|
21 ianuarie 2025 |
Au fost adăugate detalii pentru utilizarea SIP Application Layer Gateway. |
|
8 ianuarie 2025 |
Adresa de subrețea IP aferentă configurației dispozitivului și configurației aplicației Webex a fost mutată în secțiunea Subrețele IP pentru serviciile de apelare Webex |
|
17 decembrie 2024 |
S-a adăugat suport pentru WebRTC pentru specificația Webex Calling Media. |
|
14 noiembrie 2024 |
A fost actualizat intervalul de porturi acceptate pentru apelurile media Webex Calling pentru dispozitivul ATA din seria VG400. |
|
11 noiembrie 2024 |
Adăugat intervalul de porturi acceptat pentru apelurile media Webex Calling pentru dispozitivul ATA din seria VG400 |
|
25 iulie 2024 |
A fost readăugată subrețeaua IP 52.26.82.54, deoarece este necesară pentru configurarea dispozitivelor Cisco ATA și gestionarea firmware-ului. |
|
18 iulie 2024 |
Actualizat cu următoarele detalii:
|
|
28 iunie 2024 |
A fost actualizată utilizarea ambelor intervale de porturi SRTP/SRTCP pentru specificația Webex Calling Media. |
|
11 iunie 2024 |
Domeniul „huron-dev.com” a fost eliminat deoarece nu este utilizat. |
|
6 mai 2024 |
A fost actualizată utilizarea ambelor intervale de porturi SRTP/SRTCP pentru specificația Webex Calling Media. |
|
3 aprilie 2024 | Subrețelele IP pentru serviciile Webex Calling au fost actualizate cu 163.129.0.0/17 pentru a face față extinderii pieței Webex Calling în regiunea Indiei. |
|
18 decembrie 2023 |
A inclus cerința URL-ului sudirenewal.cisco.com și a portului 80 pentru configurarea dispozitivului și gestionarea firmware-ului pentru reînnoirea MIC-ului telefonului Cisco MPP. |
|
11 decembrie 2023 |
Subrețelele IP pentru serviciile Webex Calling au fost actualizate pentru a include un set mai mare de adrese IP. 150.253.209.128/25 – s-a schimbat în 150.253.128.0/17 |
|
29 noiembrie 2023 |
Subrețelele IP pentru serviciile Webex Calling au fost actualizate pentru a include un set mai mare de adrese IP, pentru a permite extinderea regiunii Webex Calling pentru creșterea viitoare. 144.196.33.0/25 – s-a schimbat în 144.196.0.0/16 Secțiunile Subrețele IP pentru serviciile Webex Calling din Webex Calling (SIP TLS) și Media apel către Webex Calling (STUN, SRTP) au fost actualizate pentru clarificarea trunking-ului bazat pe certificate și a cerințelor firewall pentru Local Gateway. |
|
14 august 2023 |
Am adăugat următoarele adrese IP 144.196.33.0/25 şi 150.253.156.128/25 pentru a susține cerințele crescute de capacitate pentru serviciile de apelare Edge și Webex. Acest interval IP este acceptat numai în regiunea SUA. |
|
5 iulie 2023 |
Am adăugat linkul https://binaries.webex.com pentru instalarea firmware-ului Cisco MPP. |
|
7 martie 2023 |
Am revizuit întregul articol pentru a include:
|
|
martie 5, 2023 |
Actualizarea articolului pentru a include următoarele:
|
|
15 noiembrie 2022 |
Am adăugat următoarele adrese IP pentru configurarea dispozitivelor și gestionarea firmware-ului (dispozitive Cisco):
Am eliminat următoarele adrese IP din configurația dispozitivelor și din gestionarea firmware-ului (dispozitive Cisco):
|
|
14 noiembrie 2022 |
Adăugată subrețeaua IP 170.72.242.0/24 pentru serviciul Webex Calling. |
|
Septembrie 08, 2022 |
Firmware-ul Cisco MPP trece la utilizarea https://binaries.webex.com ca adresă URL gazdă pentru actualizările de firmware MPP în toate regiunile. Această modificare îmbunătățește performanța de actualizare a firmware-ului. |
|
august 30, 2022 |
A fost eliminată referința la Portul 80 din Configurarea dispozitivului și gestionarea firmware-ului (dispozitive Cisco), Configurarea aplicației și rândurile CScan din tabelul Port, deoarece nu există dependențe. |
|
august 18, 2022 |
Nici o schimbare în soluție. S-au actualizat porturile de destinație 5062 (necesare pentru trunchiul bazat pe certificat), 8934 (necesare pentru trunchiul bazat pe înregistrare) pentru semnalizarea apelurilor către Webex Calling (SIP TLS). |
|
iulie 26, 2022 |
Adăugat 54.68.1.225 Adresa IP, care este necesar pentru actualizarea firmware-ului de Cisco 840/860 dispozitive. |
|
iulie 21, 2022 |
S-au actualizat porturile de destinație 5062, 8934 pentru semnalizarea apelurilor către Webex Calling (SIP TLS). |
|
iulie 14, 2022 |
Au fost adăugate adresele URL care acceptă o funcție completă a serviciilor Webex Aware. Adăugată subrețeaua IP 23.89.154.0/25 pentru serviciul Webex Calling. |
|
iunie 27, 2022 |
S-au actualizat domeniul și adresele URL pentru serviciile de apelare Webex: *.broadcloudpbx.com *.broadcloud.com.au *.broadcloud.eu *.broadcloudpbx.net |
|
iunie 15, 2022 |
S-au adăugat următoarele porturi și protocoale sub Adrese IP și porturi pentru serviciilede apelare Webex:
Informații actualizate în Webex Meetings/Messaging - Secțiunea Cerințe de rețea |
|
Mai 24, 2022 |
S-a adăugat subrețeaua IP 52.26.82.54/24 la 52.26.82.54/32 pentru serviciul Webex Calling |
|
Mai 6, 2022 |
S-a adăugat subrețeaua IP 52.26.82.54/24 pentru serviciul Webex Calling |
|
Aprilie 7, 2022 |
Intervalul de porturi UDP interne și externe ale Local Gateway a fost actualizat la 8000-48198† |
|
Aprilie 5, 2022 |
S-au adăugat următoarele subrețele IP pentru serviciul Webex Calling:
|
|
martie 29, 2022 |
S-au adăugat următoarele subrețele IP pentru serviciul Webex Calling:
|
|
Septembrie 20, 2021 |
Au fost adăugate 4 subrețele IP noi pentru serviciul Webex Calling:
|
|
Aprilie 2, 2021 |
Adăugat *.ciscospark.com sub Domenii și adrese URL pentru serviciile Webex Calling pentru a oferi asistență în cazurile de utilizare Webex Calling în aplicația Webex. |
|
25 martie 2021 |
Au fost adăugate 6 noi intervale IP pentru activate.cisco.com, începând cu 8 mai 2021.
|
|
martie 4, 2021 |
A înlocuit IP-urile discrete Webex Calling și intervalele IP mai mici cu intervale simplificate într-un tabel separat pentru a facilita înțelegerea configurației firewall-ului. |
|
februarie 26, 2021 |
S-a adăugat 5004 ca port de destinație pentru Call media la Webex Calling (STUN, SRTP) pentru a accepta Interactive Connectivity Establishment (ICE) care va fi disponibil în Webex Calling în aprilie 2021. |
|
februarie 22, 2021 |
Domeniile și adresele URL sunt acum listate într-un tabel separat. Tabelele Adrese IP și Porturi sunt ajustate pentru a grupa adrese IP pentru aceleași servicii. Adăugarea coloanei Note la tabelul Adrese IP și Porturi ajută la înțelegerea cerințelor. Mutarea următoarelor adrese IP în intervale simplificate pentru configurarea dispozitivelor și gestionarea firmware-ului (dispozitive Cisco):
Adăugarea următoarelor adrese IP pentru Configurarea aplicației, deoarece clientul Cisco Webex indică un SRV DNS mai nou în Australia în martie 2021.
|
|
ianuarie 21, 2021 |
Am adăugat următoarele adrese IP la configurația dispozitivelor și la gestionarea firmware-ului (dispozitive Cisco):
Am eliminat următoarele adrese IP din configurația dispozitivelor și din gestionarea firmware-ului (dispozitive Cisco):
Am adăugat următoarele adrese IP la configurația aplicației:
Am eliminat următoarele adrese IP din configurația aplicației:
Am eliminat următoarele numere de port din configurația aplicației:
Am adăugat următoarele domenii la configurația aplicației:
|
|
decembrie 23, 2020 |
S-au adăugat noi adrese IP de configurare a aplicațiilor la imaginile de referință ale portului. |
|
decembrie 22, 2020 |
Actualizat rândul Configurare aplicație în tabele pentru a include următoarele adrese IP: 135.84.171.154 și 135.84.172.154. Ascundeți diagramele de rețea până când sunt adăugate aceste adrese IP. |
|
decembrie 11, 2020 |
S-au actualizat configurația dispozitivului și gestionarea firmware-ului (dispozitive Cisco) și rândurile de configurare a aplicației pentru domeniile canadiene acceptate. |
|
Octombrie 16, 2020 |
S-a actualizat semnalizarea apelurilor și intrările media cu următoarele adrese IP:
|
|
Septembrie 23, 2020 |
Conform CScan, s-a înlocuit 199.59.64.156 cu 199.59.64.197. |
|
august 14, 2020 |
S-au adăugat mai multe adrese IP pentru a sprijini introducerea centrelor de date în Canada: Semnalizarea apelurilor către Webex Calling (SIP TLS) — 135.84.173.0/25,135.84.174.0/25, 199.19.197.0/24, 199.19.199.0/24 |
|
august 12, 2020 |
S-au adăugat mai multe adrese IP pentru a sprijini introducerea centrelor de date în Canada:
|
|
iulie 22, 2020 |
Adăugat următoarea adresă IP pentru a sprijini introducerea de centre de date în Canada: 135.84.173.146 |
|
iunie 9, 2020 |
Am făcut următoarele modificări la intrarea CScan:
|
|
martie 11, 2020 |
Am adăugat următoarele domenii și adrese IP la configurația aplicației:
Am actualizat următoarele domenii cu adrese IP suplimentare pentru configurarea dispozitivului și gestionarea firmware-ului:
|
|
februarie 27, 2020 |
Am adăugat următorul domeniu și porturi la configurarea dispozitivului și gestionarea firmware-ului: cloudupgrader.webex.com—443, 6970 |


