- 主页
- /
- 文章


适用于 Webex Calling 的端口参考信息
 在此文章中
在此文章中 反馈?
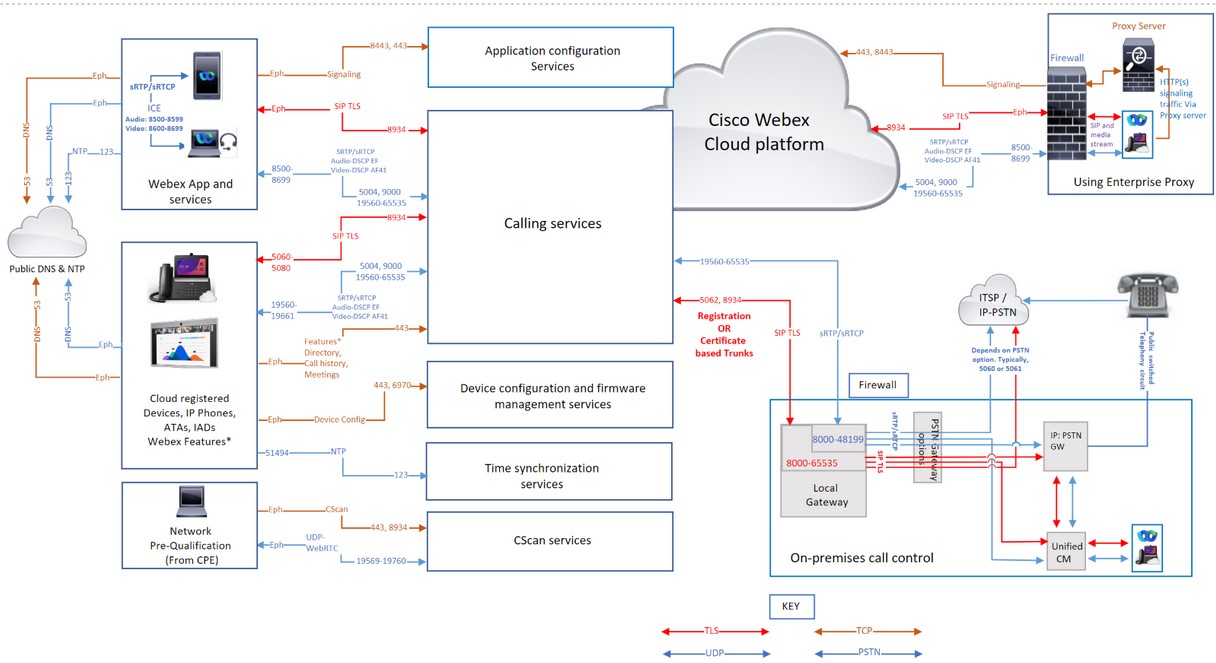
反馈?本文面向网络管理员,特别是组织内使用 Webex Calling 服务的防火墙和代理安全管理员。它描述了网络要求,并列出了用于连接您的电话、Webex 应用和网关到 Webex 通话服务的地址、端口和协议。
正确配置防火墙和代理是成功部署呼叫功能的关键。Webex Calling 使用 SIP 和 HTTPS 进行呼叫信令,并使用相关的地址和端口进行媒体、网络连接和网关连接,因为 Webex Calling 是一项全球服务。
并非所有防火墙配置都需要开放端口。但是,如果您运行的是内部到外部的规则,则必须为所需的协议打开端口才能释放服务。
网络地址转换(NAT)
网络地址转换 (NAT) 和端口地址转换 (PAT) 功能应用于两个网络之间的边界,以转换地址空间或防止 IP 地址空间冲突。
组织使用防火墙和代理等网关技术提供 NAT 或 PAT 服务,以便为位于私有 IP 地址空间中的 Webex App 应用程序或 Webex 设备提供互联网访问。这些网关使内部应用程序或设备到互联网的流量看起来像是来自一个或多个可公开路由的 IP 地址。
-
如果部署 NAT,则无需在防火墙上打开入站端口。
-
当多个应用用户和设备访问 Webex Calling 时,验证应用或设备连接所需的 NAT 池大小。 & 使用 NAT 或 PAT 的 Webex 感知服务。确保为 NAT 地址池分配足够的公网 IP 地址,以防止端口耗尽。端口耗尽会导致内部用户和设备无法连接到 Webex Calling 和 Webex Aware 服务。
-
定义合理的绑定周期,避免在 NAT 设备上操纵 SIP。
-
配置最小 NAT 超时时间,以确保设备正常运行。例如:Cisco 电话每隔 1-2 分钟发送一次后续的 REGISTER 刷新消息。
-
如果您的网络实现了 NAT 或 SPI,则应为连接设置更大的超时时间(至少 30 分钟)。此超时机制可在保证连接可靠性的同时,降低用户移动设备的电池消耗。
SIP应用层网关
如果路由器或防火墙支持 SIP,意味着启用了 SIP 应用层网关 (ALG) 或类似功能,我们建议您关闭此功能以确保服务的正常运行。尽管所有 Webex Calling 流量都经过加密,但某些 SIP ALG 实现可能会导致防火墙穿透问题。因此,我们建议关闭 SIP ALG 以确保高质量的服务。
请查阅相关制造商的文档,了解在特定设备上禁用 SIP ALG 的步骤。
Webex Calling 的代理支持
组织部署互联网防火墙或互联网代理和防火墙,以检查、限制和控制进出其网络的 HTTP 流量。从而保护他们的网络免受各种形式的网络攻击。
企业通常将代理服务器配置为将基于 HTTP 的互联网流量转发到企业防火墙的唯一途径。此配置使防火墙能够限制出站互联网流量,仅允许来自代理服务器的流量。
代理服务器执行多种安全功能,例如:
-
允许或阻止访问特定网址。
-
用户身份验证
-
IP address/domain/hostname/URI 信誉查询
-
流量解密和检查
配置代理功能后,它将应用于所有使用 HTTP 协议的应用程序。
Webex 应用和 Webex 设备应用包括以下内容:
-
Webex 服务
-
使用思科云配置平台(例如 GDS、EDOS 设备激活、配置)的客户设备激活 (CDA) 流程 & Webex云平台入门指南。
-
证书认证
-
固件升级
-
状态报告
-
PRT 上传
-
XSI 服务
除非这些准则允许,否则请勿更改或删除通过代理或防火墙传输的 HTTP 标头值 altering-header-values。按照这些准则修改或删除 HTTP 标头可能会影响对 Webex Calling 和 Webex-Aware 服务的访问,并可能导致 Webex 应用和设备失去访问权限。
如果配置了代理服务器地址,则只有信令流量。 (HTTP/HTTPS) 发送到代理服务器。使用 SIP 注册 Webex Calling 服务的客户端及其相关媒体不会发送到代理服务器。因此,允许这些客户端直接通过防火墙。
支持的代理选项和配置 & 身份验证类型
支持的代理类型有:
-
显式代理(检查或非检查)—配置客户端(应用程序或设备)的显式代理,以指定要使用的服务器。
-
透明代理(非检查型)—客户端未配置为使用特定的代理服务器地址,并且无需任何更改即可与非检查型代理一起工作。
-
透明代理(检查中)—客户端未配置为使用特定的代理服务器地址。无需更改 HTTP 的任何配置;但是,您的客户端(应用程序或设备)需要根证书,以便它们信任代理。IT 团队使用检查代理来强制执行对可访问网站和不允许访问的内容类型的策略。
使用以下命令手动配置 Cisco 设备和 Webex 应用的代理地址:
-
平台操作系统
-
设备用户界面
-
通过 Web 代理机制自动发现,例如:
-
Web代理自动发现(WPAD) - Web代理自动发现协议
-
代理自动配置 (PAC) 文件 - 代理自动配置文件
-
在配置您首选的产品类型时,请从以下代理配置中进行选择。 & 表格中的身份验证类型:
|
产品 |
代理配置 |
验证类型 |
|---|---|---|
|
Mac 版 Webex |
手动、WPAD、PAC |
无需身份验证、基本身份验证、NTLM 身份验证、† |
|
Windows 版 Webex |
手动、WPAD、PAC、GPO |
无身份验证、基本身份验证、NTLM 身份验证、 协商身份验证、协商身份验证。 |
|
iOS 版 Webex |
手动、WPAD、PAC |
不验证、基本、摘要、NTLM |
|
Android 版 Webex |
手动、PAC |
不验证、基本、摘要、NTLM |
|
Webex Web 应用程序 |
操作系统支持 |
无身份验证、基本身份验证、摘要式身份验证、NTLM 身份验证、协商身份验证 † |
|
Webex 设备 |
WPAD、PAC 或手动 |
不验证、基本、摘要 |
|
Cisco IP 电话 |
手动、WPAD、PAC |
不验证、基本、摘要 |
|
Webex 视频网格节点 |
手动 |
不验证、基本、摘要、NTLM |
表格中的图例:
-
†Mac NTLM 身份验证 - 计算机无需登录域,系统会提示用户输入密码
-
†Windows NTLM 身份验证 - 仅当计算机登录到域时才受支持
-
协商 †- Kerberos 与 NTLM 回退认证。
-
要将 Cisco Webex Board、Desk 或 Room 系列设备连接到代理服务器,请参阅 将 Board、Desk 或 Room 系列设备连接到代理服务器。
-
对于 Cisco IP 电话,请参阅 设置代理服务器 作为配置代理服务器和设置的示例。
对于 No Authentication,请配置客户端使用不支持身份验证的代理地址。使用 Proxy Authentication时,请使用有效的凭据进行配置。检查网络流量的代理可能会干扰 Web 套接字连接。如果出现此问题,则绕过不检查流量的步骤。 *.Webex.com 或许能解决问题。如果已经看到其他条目,请在最后一个条目后添加分号,然后输入 Webex 例外。
Windows 操作系统的代理设置
Microsoft Windows 支持两个用于 HTTP 流量的网络库(WinINet 和 WinHTTP),允许进行代理配置。WinINet 是 WinHTTP 的超集。
-
WinInet 专为单用户桌面客户端应用程序而设计。
-
WinHTTP 主要面向多用户、基于服务器的应用程序而设计。
在两者之间进行选择时,请选择 WinINet 作为代理配置设置。有关详细信息,请参阅 wininet-vs-winhttp。
有关以下内容的详细信息,请参阅 配置允许在企业网络上访问 Webex 的域列表 :
-
确保用户只能使用预定义域列表中的帐户登录应用程序。
-
使用代理服务器来拦截请求并限制允许的域。
代理检查和证书置顶
Webex 应用和设备在建立 TLS 会话时会验证服务器的证书。证书检查,例如证书颁发者和数字签名,依赖于验证直至根证书的证书链。为了执行验证检查,Webex 应用和设备使用安装在操作系统信任存储中的一组受信任的根 CA 证书。
如果您已部署 TLS 检查代理来拦截、解密和检查 Webex Calling 流量。确保代理提供的证书(而不是 Webex 服务证书)由证书颁发机构签名,并且根证书已安装在 Webex 应用或 Webex 设备的信任存储区中。
-
对于 Webex 应用 - 在设备的操作系统中安装用于由代理签署证书的 CA 证书。
-
对于 Webex Room 设备和 Cisco 多平台 IP 电话 - 向 TAC 团队提交服务请求以安装 CA 证书。
此表显示了支持通过代理服务器进行 TLS 检测的 Webex 应用和 Webex 设备
|
产品 |
支持自定义受信任 CA 以进行 TLS 检查 |
|---|---|
|
Webex 应用程序 (Windows、Mac、iOS、Android、Web) |
有 |
|
Webex Room 设备 |
有 |
|
思科IP多平台(MPP)电话 |
是 |
防火墙配置
Cisco 在安全的 Cisco 和 Amazon Web Services (AWS) 数据中心中支持 Webex Calling 和 Webex Aware 服务。亚马逊已将其 IP 子网预留给思科独家使用,并保护了位于这些子网中的 AWS 虚拟私有云内的服务。
配置您的防火墙,以允许您的设备、应用程序和面向互联网的服务进行通信,从而使其功能正常运行。此配置允许访问所有受支持的 Webex Calling 和 Webex Aware 云服务、域名、IP 地址、端口和协议。
将以下内容加入白名单或开放访问权限,以便 Webex Calling 和 Webex Aware 服务正常运行。
-
这 URLs/Domains 在 Webex Calling 服务的域名和 URL 部分中提到的内容以及在 Webex Calling 服务的 IP 子网 [ 部分中列出的 IP 子网、端口和协议用于多种用途,包括呼叫信令、进出 Webex Calling 的媒体流量、网络时间协议 (NTP) 同步以及这些 IP 子网的 CScan 网络就绪性测试。
-
如果您的组织使用 Webex 套件云协作服务(包括 Webex Meetings、Messaging、Webex Attendant Console、Webex Edge Connect 私有网络对等连接到 Webex 主干网以及其他相关服务),请确保文章 Webex 服务网络要求、 Webex Edge Connect和 Attendant Console 网络要求 中指定的 IP 子网、域和 URL 可以通过您的网络。这是为了保证这些 Webex 服务的正常连接和功能。
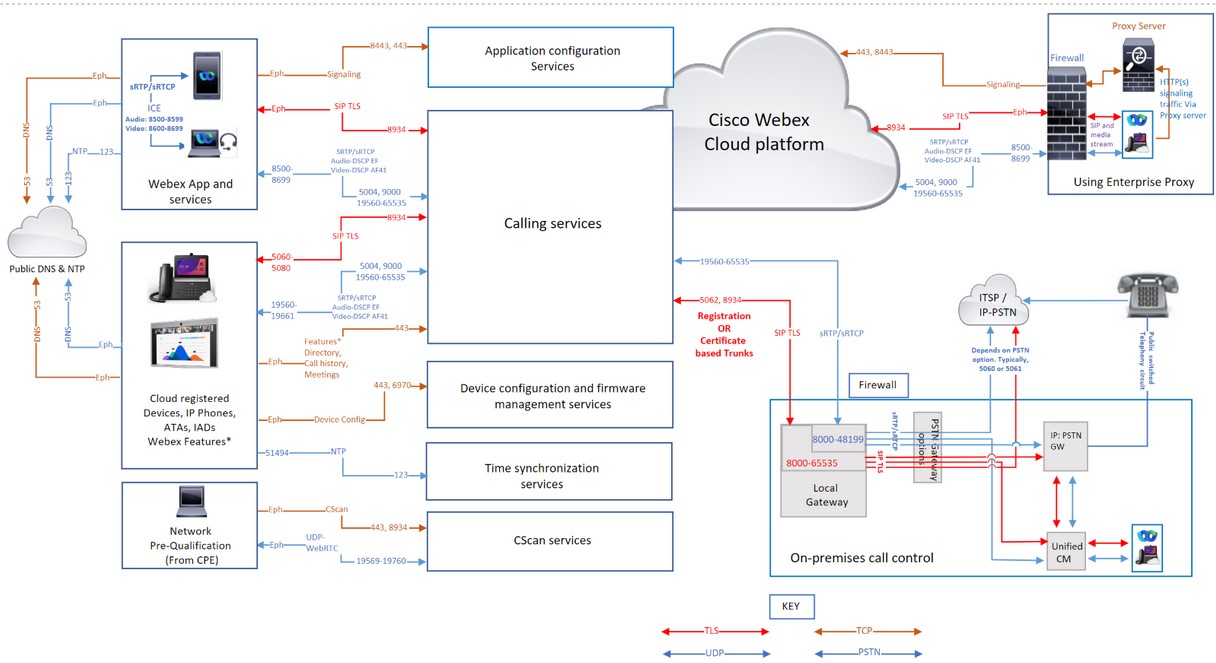
Webex通话流量通过代理和防火墙
如果您仅使用防火墙,则不支持仅使用 IP 地址过滤 Webex Calling 流量,因为某些 IP 地址池是动态的,随时可能发生变化。思科不赞成根据特定地理区域或云服务提供商过滤部分 IP 地址。按地区筛选可能会严重降低通话体验。
Cisco 不维护动态变化的 IP 地址池,因此本文中未列出。定期更新您的规则,未能更新防火墙规则列表可能会影响用户体验。
如果您的防火墙不支持 Domain/URL 进行过滤,然后使用企业代理服务器选项。此选项 filters/allows 经过 URL/domain 在将 HTTPS 信令流量转发到您的代理服务器之前,先将其转发到您的防火墙。
在使用企业代理服务器选项进行过滤时 Domain/URLs, 请注意,它并非设计用于处理交互式音频和视频,它仅用于 HTTPS 信令流量。始终使用:
-
基于端口和IP子网的呼叫信令过滤 & 媒体
-
Domain/URL 过滤适用于 HTTP(s) 信令流量
对于 Webex Calling,UDP 是 Cisco 首选的媒体传输协议,并且建议仅使用 SRTP over UDP。在生产环境中,Webex Calling 不支持使用 TCP 和 TLS 作为媒体传输协议。这些协议的面向连接的特性会影响网络丢包对媒体质量的影响。如果您对传输协议有任何疑问,请提交支持工单。
Webex Calling 服务的域名和 URL
一个 * 显示在网址的开头(例如, *.webex.com) 表示顶级域及其所有子域中的服务均可访问。
|
域/URL |
描述 |
使用这些域/URL 的 Webex 应用程序和设备 |
|---|---|---|
|
Cisco Webex Calling 和 Webex Aware 服务 | ||
|
*.broadcloudpbx.com |
Webex Control Hub 到呼叫管理门户交叉启动的授权微服务。 |
Control Hub |
|
*.broadcloud.com.au |
Webex Calling 服务(澳大利亚)。 |
所有 |
|
*.broadcloud.eu |
Webex Calling 服务(欧洲)。 |
所有 |
|
*.broadcloudpbx.net |
呼叫客户端配置和管理服务。 |
Webex 应用程序 |
|
*.webex.com *.cisco.com |
Webex 通话核心 & Webex Aware 服务
当手机首次连接到网络或在恢复出厂设置且未设置 DHCP 选项后连接到网络时,它会联系设备激活服务器进行零接触配置。新电话使用 activate.cisco.com,而固件版本早于 11.2(1) 的电话继续使用 webapps.cisco.com 进行配置。 从 binaries.webex.com下载设备固件和区域设置更新。 允许版本低于 12.0.3 的 Cisco 多平台电话 (MPP) 通过端口 80 访问 sudirenewal.cisco.com 以更新制造商安装证书 (MIC) 并获得安全唯一设备标识符 (SUDI)。详情请参见 现场通知。 如果您未使用代理服务器,而仅使用防火墙过滤 URL,则添加 |
全部 |
|
*.ucmgmt.cisco.com |
Webex Calling 服务 |
Control Hub |
|
*.wbx2.com 和 *.ciscospark.com |
用于云感知,以便连接到 Webex Calling & Webex Aware 在入职期间和入职后提供的服务。 这些服务是必要的
|
全部 |
|
*.webexapis.com |
Webex 微服务,用于管理您的 Webex App 应用程序和 Webex 设备。
|
全部 |
|
*.webexcontent.com |
Webex Messaging 提供的与通用文件存储相关的服务包括:
|
Webex Apps 消息服务。 2019年10月,使用webexcontent.com的文件存储服务被clouddrive.com取代。 |
|
*.accompany.com |
人员洞察整合 |
Webex 应用程序 |
|
其他 Webex 相关服务 (第三方域名) | ||
|
*.appdynamics.com *.eum-appdynamics.com |
性能跟踪、错误和崩溃捕获、会话指标。 |
Webex 应用,Webex Web 应用 |
|
*.sipflash.com |
设备管理服务。用于固件升级和安全注册。 |
Webex 应用程序 |
|
*.walkme.com *.walkmeusercontent.com |
Webex 用户指南客户端。为新用户提供加入和使用教程。 有关 WalkMe 的更多信息,请单击此处。 |
Webex 应用程序 |
|
*.google.com *.googleapis.com |
向移动设备上的 Webex 应用发送通知(例如:接通电话时会收到新消息) 有关 IP 子网,请参阅以下链接 Google Firebase 云消息传递 (FCM) 服务 Apple Push Notification Service (APNS) 对于 APNS,Apple 列出了该服务的 IP 子网。 | Webex 应用程序 |
|
api.wxc.e911cloud.com wxc.e911cloud.com |
911 (E911) 紧急服务 (RedSky) 与 Webex Calling 集成 电话和 Webex 客户端通过 443 端口与 RedSky 服务通信。 有关详细信息,请参阅文章 e911 服务与 Webex Calling 的集成 。 |
Webex 应用、设备 |
|
*.quovadisglobal.com *.digicert.com *.identrust.com *.godaddy.com |
这是用来检查安全证书的“证书吊销列表”的。证书吊销列表确保任何被泄露的证书都不能用于拦截通过 TCP 端口 80 进行的安全 Webex 流量。 Webex Calling 支持 CRL 和 OCSP 装订来确定证书吊销状态。虽然 OCSP 装订减少了 Webex App 联系 CA 的需要;但设备仍然可以直接联系证书颁发机构。此过程验证硬件身份,执行 802.1X 网络身份验证,或者在装订响应不可用或无效时下载 CRL。 | 全部 |
Webex 通话服务的 IP 子网
HTTPS 信令 - Webex Calling 和 Webex Aware 服务的会话建立基于 URL 而不是 IP 地址。网络 firewalls/proxies 必须允许访问 Domains/URLs 不仅仅是IP范围。
|
Webex Calling 服务的 IP 子网*† | ||
|---|---|---|
|
(1)呼叫信令、媒体、NTP & CScan | ||
|
23.89.0.0/16 |
62.109.192.0/18 |
85.119.56.0/23 |
|
128.177.14.0/24 |
128.177.36.0/24 |
135.84.168.0/21 |
|
139.177.64.0/21 |
139.177.72.0/23 |
144.196.0.0/16 |
|
150.253.128.0/17 |
163.129.0.0/17 |
170.72.0.0/16 |
|
170.133.128.0/18 |
185.115.196.0/22 |
199.19.196.0/23 |
|
199.19.199.0/24 |
199.59.64.0/21 | |
|
(2)设备配置和固件管理(思科设备) | ||
|
3.14.211.49 |
3.20.185.219 |
3.130.87.169 |
|
3.134.166.179 |
52.26.82.54 |
62.109.192.0/18 |
|
72.163.10.96/27 |
72.163.15.64/26 |
72.163.15.128/26 |
|
72.163.24.0/23 |
72.163.10.128/25 |
173.37.146.128/25 |
|
173.36.127.0/26 |
173.36.127.128/26 |
173.37.26.0/23 |
|
173.37.149.96/27 |
192.133.220.0/26 |
192.133.220.64/26 |
|
(3)Webex应用程序配置 | ||
|
62.109.192.0/18 |
64.68.96.0/19 |
150.253.128.0/17 |
|
207.182.160.0/19 | ||
|
连接目的 | 源地址 | 源端口 | 协议 | 目的地地址 | 目的地端口 | 说明 | |
|---|---|---|---|---|---|---|---|
| 到 Webex Calling 的呼叫信令 (SIP TLS) | 本地网关外部 (NIC) | 8000-65535 | TCP | 请参阅 Webex 呼叫服务的 IP 子网 (1)。 | 5062, 8934 |
这些 IPs/ports 需要从本地网关、设备和 Webex 应用程序(源)向 Webex Calling Cloud(目标)发出出站 SIP-TLS 呼叫信令。 端口 5062(基于证书的中继需要)。端口 8934(基于注册的中继线路需要此端口) | |
| 设备 | 5060-5080 | 8934 | |||||
| Room 系列 | 临时 | ||||||
| Webex 应用程序 | 临时(依赖于操作系统) | ||||||
| 从 Webex Calling (SIP TLS) 到本地网关的呼叫信令 |
Webex 通话地址范围。 请参阅Webex 通话服务的 IP 子网 (1) | 8934 | TCP | 客户为其本地网关选择的 IP 地址或 IP 地址范围 | 客户为其本地网关选择的端口或端口范围 |
适用于基于证书的本地网关。需要建立从 Webex Calling 到本地网关的连接。 基于注册的本地网关的工作原理是重用从本地网关创建的连接。 目标端口由客户选择 配置中继 | |
| 呼叫媒体到 Webex 呼叫(STUN, SRTP/SRTCP, T38,DTLS) | 本地网关外部 NIC | 8000-48199†* | UDP | 请参阅 Webex 呼叫服务的 IP 子网 (1)。 |
5004、9000、8500—8699、19560—65535(基于UDP的SRTP) |
| |
| 设备†* | 19560-19661 | ||||||
| 房间系列†* | 音频 52050-52099 视频52200-52299 | ||||||
|
VG400 ATA 设备 | 19560-19849 | ||||||
| Webex 应用†* |
音频:8500-8599 视频:8600-8699 | ||||||
|
WebRTC | 短暂的(根据浏览器政策) | ||||||
| Webex Calling 的通话媒体 (SRTP/SRTCP, T38) |
Webex 通话地址范围。 请参阅Webex 通话服务的 IP 子网 (1) | 19560-65535(基于UDP的SRTP) | UDP | 客户为其本地网关选择的 IP 地址或 IP 地址范围 | 客户为其本地网关选择的媒体端口范围 |
适用于基于证书的本地网关 | |
| 到 PSTN 网关的呼叫信令 (SIP TLS) | 本地网关内部 NIC | 8000-65535 | TCP | 您的 ITSP PSTN GW 或 Unified CM | 取决于 PSTN 选项(例如,对于 Unified CM,通常为 5060 或 5061) | ||
| 呼叫媒体至 PSTN 网关 (SRTP/SRTCP) | 本地网关内部 NIC | 8000-48199†* | UDP | 您的 ITSP PSTN GW 或 Unified CM | 取决于 PSTN 选项(例如,统一 CM 通常为 5060 或 5061)。 | ||
| 设备配置和固件管理(Cisco 设备) | Webex Calling 设备 | 临时 | TCP |
请参阅Webex 通话服务的 IP 子网 (2) | 443, 6970, 80 |
出于以下原因需要:
| |
| Webex App 配置 | Webex App 应用程序 | 临时 | TCP |
请参阅Webex 通话服务的 IP 子网 (3) | 443, 8443 | 用于身份代理身份验证、Webex 应用程序客户端配置服务、基于浏览器的自助服务 Web 访问以及管理界面访问。 Cisco Unified CM 设置中的 Webex App 使用 TCP 端口 8443 下载配置。只有使用该设置连接到 Webex Calling 的客户才需要打开端口。 | |
| 设备时间同步 (NTP) | Webex Calling 设备 | 临时 | UDP | 请参阅 Webex 呼叫服务的 IP 子网 (1)。 | 123 †* | 需要这些 IP 地址才能实现设备(MPP 电话、ATA 和 SPA ATA)的时间同步 | |
|
域名系统 (DNS) 解析 | Webex 通话设备、Webex 应用和 Webex 设备 | 临时 | UDP 和 TCP | 主机定义 | 53†* | 用于 DNS 查询,以发现云端 Webex Calling 服务的 IP 地址。尽管典型的 DNS 查询是通过 UDP 完成的,但如果查询响应无法放入 UDP 数据包中,则某些查询可能需要 TCP。 | |
| 网络时间协议 (NTP) | Webex 应用和 Webex 设备 | 123 | UDP | 主机定义 | 123 | 时间同步 | |
| CScan | 基于网络的网络就绪性预审工具(适用于 Webex Calling) | 临时 | TCP | 请参阅 Webex 呼叫服务的 IP 子网 (1)。 | 8934 和 443 | 基于网络的网络就绪性预审工具,适用于 Webex Calling。有关更多信息,请参阅 cscan.webex.com。 | |
| UDP | 19569-19760 | ||||||
| 附加 Webex 通话 & Webex Aware 服务 (第三方) | |||||||
| 推送通知 APNS 和 FCM 服务 | Webex Calling 应用程序 | 临时 | TCP |
请参阅链接中提到的 IP 子网。 | 443, 2197, 5228, 5229, 5230, 5223 | 向移动设备上的 Webex 应用发送通知(例如:当您收到新消息或接听电话时) | |
-
†* 本地网关媒体端口范围可通过 rtp-port range进行配置。
-
†*SRTP 端口范围内动态分配的设备和应用程序的媒体端口。SRTP 端口为偶数端口,对应的 SRTCP 端口分配为连续的奇数端口。
-
如果为您的应用和设备配置了代理服务器地址,则信令流量将发送到代理服务器。通过 UDP 流传输的 SRTP 媒体将直接传输到您的防火墙,而不是代理服务器。
-
如果您在企业网络中使用 NTP 和 DNS 服务,则仍必须允许 出站 DNS (UDP/TCP 53) 和 NTP (UDP 123) 流量通过您的防火墙,用于 Webex Calling 和 Webex Aware 服务。虽然您的内部 DNS 处理本地查找,但对于 Webex 服务,设备和应用程序必须解析外部服务的 FQDN 和 SRV 记录。IP 电话等设备通常会连接到公共 NTP 服务器或 Webex Calling 自己的时间服务器,以保持其内部时钟同步,这对于通话安全和注册至关重要。
Webex Calling 的 MTU 大小 & Webex Aware 服务
最大可传输单元 (MTU) 是 IP 数据包在网络链路上传输而无需分片的最大大小。如果 MTU 未设置为默认值,则可能会出现问题。Webex Calling 建议将网络上所有 IP 数据包的默认 MTU 大小保持为 1500 字节。
对于 Webex Calling 和 Webex Aware 服务,如果数据包需要分片,请设置“不分片 (DF)”位以强制使用 ICMP 通信。
服务质量 (QoS)/Type 服务(ToS)
允许您对从本地设备或客户端到 Webex Calling 云平台的包进行标记。QoS 使您能够优先处理实时流量,而不是其他数据流量。启用此设置会修改使用 SIP 信令和媒体的应用程序和设备的 QoS 标记。
| 源地址 | 交通类型 | 目的地地址 | 源端口 | 目的地端口 | DSCP 等级和值 |
|---|---|---|---|---|---|
| Webex 应用程序 | 音频 |
请参考 Webex Calling 服务的 IP 子网、域名和 URL | 8500-8599 | 8500-8599, 19560-65535 | 加急货运 (46) |
| Webex 应用程序 | 视频 | 8600-8699 | 8600-8699, 19560-65535 | 保证转发 41 (34) | |
| Webex 应用程序 | 发送信号 | 临时(依赖于操作系统) | 8934 | CS0 (0) | |
| Webex 设备(MPP 和会议室) | 音频与视频 | 19560-19661 | 19560-65535 |
加急货运 (46) & 保证转发 41 (34) | |
| Webex 设备 | 发送信号 | 5060-5080 | 8934 | 类选择器 3 (24) |
-
为音频创建单独的 QoS 配置文件 Video/Share 因为它们的源端口范围不同,所以需要对流量进行不同的标记。
-
适用于 Windows 客户端:要为您的组织启用 UDP 源端口区分功能,请联系您当地的客户团队。如果不启用此功能,您将无法区分音频和 Video/Share 由于源端口相同,因此使用 Windows QoS 策略 (GPO)。 audio/video/share. 详情请参见 为 Webex App 启用媒体源端口范围
-
对于 Webex 设备,请在 Control Hub 设备设置中配置 QoS 设置更改。详情请参见 配置 & 在 Webex 通话中修改设备设置
Webex Meetings/Messaging - 网络要求
对于使用 Webex Suite 云协作服务、Webex 云注册产品的客户,请将 MPP 设备接入 Webex 云,以使用通话记录、目录搜索、会议和消息传递等服务。确保 Domains/URLs/IP Addresses/Ports 本文中提到的是Webex服务的 开放网络要求。
Webex for Government 的网络要求
如需获取 Webex for Government 服务的域名、URL、IP 地址范围和端口列表,请点击此处查看相关信息:Webex for Government 的网络要求
Webex Attendant Console 的网络要求
对于使用接待员控制台(包括接待员、服务员和操作员功能)的客户,请确保 Domains/URLs/IP Addresses/Ports/Protocols 开放 服务员控制台的网络要求
Webex Calling 本地网关入门
对于使用本地网关解决方案和 Webex Calling 实现本地 PSTN 和第三方 SBC 互操作性的客户,请阅读文章 “本地网关入门”。
引用
要了解 Webex Calling 的新增功能,请参阅 Webex Calling 的新增功能
有关 Webex Calling 的安全要求,请参阅 文章
使用交互式连接建立 (ICE) 进行 Webex 通话媒体优化 文章
文档修订历史
|
日期 |
我们对此文章进行了以下更改 |
|---|---|
|
2026年3月4日 |
在 Webex 呼叫服务的 IP 子网部分中,将设备时间同步 (NTP) 的源端口从 51494 更改为临时端口。 |
|
2026年2月23日 |
Webex Calling 的连接详情会在 IP 子网内更新。 以下还包含其他第三方网址:
对文章进行编辑更新,以提高文章的可读性。 |
|
2025年12月5日 |
添加了 Webex 通话服务的 IP 子网部分下列出的 IP 子网、端口和协议的使用方法。 |
|
2025年10月24日 |
提高了图像质量,并修复了与 Google Firebase 云消息传递 (FCM) 服务的失效链接 |
|
2025年9月15日 |
|
|
2025年4月10日 |
包含的文本旨在强调 Webex Calling 和 Webex Aware 服务的 MTU 大小 |
|
2025年3月27日 |
已更新 Webex 通话服务的 IP 子网 62.109.192.0/18 为了适应 Webex Calling 在沙特阿拉伯地区的市场扩张。 |
|
2025年1月21日 |
添加了有关使用 SIP 应用层网关的详细信息。 |
|
2025年1月8日 |
已将与设备配置和 Webex 应用配置相关的 IP 子网地址移至 Webex 通话服务的 IP 子网 部分 |
|
2024年12月17日 |
为 Webex Calling Media 规范添加了对 WebRTC 的支持。 |
|
2024年11月14日 |
更新了 VG400 系列 ATA 设备对 Webex Calling 通话媒体的支持端口范围 |
|
2024年11月11日 |
为 VG400 系列 ATA 设备添加了 Webex Calling 通话媒体支持的端口范围 |
|
2024年7月25日 |
重新添加了 52.26.82.54 IP 子网,因为 Cisco ATA 设备配置和固件管理需要它。 |
|
2024年7月18日 |
更新内容如下:
|
|
2024年6月28日 |
更新了 Webex 通话媒体规范中 SRTP/SRTCP 端口范围的使用情况。 |
|
2024年6月11日 |
已移除“huron-dev.com”域名,因为它未使用。 |
|
2024年5月6日 |
更新了 Webex 通话媒体规范中 SRTP/SRTCP 端口范围的使用情况。 |
|
2024年4月3日 | 已更新 Webex Calling 服务的 IP 子网 163.129.0.0/17 为了适应 Webex Calling 在印度地区的市场扩张。 |
|
2023年12月18日 |
包括 sudirenewal.cisco.com URL 和端口 80,用于 Cisco MPP 电话的 MIC 续订的设备配置和固件管理。 |
|
2023年12月11日 |
更新了 Webex Calling 服务的 IP 子网,使其包含更多 IP 地址。 150.253.209.128/25 – 改为 150.253.128.0/17 |
|
2023年11月29日 |
更新了 Webex Calling 服务的 IP 子网,使其包含更多 IP 地址,以适应 Webex Calling 区域的未来扩展。 144.196.33.0/25 – 改为 144.196.0.0/16 Webex Calling (SIP TLS) 和呼叫媒体到 Webex Calling (STUN, SRTP) 部分下的 Webex Calling 服务 IP 子网已更新,以明确基于证书的中继和本地网关的防火墙要求。 |
|
2023 年 8 月 14 日 |
我们已添加以下 IP 地址 144.196.33.0/25 和 150.253.156.128/25 为了满足 Edge 和 Webex 通话服务不断增长的容量需求。 此IP地址范围仅在美国地区受支持。 |
|
2023年7月5日 |
添加了用于安装 Cisco MPP 固件的链接 https://binaries.webex.com 。 |
|
2023年3月7日 |
我们已对整篇文章进行了全面修改,内容包括:
|
|
2023年3月5日 |
更新文章内容,添加以下内容:
|
|
2022 年 11 月 15 日 |
我们已添加以下 IP 地址用于设备配置和固件管理(思科设备):
我们已从设备配置和固件管理(思科设备)中移除以下 IP 地址:
|
|
2022年11月14日 |
添加了 IP 子网 170.72.242.0/24 适用于 Webex 通话服务。 |
|
2022 年 9 月 8 日 |
Cisco MPP 固件在所有地区都将过渡到使用 https://binaries.webex.com 作为 MPP 固件升级的主机 URL。此更改改进了固件升级性能。 |
|
2022 年 8 月 30 日 |
从端口表中的设备配置和固件管理(思科设备)、应用程序配置和 CScan 行中删除了对端口 80 的引用,因为不存在依赖关系。 |
|
2022 年 8 月 18 日 |
解决方案没有变化。将呼叫信号的目标端口 5062(基于证书的中继需要)和 8934(基于注册的中继的必需)更新为 Webex Calling (SIP TLS)。 |
|
2022 年 7 月 26 日 |
添加了 54.68.1.225 IP 地址,这是 Cisco 840/860 设备的固件升级所需的 IP 地址。 |
|
2022 年 7 月 21 日 |
将呼叫信号的目标端口 5062、8934 更新Webex Calling (SIP TLS)。 |
|
2022 年 7 月 14 日 |
添加了支持 Webex Aware 服务完整功能的 URL。 添加了 IP 子网 23.89.154.0/25 适用于 Webex 通话服务。 |
|
2022 年 6 月 27 日 |
更新了服务域和 url Webex Calling URL: *.broadcloudpbx.com *.broadcloud.com.au *.broadcloud.eu *.broadcloudpbx.net |
|
2022 年 6 月 15 日 |
在服务 IP 地址和 端口下添加了下列Webex Calling和协议:
Webex 中已更新信息 Meetings/Messaging - 网络要求 部分 |
|
2022 年 5 月 24 日 |
为服务添加 IP 子网 52.26.82.54/24 至 52.26.82.54/32 Webex Calling服务 |
|
2022 年 5 月 6 日 |
添加了服务 52.26.82.54/24 的 IP Webex Calling子网 |
|
2022 年 4 月 7 日 |
已将本地网关的内部和外部 UDP 端口范围更新为 8000-48198† |
|
2022 年 4 月 5 日 |
添加了以下 IP 子网Webex Calling服务:
|
|
2022 年 3 月 29 日 |
添加了以下 IP 子网Webex Calling服务:
|
|
2021 年 9 月 20 日 |
新增 4 个 IP 子网用于 Webex Calling 服务:
|
|
2021 年 4 月 2 日 |
额外 *.ciscospark.com 在 Webex Calling Services 的域名和 URL 下,以支持 Webex App 中的 Webex Calling 用例。 |
|
2021 年 3 月 25 日 |
为 activate.cisco.com 添加了 6 个新的 IP 地址范围,自 2021 年 5 月 8 日起生效。
|
|
2021 年 3 月 4 日 |
已使用独立表格中的简化范围替换 Webex Calling 分散式 IP 和范围较小的 IP,以便于了解防火墙配置。 |
|
2021 年 2 月 26 日 |
将 5004 作为呼叫媒体的目标端口添加到 Webex Calling(STUN、SRTP)来支持将在 2021 年 4 月提供的交互式连接增强器 (Webex Calling ICE)。 |
|
2021 年 2 月 22 日 |
域和 URL 现已列在独立表格中。 IP 地址和端口表已进行调整,以便将相同服务的 IP 地址分组。 在 IP 地址和端口表中添加“备注”列,以帮助理解需求。 将以下 IP 地址移至简化范围,以便进行设备配置和固件管理(思科设备):
由于 Cisco Webex 客户端在 2021 年 3 月指向澳大利亚较新的 DNS SRV,因此为应用程序配置添加以下 IP 地址。
|
|
2021 年 1 月 21 日 |
我们已将以下 IP 地址添加到设备配置和固件管理(思科设备):
我们已从设备配置和固件管理(思科设备)中移除以下 IP 地址:
我们已将以下 IP 地址添加到应用程序配置中:
我们已从应用程序配置中移除以下 IP 地址:
我们已从应用程序配置中移除以下端口号:
我们已将以下域名添加到应用程序配置中:
|
|
2020 年 12 月 23 日 |
在端口引用图像中添加了新的应用程序配置 IP 地址。 |
|
2020 年 12 月 22 日 |
更新了表格中的应用程序配置行以包含以下 IP 地址:135.84.171.154 和 135.84.172.154。 在添加这些 IP 地址之前,请隐藏网络拓扑图。 |
|
2020 年 12 月 11 日 |
更新了受支持的加拿大区域的设备配置和固件管理(Cisco 设备)和应用程序配置行。 |
|
2020 年 10 月 16 日 |
用以下 IP 地址更新了呼叫信令和媒体条目:
|
|
2020 年 9 月 23 日 |
在 CScan 下,将 199.59.64.156 替换为 199.59.64.197。 |
|
2020 年 8 月 14 日 |
添加了更多 IP 地址以支持加拿大的数据中心采用: 到 Webex Calling 的呼叫信令(SIP TLS)—135.84.173.0/25、135.84.174.0/25、199.19.197.0/24、199.19.199.0/24 |
|
2020 年 8 月 12 日 |
添加了更多 IP 地址以支持加拿大的数据中心采用:
|
|
2020 年 7 月 22 日 |
添加了以下 IP 地址以支持加拿大的数据中心采用:135.84.173.146 |
|
2020 年 6 月 9 日 |
我们对 CScan 条目进行了以下更改:
|
|
2020 年 3 月 11 日 |
我们在应用程序配置中添加了以下域名和 IP 地址:
我们更新了以下域,将额外 IP 地址用于设备配置和固件管理:
|
|
2020 年 2 月 27 日 |
我们将以下域和端口添加到设备配置和固件管理: cloudupgrader.webex.com—443, 6970 |


