Configurar o gateway local no Cisco IOS XE do Webex Calling
 Comentários?
Comentários?Visão geral
O Webex Calling atualmente suporta duas versões do Gateway Local:
-
Gateway local
-
Portal local para Webex para o governo
-
Antes de começar, entenda os requisitos da Rede Telefônica Pública Comutada (PSTN) e do Gateway Local (LGW) para o Webex Calling em instalações próprias. Consulte Arquitetura de preferência da Cisco para Webex Calling para obter mais informações.
-
Este artigo pressu que uma plataforma de Gateway local dedicada está no lugar sem a configuração de voz existente. Se você modificar um gateway PSTN existente ou uma implementação do CUBE Enterprise para usar como função de Gateway Local para Chamadas Webex, preste muita atenção à configuração. Certifique-se de não interromper os fluxos de chamadas e funcionalidades existentes devido às alterações que você fizer.
Os procedimentos contêm links para a documentação de referência dos comandos, onde você pode aprender mais sobre as opções de cada comando. Todos os links de referência de comandos levam ao Webex Managed Gateways Command Reference a menos que seja indicado o contrário (caso em que os links de comando levam ao Cisco IOS Voice Command Reference). Você pode acessar todos esses guias em Referências de comandos do Cisco Unified Border Element .
Para obter informações sobre os SBCs de terceiros suportados, consulte a documentação de referência do produto correspondente.
Há duas opções para configurar o Gateway local para seu Webex Calling de acesso:
-
Tronco baseado em registro
-
Tronco baseado em certificado
Use o fluxo de tarefas em Gateway Local baseado em registro ou Gateway Local baseado em certificado para configurar o Gateway Local para seu tronco de Chamadas Webex.
Consulte Introdução ao Gateway Local para obter mais informações sobre diferentes tipos de tronco. Execute os seguintes passos no próprio Gateway local, usando a Interface de Linha de Comando (CLI). Utilizamos o Protocolo de Iniciação de Sessão (SIP) e o Protocolo de Segurança da Camada de Transporte (TLS) para proteger o tronco e o Protocolo de Tempo Real Seguro (SRTP) para proteger a mídia entre o Gateway Local e o Webex Calling.
-
Selecione CUBE como seu gateway local. O Webex for Government não oferece suporte atualmente a nenhum Controlador de Fronteira de Sessão (SBC) de terceiros. Para consultar a lista mais recente, consulte Introdução ao Gateway Local.
- Instale o Cisco IOS XE Dublin 17.12.1a ou versões posteriores em todos os gateways locais do Webex for Government.
-
Para consultar a lista de Autoridades de Certificação (ACs) raiz que o Webex for Government suporta, consulte Autoridades de certificação raiz para Webex for Government.
-
Para obter detalhes sobre os intervalos de portas externas para o Gateway Local no Webex for Government, consulte Requisitos de rede para o Webex for Government (FedRAMP).
O Gateway Local para Webex para Governo não é compatível com o seguinte:
-
STUN/ICE-Lite para otimização do caminho da mídia
-
Fax (T.38)
Para configurar o Gateway Local para o seu tronco de chamadas Webex no Webex for Government, use a seguinte opção:
-
Tronco baseado em certificado
Use o fluxo de tarefas em Gateway local baseado em certificado para configurar o Gateway local para seu tronco de chamadas Webex. Para obter mais detalhes sobre como configurar um Gateway Local baseado em certificado, consulte Configurar tronco baseado em certificado do Webex Calling.
É obrigatório configurar cifras GCM compatíveis com FIPS para dar suporte ao Gateway Local do Webex para Governo. Caso contrário, o estabelecimento da chamada falha. Para obter detalhes de configuração, consulte Configurar tronco baseado em certificado do Webex Calling.
O Webex para Governo não suporta o Portal Local baseado em registro.
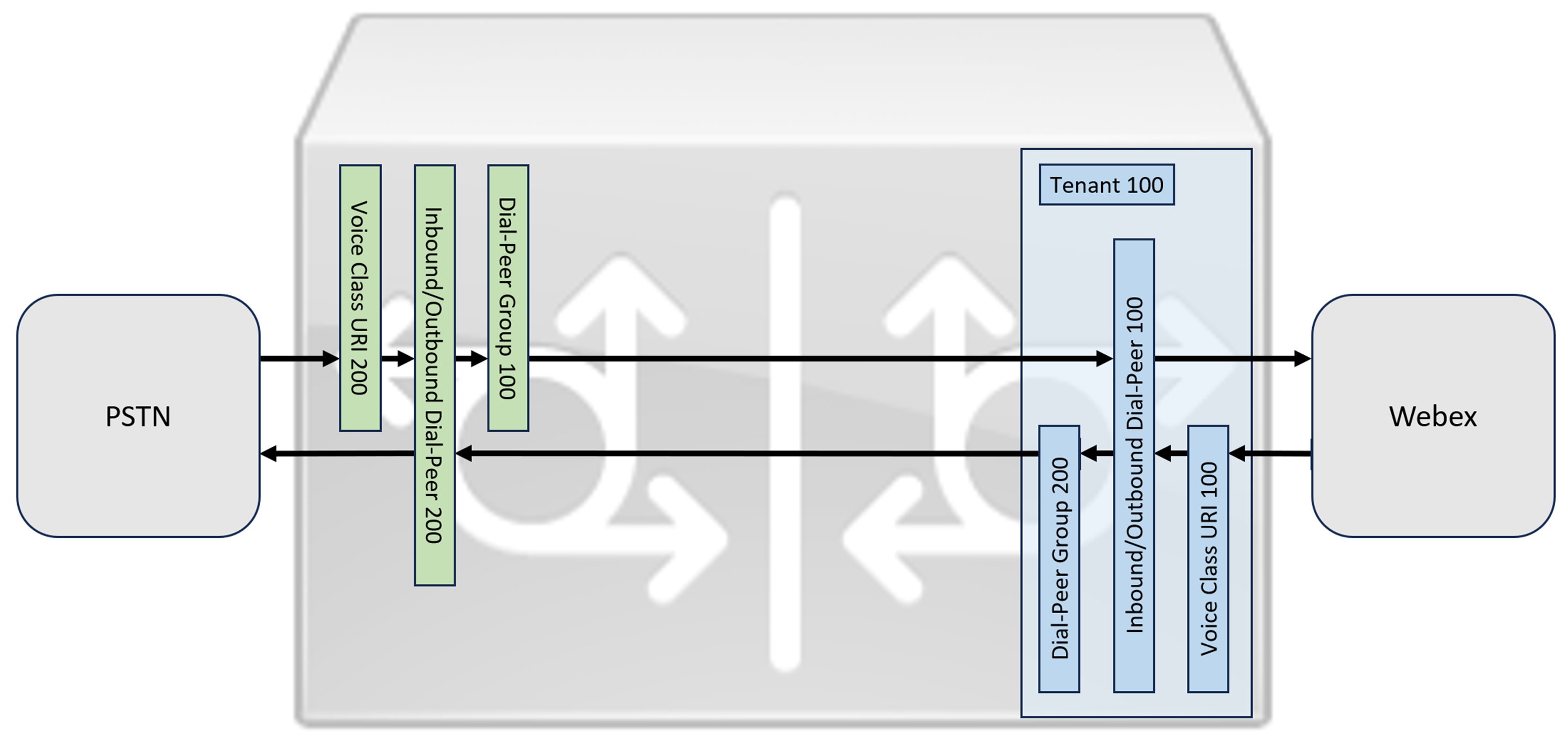
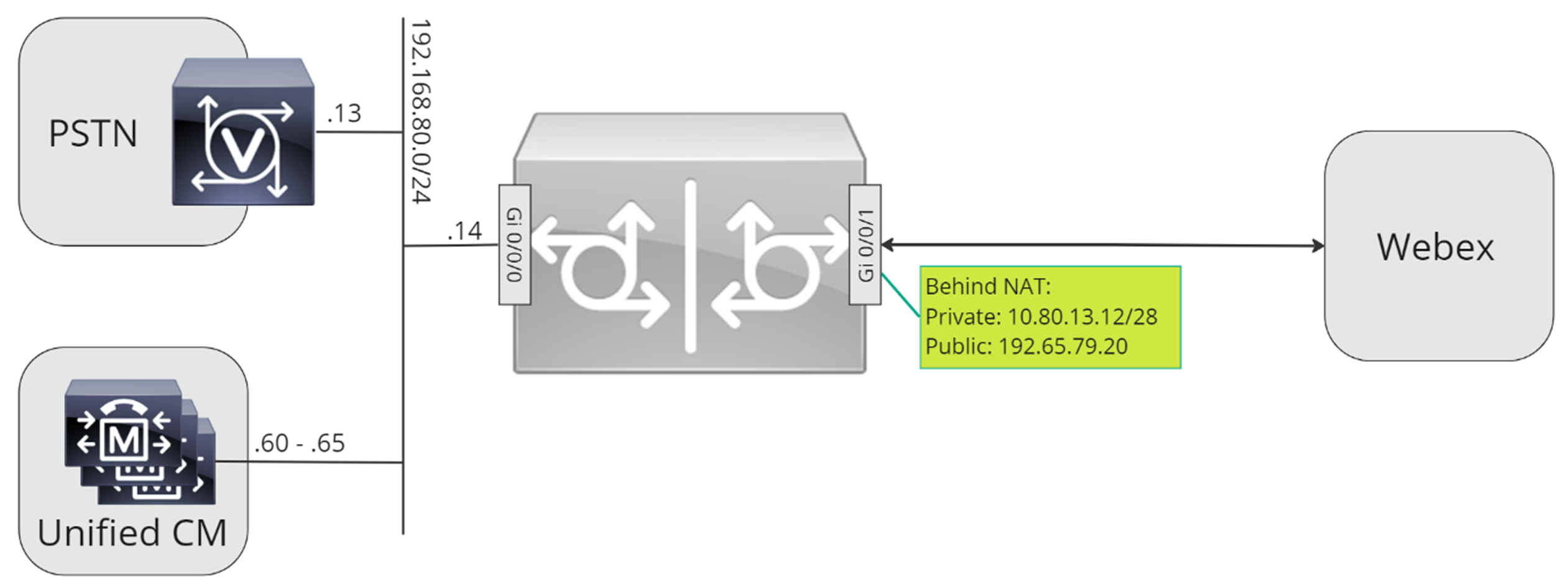
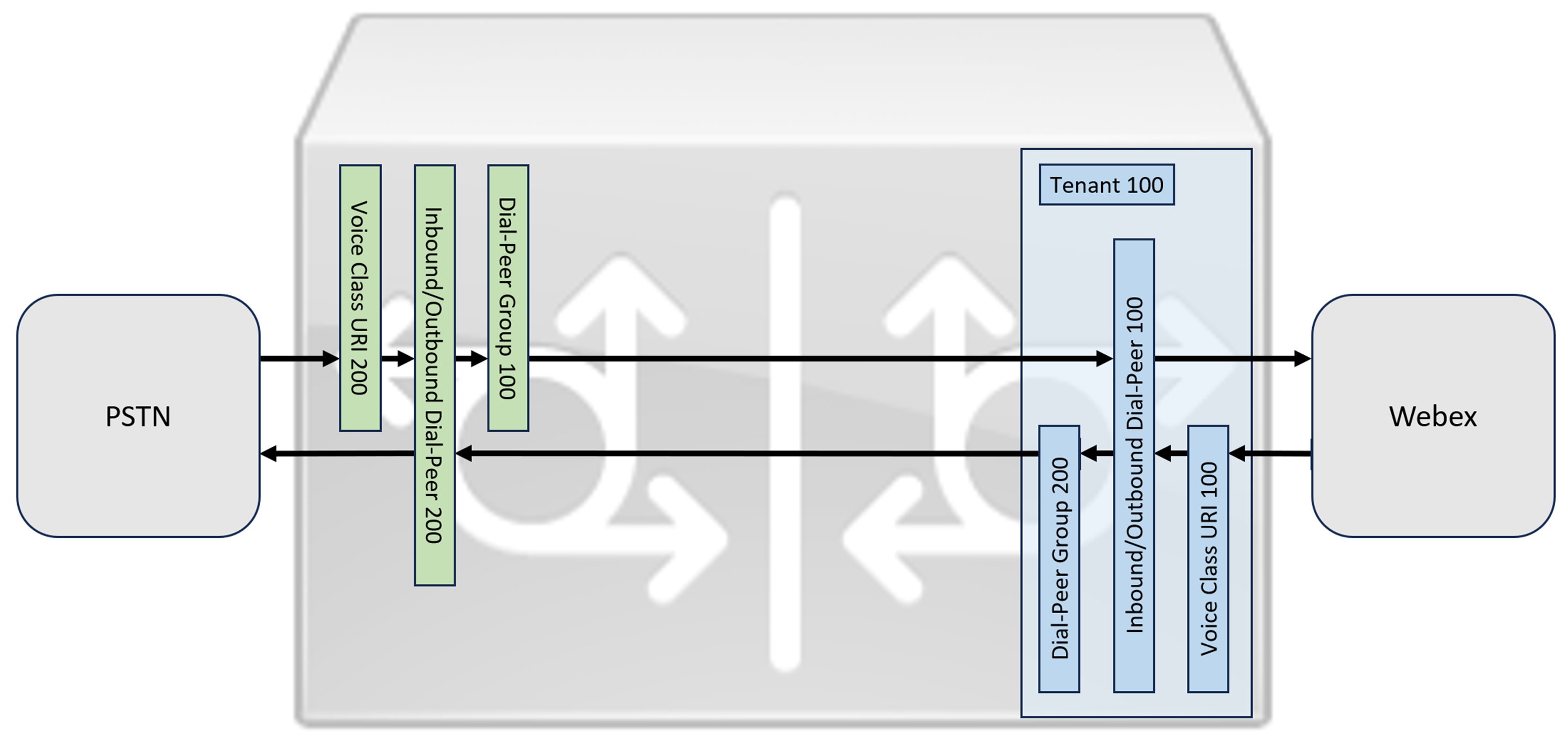
Esta seção descreve como configurar um Cisco Unified Border Element (CUBE) como um gateway local para chamadas Webex, usando um tronco SIP registrado. A primeira parte deste documento ilustra como configurar um gateway PSTN simples. Neste caso, todas as chamadas da PSTN são encaminhadas para o Webex Calling e todas as chamadas do Webex Calling são encaminhadas para a PSTN. A imagem abaixo destaca essa solução e a configuração de roteamento de chamadas de alto nível que será seguida.
Neste projeto, são utilizadas as seguintes configurações principais:
-
inquilinos da classe de voz: Utilizado para criar configurações específicas do tronco.
-
URI da classe de voz: Utilizado para classificar mensagens SIP para a seleção de um dial-peer de entrada.
-
dial-peer de entrada: Fornece tratamento para mensagens SIP de entrada e determina a rota de saída usando um grupo de dial-peers.
-
grupo de dial-peer: Define os dial-peers de saída usados para o encaminhamento de chamadas subsequentes.
-
discagem de saída: Fornece tratamento para mensagens SIP de saída e as encaminha para o destino necessário.
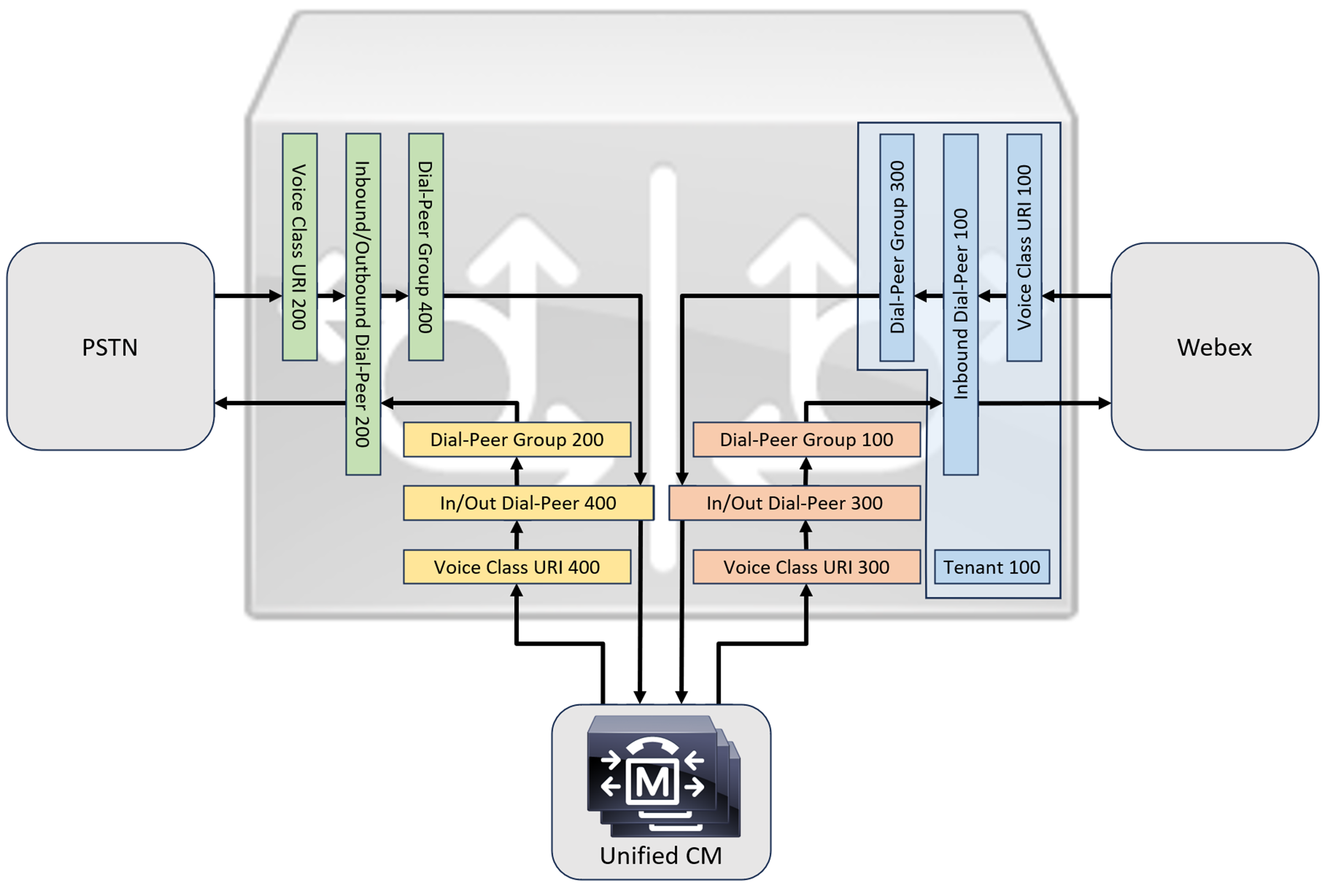
Embora os protocolos IP e SIP tenham se tornado os padrões para troncos PSTN, os circuitos ISDN TDM (Multiplexação por Divisão de Tempo) ainda são amplamente utilizados e compatíveis com os troncos do Webex Calling. Para permitir a otimização de mídia dos caminhos IP para gateways locais com fluxos de chamadas TDM-IP, atualmente é necessário usar um processo de roteamento de chamadas de duas etapas. Essa abordagem modifica a configuração de roteamento de chamadas mostrada acima, introduzindo um conjunto de dial-peers de loopback internos entre o Webex Calling e os troncos PSTN, conforme ilustrado na imagem abaixo.
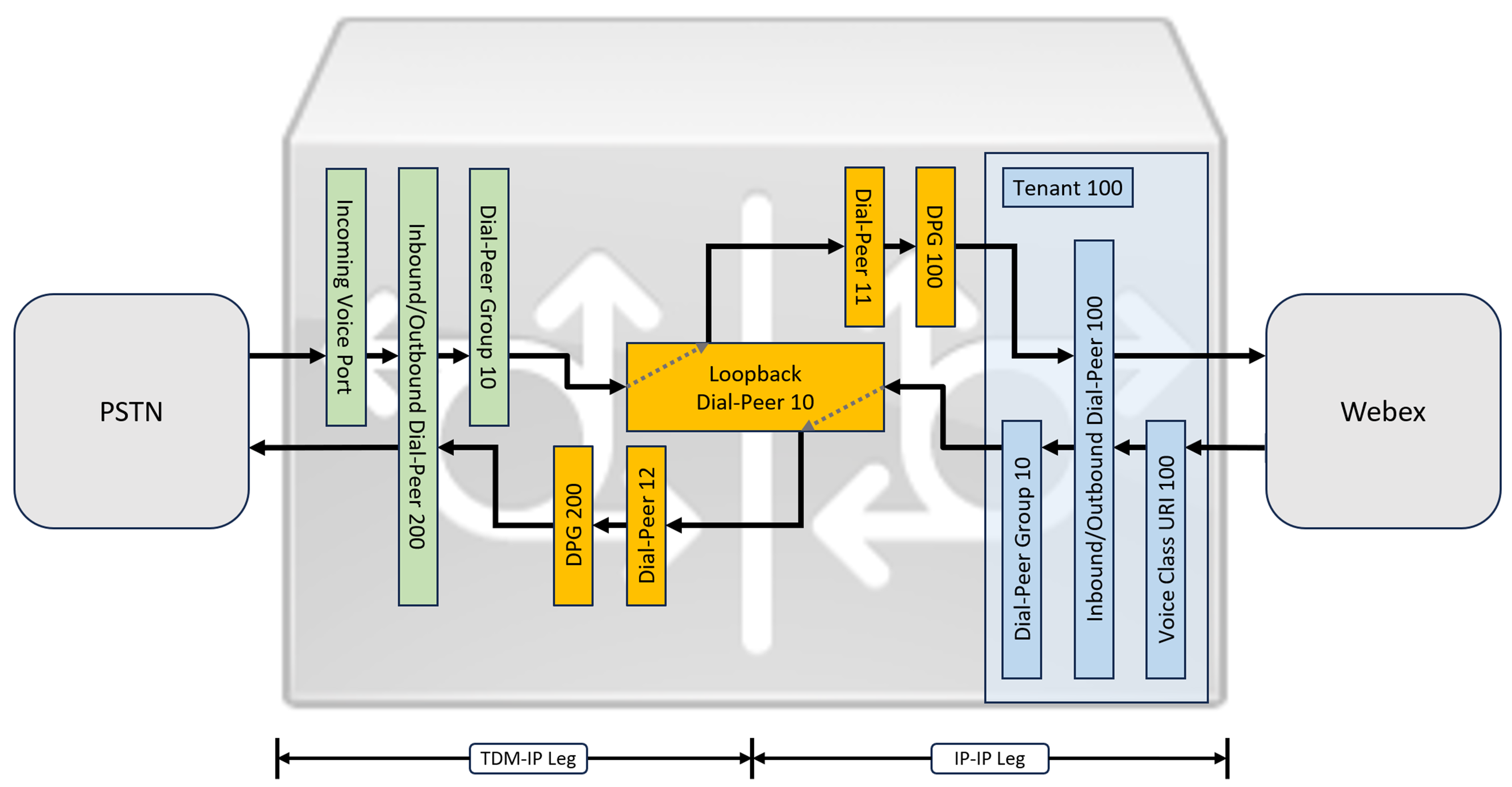
Ao conectar uma solução Cisco Unified Communications Manager local com o Webex Calling, você pode usar a configuração simples do gateway PSTN como base para criar a solução ilustrada no diagrama a seguir. Neste caso, o Unified Communications Manager fornece roteamento e tratamento centralizados de todas as chamadas PSTN e Webex Calling.
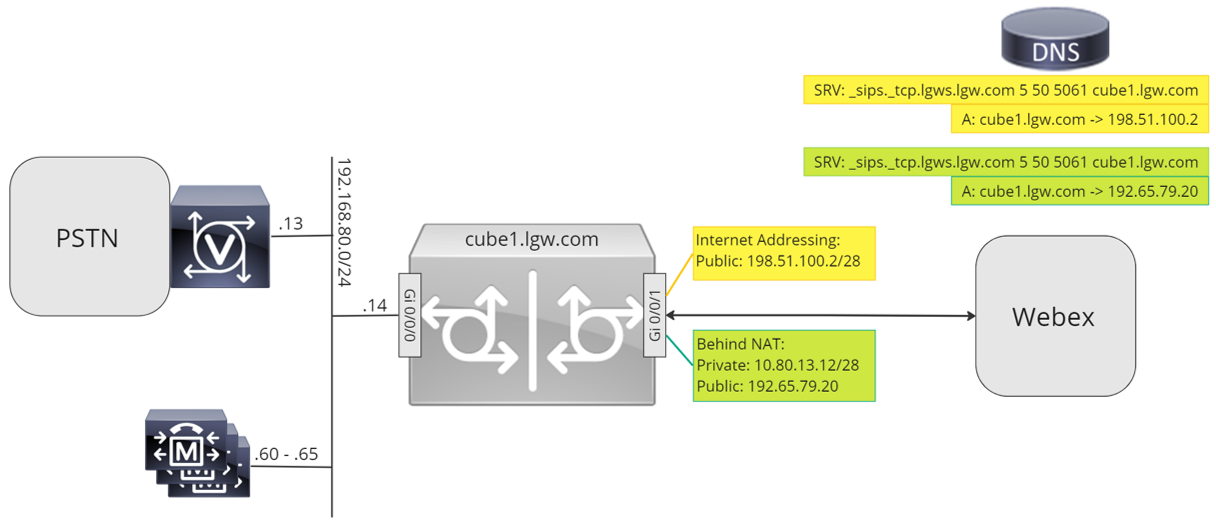
Ao longo deste documento, serão utilizados os nomes de host, endereços IP e interfaces ilustrados na imagem a seguir.
Utilize as orientações de configuração presentes no restante deste documento para concluir a configuração do seu Gateway Local da seguinte forma:
-
Passo 1: Configure a conectividade básica e a segurança do roteador.
-
Passo 2: Configurar tronco de chamadas do Webex
Dependendo da arquitetura necessária, siga um dos seguintes caminhos:
-
Passo 2: Configure o gateway local com o tronco SIP PSTN.
-
Passo 4: Configure o Gateway Local com um ambiente Unified CM existente
Ou:
-
Passo 2: Configure o gateway local com o tronco TDM PSTN.
Configuração básica
O primeiro passo para preparar seu roteador Cisco como um Gateway Local para o Webex Calling é criar uma configuração básica que proteja sua plataforma e estabeleça a conectividade.
-
Todas as implementações de Local Gateway baseadas em registro exigem o Cisco IOS XE 17.6.1a ou versões posteriores. Recomenda-se o uso do Cisco IOS 17.12.2 ou posterior. Para as versões recomendadas, consulte a página Cisco Software Research. Procure a plataforma e selecione uma das versões sugeridas.
-
Os roteadores da série ISR4000 devem ser configurados com licenças de tecnologia de Comunicações Unificadas e de Segurança.
-
Os roteadores da série Catalyst Edge 8000 equipados com placas de voz ou DSPs requerem licenciamento DNA Advantage. Roteadores sem placas de voz ou DSPs exigem, no mínimo, uma licença DNA Essentials.
-
-
Crie uma configuração básica para sua plataforma que esteja de acordo com as políticas da sua empresa. Em particular, configure e verifique o seguinte:
-
Ntp
-
Acls
-
Autenticação de usuário e acesso remoto
-
DNS
-
Roteamento IP
-
Endereços IP
-
-
A rede para o Webex Calling deve usar um endereço IPv4.
-
Faça o upload do pacote de certificados raiz da Cisco para o gateway local.
Ao configurar o lado do locatário para se conectar com o Webex Calling, somente endereços baseados em SRV são suportados.
Configuração
| 1 |
Certifique-se de atribuir endereços IP válidos e roteáveis a todas as interfaces de Camada 3, por exemplo:
|
| 2 |
Proteja as credenciais de registro e STUN no roteador usando criptografia simétrica. Configure a chave de criptografia primária e o tipo de criptografia da seguinte forma:
|
| 3 |
Crie um ponto de confiança PKI provisório. Este ponto de confiança é necessário para configurar o TLS posteriormente. Para troncos baseados em registro, este ponto de confiança não requer um certificado - como é necessário para um tronco baseado em certificado. |
| 4 |
Habilite a exclusividade TLS 1.2 e especifique o ponto de confiança padrão usando os seguintes comandos de configuração. Atualize os parâmetros de transporte para garantir uma conexão segura e confiável para o registro: O comando
|
| 5 |
Instale o pacote de certificados raiz da Cisco, que inclui o certificado IdenTrust Commercial Root CA1 usado pelo Webex Calling. Use o comando crypto pki trustpool import clean url para baixar o pacote de certificados raiz da CA a partir da URL especificada e para limpar o pool de certificados da CA atual. Em seguida, instale o novo pacote de certificados: Se você precisar usar um proxy para acessar a internet via HTTPS, adicione a seguinte configuração antes de importar o pacote de CA: ip http client proxy-server yourproxy.com proxy-port 80 |
| 1 |
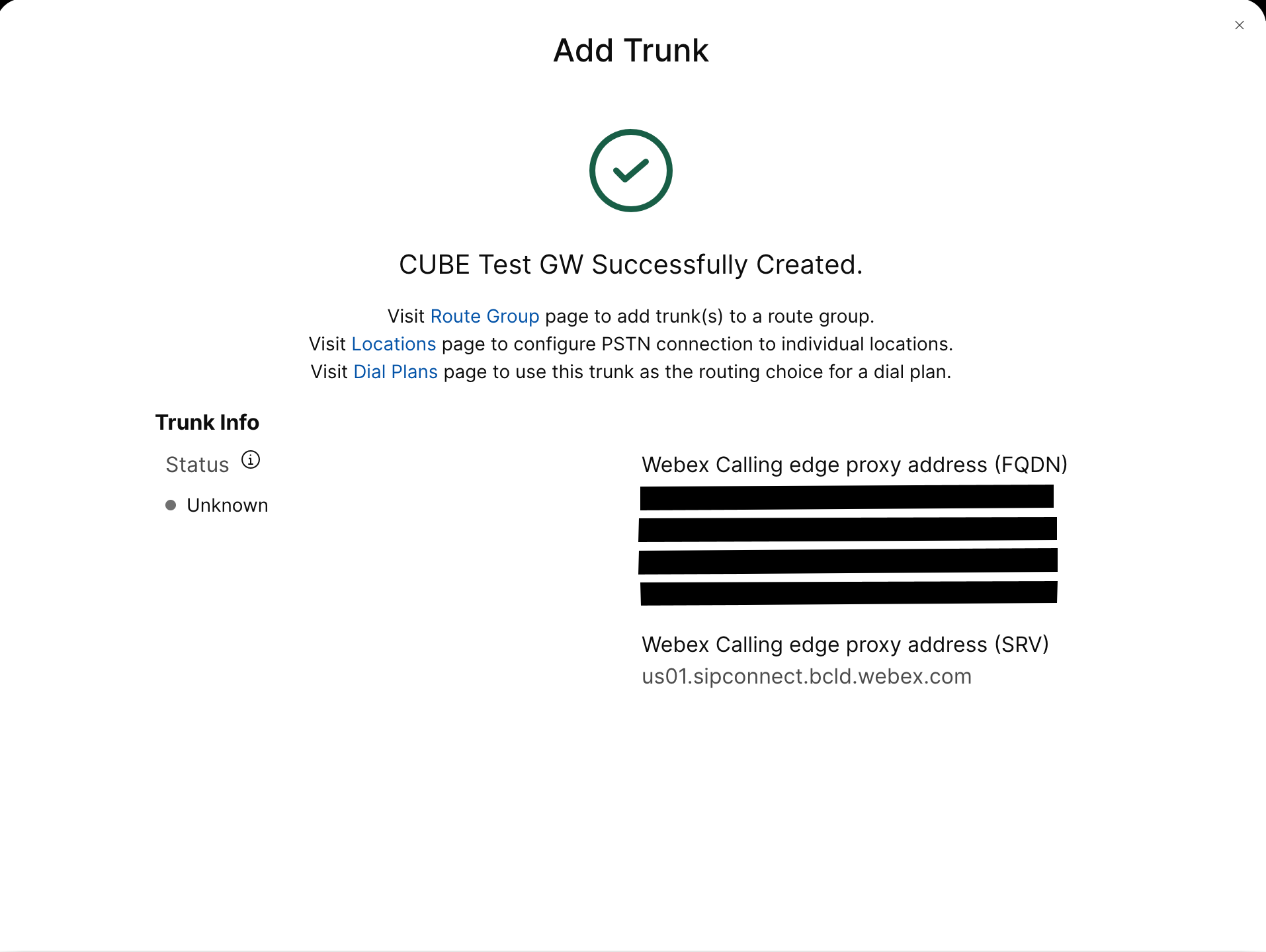
Criar um tronco PSTN baseado em registro para um local existente no Hub de Controle. Anote as informações do tronco que são fornecidas assim que o tronco for criado. Os detalhes destacados na ilustração são utilizados nas etapas de configuração deste guia. Para obter mais informações, consulte Configurar troncos, grupos de rotas e planos de discagem para Webex Calling. 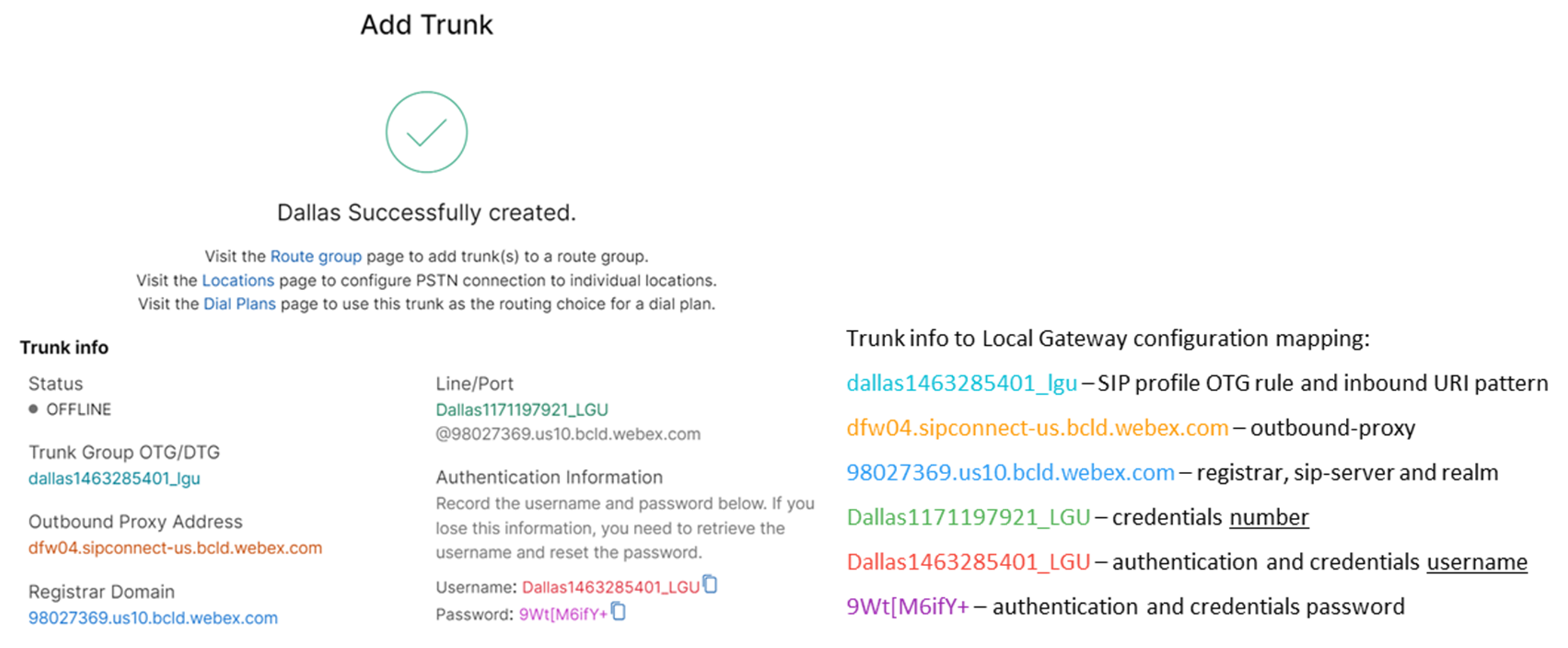 |
| 2 |
Insira os seguintes comandos para configurar o CUBE como um Gateway Local de Chamadas Webex: Aqui está uma explicação dos campos para a configuração:
Habilita os recursos do Cisco Unified Border Element (CUBE) na plataforma. estatísticas de mídiaPermite o monitoramento de mídia no Gateway local. estatísticas em massa de mídiaPermite que o avião de controle sondar o avião de dados para as estatísticas de chamada em massa. Para obter mais informações sobre esses comandos, consulte Mídia. permitir conexões sip para sipAtive a funcionalidade básica de agente de usuário SIP back-to-back do CUBE. Para obter mais informações, consulte Permitir conexões. Por padrão, o transporte de fax T.38 está ativado. Para obter mais informações, consulte protocolo de fax t38 (serviço de voz). Habilita o STUN (Session Traversal of UDP through NAT) globalmente.
Para obter mais informações, consulte stun flowdata agent-id e stun flowdata shared-secret. carga útil assimétrica completaConfigura o suporte a payloads assimétricos SIP para payloads DTMF e de codecs dinâmicos. Para obter mais informações, consulte carga útil assimétrica. oferta antecipada forçadaForça o Gateway Local a enviar informações SDP na mensagem INVITE inicial, em vez de esperar pelo reconhecimento do par vizinho. Para obter mais informações sobre este comando, consulte oferta-antecipada. |
| 3 |
Configure voice class codec 100 permitindo somente codecs G.711 para todos os troncos. Essa abordagem simples é adequada para a maioria das implementações. Caso necessário, outros tipos de codecs suportados pelos sistemas de origem e destino podem ser adicionados à lista. Soluções mais complexas envolvendo transcodificação usando módulos DSP são suportadas, mas não estão incluídas neste guia. Aqui está uma explicação dos campos para a configuração: codec de classe de voz 100Utilizado para permitir apenas codecs preferenciais para chamadas de tronco SIP. Para obter mais informações, consulte codec de classe de voz. |
| 4 |
Configure voice class stun-usage 100 para habilitar o ICE no tronco Webex Calling. Aqui está uma explicação dos campos para a configuração: uso de atordoamento gelo leveUtilizado para habilitar o ICE-Lite para todos os dial-peers do Webex Calling, permitindo a otimização de mídia sempre que possível. Para mais informações, consulte uso de atordoamento da classe de voz e uso de atordoamento gelo leve. A otimização de mídia é negociada sempre que possível. Se uma chamada exigir serviços de mídia na nuvem, como gravação, a mídia não poderá ser otimizada. |
| 5 |
Configure a política de criptografia de mídia para o tráfego do Webex. Aqui está uma explicação dos campos para a configuração: classe de voz srtp-crypto 100Especifica SHA1_80 como o único conjunto de cifras SRTP que o CUBE oferece no SDP em mensagens de oferta e resposta. O Webex Calling suporta apenas SHA1_80. Para obter mais informações, consulte classe de voz srtp-crypto. |
| 6 |
Configure um padrão para identificar chamadas para um tronco de Gateway Local com base no parâmetro de tronco de destino: Aqui está uma explicação dos campos para a configuração: aula de voz uri 100 golesDefine um padrão para associar um convite SIP recebido a um dial-peer de tronco também recebido. Ao inserir esse padrão, use dtg= seguido de Trunk. OTG/DTG Valor fornecido no Hub de Controle quando o tronco foi criado. Para obter mais informações, consulte voice class uri. |
| 7 |
Configure sip profile 100, que será usado para modificar mensagens SIP antes de serem enviadas para o Webex Calling.
Aqui está uma explicação dos campos para a configuração:
O provedor PSTN dos Estados Unidos ou do Canadá pode oferecer a verificação do ID do chamador para chamadas de spam e fraude, com a configuração adicional mencionada no artigo Indicação de chamada de spam ou fraude no Webex Calling. |
| 8 |
Configurar tronco de chamadas Webex: |
| 9 |
Para configurar dispositivos de rede como o CUBE e encaminhar cabeçalhos do Protocolo de Iniciação de Sessão (SIP) que o dispositivo não processa, use estes comandos. Esses comandos permitem que o dispositivo transmita cabeçalhos SIP não suportados, incluindo cabeçalhos de geolocalização e PIDF-LO (Presence Information Data Format - Location Object), no gateway local. Essa funcionalidade auxilia os serviços Nomadic E911, garantindo que as informações críticas de localização sejam preservadas e encaminhadas corretamente. |
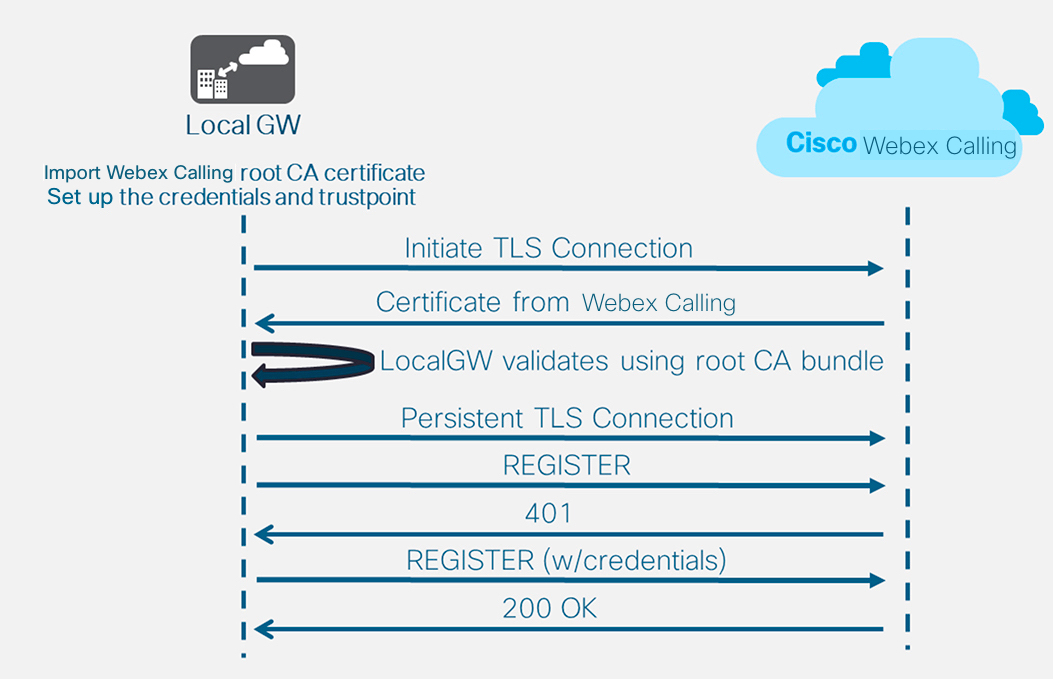
Depois de definir o locatário 100 e configurar um dial-peer VoIP SIP, o gateway inicia uma conexão TLS com o Webex Calling. Nesse ponto, o SBC de acesso apresenta seu certificado ao Gateway Local. O Gateway Local valida o certificado SBC de acesso ao Webex Calling usando o pacote raiz da CA que foi atualizado anteriormente. Se o certificado for reconhecido, uma sessão TLS persistente será estabelecida entre o Gateway Local e o SBC de acesso ao Webex Calling. O Gateway Local consegue então usar essa conexão segura para se registrar no SBC de acesso do Webex. Quando o cadastro é solicitado para autenticação:
-
Os parâmetros username, passworde realm da configuração credentials são usados na resposta.
-
As regras de modificação no perfil SIP 100 são usadas para converter URLs SIPS de volta para SIP.
O registro é considerado bem-sucedido quando um código 200 OK é recebido do SBC de acesso.
Após criar um tronco para o Webex Calling conforme descrito acima, utilize a seguinte configuração para criar um tronco não criptografado para um provedor PSTN baseado em SIP:
Se o seu provedor de serviços oferecer um tronco PSTN seguro, você poderá seguir uma configuração semelhante à detalhada acima para o tronco de chamadas do Webex. O CUBE oferece suporte ao roteamento seguro de chamadas.
Se você estiver usando um TDM / Tronco PSTN ISDN, pule para a próxima seção Configurar Gateway Local com tronco PSTN TDM.
Para configurar interfaces TDM para pernas de chamadas PSTN nos gateways Cisco TDM-SIP, consulte Configurando ISDN PRI.
| 1 |
Configure o seguinte URI de classe de voz para identificar chamadas recebidas do tronco PSTN: Aqui está uma explicação dos campos para a configuração: aula de voz uri 200 golesDefine um padrão para associar um convite SIP recebido a um dial-peer de tronco também recebido. Ao inserir esse padrão, use o endereço IP do seu gateway PSTN. Para obter mais informações, consulte voice class uri. |
| 2 |
Configure o seguinte dial-peer IP PSTN: Aqui está uma explicação dos campos para a configuração: Define um dial-peer VoIP com uma tag de 200 e fornece uma descrição significativa para facilitar o gerenciamento e a resolução de problemas. Para obter mais informações, consulte dial-peer voice. padrão de destino RUIM.RUIMÉ necessário um padrão de destino fictício ao rotear chamadas de saída usando um grupo de dial-peers de entrada. Neste caso, qualquer padrão de destino válido pode ser usado. Para obter mais informações, consulte destination-pattern (interface). sessão protocolo sipv2Especifica que este dial-peer lida com as pernas de chamada SIP. Para obter mais informações, consulte protocolo de sessão (dial peer). destino da sessão ipv4: 192.168.80.13Especifica o endereço de destino para chamadas enviadas ao provedor PSTN. Isso pode ser um endereço IP ou um nome de host DNS. Para obter mais informações, consulte destino da sessão (VoIP dial peer). URI de entrada via 200Especifica a classe de voz usada para corresponder as chamadas recebidas a este dial-peer usando o URI do cabeçalho INVITE VIA. Para obter mais informações, consulte URL de entrada. classe de voz gole id afirmado pai
(Opcional) Ativa o processamento do cabeçalho P-Asserted-Identity e controla como ele é usado para o tronco PSTN. Se este comando for utilizado, a identidade da parte que está chamando, fornecida pelo dial-peer de entrada, será usada nos cabeçalhos From e P-Asserted-Identity de saída. Caso este comando não seja utilizado, a identidade da parte chamadora fornecida pelo dial-peer de entrada será utilizada nos cabeçalhos From e Remote-Party-ID de saída. Para obter mais informações, consulte voice-class sip asserted-id. vincular interface de origem de controle GigabitEthernet0/0/0
Configura a interface de origem e o endereço IP associado para mensagens enviadas à PSTN. Para obter mais informações, consulte bind. vincular interface de origem de mídia GigabitEthernet0/0/0Configura a interface de origem e o endereço IP associado para mídia enviada à PSTN. Para obter mais informações, consulte bind. codec de classe de voz 100Configura o dial-peer para usar a lista de filtros de codec comum 100. Para obter mais informações, consulte codec de classe de voz. dtmf-relay rtp-nteDefine o RTP-NTE (RFC2833) como o recurso DTMF esperado no retorno de chamada. Para obter mais informações, consulte DTMF Relay (Voz sobre IP). sem vadDesativa a detecção de atividade de voz. Para obter mais informações, consulte vad (dial peer). |
| 3 |
Se você estiver configurando seu Gateway Local para rotear chamadas somente entre o Webex Calling e a PSTN, adicione a seguinte configuração de roteamento de chamadas. Se você estiver configurando seu Gateway Local com uma plataforma Unified Communications Manager, pule para a próxima seção. |
Após criar um tronco para o Webex Calling, utilize a seguinte configuração para criar um tronco TDM para o seu serviço PSTN com roteamento de chamadas em loopback, permitindo a otimização de mídia na chamada do Webex.
Se você não precisa de otimização de mídia IP, siga os passos de configuração para um tronco SIP PSTN. Utilize uma porta de voz e um dial-peer POTS (conforme mostrado nas etapas 2 e 3) em vez do dial-peer VoIP PSTN.
| 1 |
A configuração de dial-peer de loopback usa grupos de dial-peers e tags de roteamento de chamadas para garantir que as chamadas sejam transmitidas corretamente entre o Webex e a PSTN, sem criar loops de roteamento de chamadas. Configure as seguintes regras de tradução que serão usadas para adicionar e remover as tags de roteamento de chamadas: Aqui está uma explicação dos campos para a configuração: regra de tradução de vozUtiliza expressões regulares definidas em regras para adicionar ou remover tags de roteamento de chamadas. Os dígitos acima da decimal ('A') são usados para maior clareza na resolução de problemas. Nessa configuração, a tag adicionada pelo translation-profile 100 é usada para direcionar as chamadas do Webex Calling para a PSTN por meio dos dial-peers de loopback. Da mesma forma, a tag adicionada pelo perfil de tradução 200 é usada para direcionar chamadas da PSTN para o Webex Calling. Os perfis de tradução 11 e 12 removem essas tags antes de encaminhar as chamadas para os troncos Webex e PSTN, respectivamente. Este exemplo pressupõe que os números chamados pelo Webex Calling sejam apresentados em +E.164 formatar. A regra 100 remove o primeiro + Para manter um número chamado válido. A regra 12 adiciona então um ou mais dígitos de roteamento nacional ou internacional ao remover a etiqueta. Use dígitos que correspondam ao seu plano de discagem nacional ISDN local. Se o Webex Calling apresentar números no formato nacional, ajuste as regras 100 e 12 para simplesmente adicionar e remover a tag de roteamento, respectivamente. Para obter mais informações, consulte voice translation-profile e voice translation-rule. |
| 2 |
Configure as portas da interface de voz TDM conforme exigido pelo tipo de tronco e protocolo utilizado. Para obter mais informações, consulte Configurando ISDN PRI. Por exemplo, a configuração básica de uma interface ISDN de taxa primária instalada no slot NIM 2 de um dispositivo pode incluir o seguinte: |
| 3 |
Configure o seguinte dial-peer TDM PSTN: Aqui está uma explicação dos campos para a configuração: Define um dial-peer VoIP com a tag 200 e fornece uma descrição significativa para facilitar o gerenciamento e a resolução de problemas. Para obter mais informações, consulte dial-peer voice. padrão de destino RUIM.RUIMÉ necessário um padrão de destino fictício ao rotear chamadas de saída usando um grupo de dial-peers de entrada. Neste caso, qualquer padrão de destino válido pode ser usado. Para obter mais informações, consulte destination-pattern (interface). perfil de tradução recebido 200Atribui o perfil de tradução que adicionará uma etiqueta de encaminhamento de chamadas ao número chamado de entrada. discagem direta para dentroEncaminha a chamada sem fornecer um tom de discagem secundário. Para obter mais informações, consulte direct-inward-dial. porta 0/2/0:15A porta de voz física associada a este dial-peer. |
| 4 |
Para habilitar a otimização de mídia dos caminhos IP para gateways locais com fluxos de chamadas TDM-IP, você pode modificar o roteamento de chamadas introduzindo um conjunto de dial-peers de loopback internos entre o Webex Calling e os troncos PSTN. Configure os seguintes dial-peers de loopback. Neste caso, todas as chamadas recebidas serão inicialmente encaminhadas para o dial-peer 10 e, a partir daí, para o dial-peer 11 ou 12, com base na tag de roteamento aplicada. Após a remoção da etiqueta de roteamento, as chamadas serão encaminhadas para o tronco de saída usando grupos de dial-peer. Aqui está uma explicação dos campos para a configuração: Define um dial-peer VoIP e fornece uma descrição significativa para facilitar o gerenciamento e a resolução de problemas. Para obter mais informações, consulte dial-peer voice. perfil de tradução recebido 11Aplica o perfil de tradução definido anteriormente para remover a etiqueta de roteamento de chamadas antes de passar para o tronco de saída. padrão de destino RUIM.RUIMÉ necessário um padrão de destino fictício ao rotear chamadas de saída usando um grupo de dial-peers de entrada. Para obter mais informações, consulte destination-pattern (interface). sessão protocolo sipv2Especifica que este dial-peer lida com as pernas de chamada SIP. Para obter mais informações, consulte protocolo de sessão (dial peer). destino da sessão ipv4: 192.168.80.14Especifica o endereço da interface do roteador local como o destino da chamada para o loopback. Para obter mais informações, consulte destino da sessão (voip dial peer). vincular interface de origem de controle GigabitEthernet0/0/0Configura a interface de origem e o endereço IP associado para mensagens enviadas através do loopback. Para obter mais informações, consulte bind. vincular interface de origem de mídia GigabitEthernet0/0/0Configura a interface de origem e o endereço IP associado para mídias enviadas através do loopback. Para obter mais informações, consulte bind. dtmf-relay rtp-nteDefine o RTP-NTE (RFC2833) como o recurso DTMF esperado no retorno de chamada. Para obter mais informações, consulte DTMF Relay (Voz sobre IP). codec g711alaw Força todas as chamadas PSTN a utilizarem G.711. Selecione a-law ou u-law para corresponder ao método de compressão utilizado pelo seu serviço ISDN. sem vadDesativa a detecção de atividade de voz. Para obter mais informações, consulte vad (dial peer). |
| 5 |
Adicione a seguinte configuração de roteamento de chamadas: Isso conclui a configuração do seu Gateway Local. Salve a configuração e recarregue a plataforma se esta for a primeira vez que os recursos do CUBE são configurados.
|
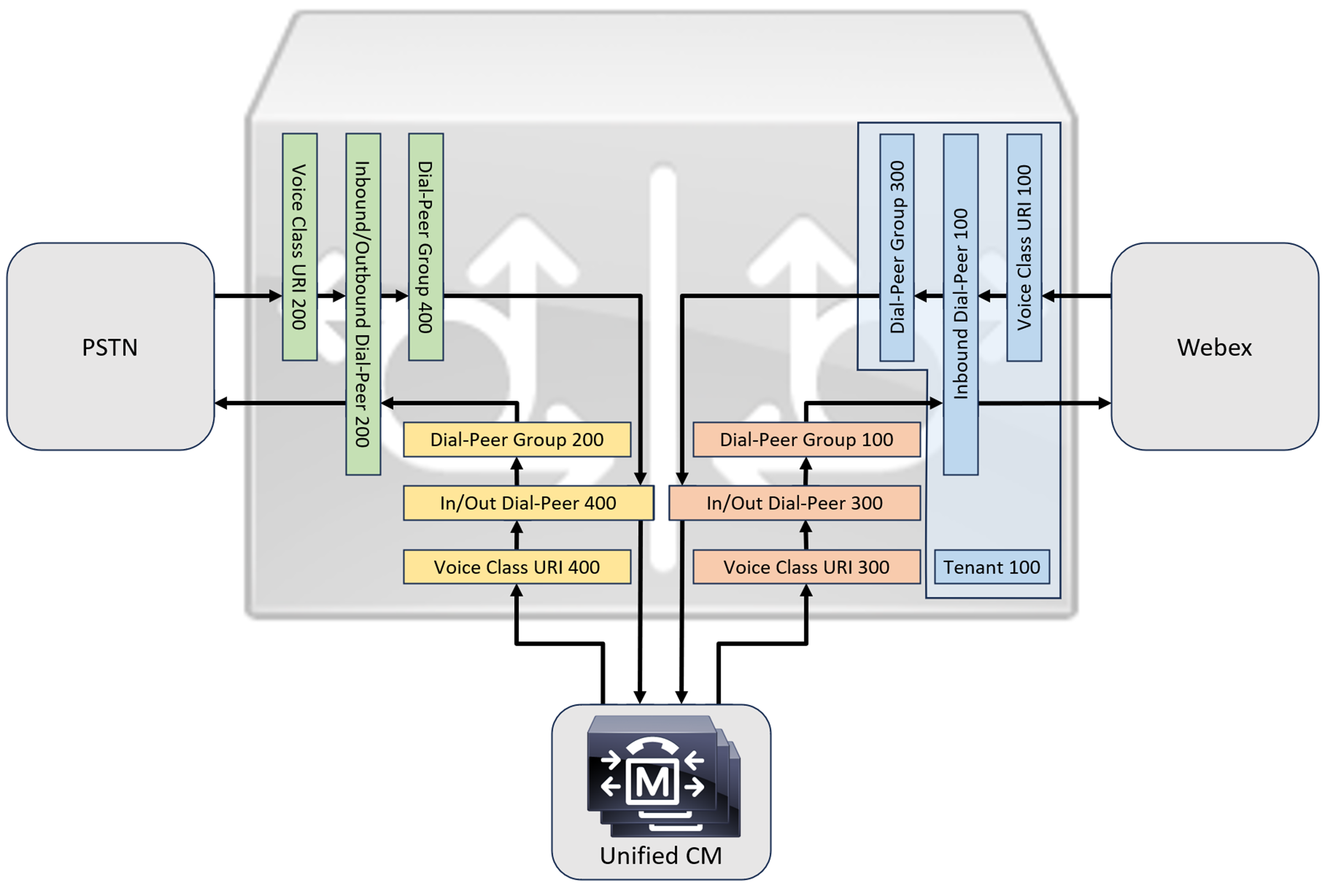
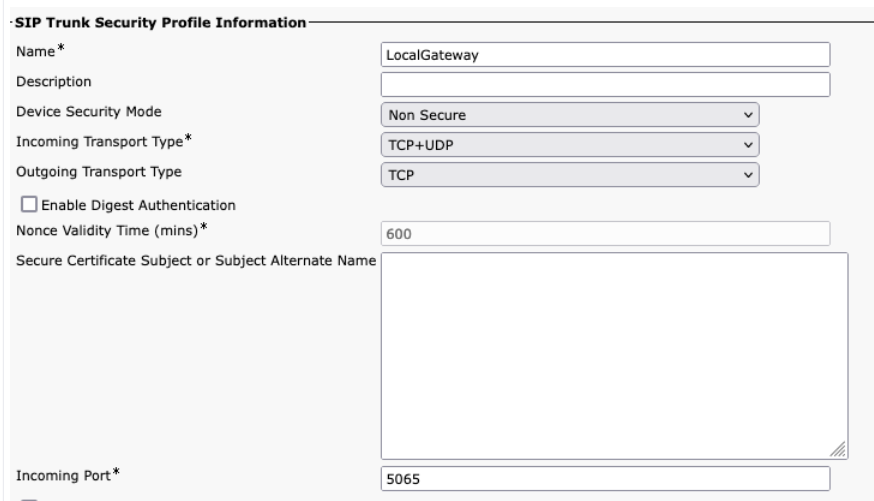
A configuração de chamadas PSTN-Webex nas seções anteriores pode ser modificada para incluir troncos adicionais em um cluster Cisco Unified Communications Manager (UCM). Neste caso, todas as chamadas são encaminhadas através do Unified CM. As chamadas originadas no UCM pela porta 5060 são encaminhadas para a PSTN e as chamadas originadas pela porta 5065 são encaminhadas para o Webex Calling. As seguintes configurações incrementais podem ser adicionadas para incluir esse cenário de chamada.
Ao criar o tronco de chamadas Webex no Unified CM, certifique-se de configurar a porta de entrada nas configurações do Perfil de Segurança do Tronco SIP para 5065. Isso permite o recebimento de mensagens na porta 5065 e preenche o cabeçalho VIA com esse valor ao enviar mensagens para o Gateway Local.
| 1 |
Configure as seguintes URIs de classe de voz: |
| 2 |
Configure os seguintes registros DNS para especificar o roteamento SRV para hosts do Unified CM: O IOS XE utiliza esses registros para determinar localmente os hosts e portas UCM de destino. Com essa configuração, não é necessário configurar registros no seu sistema DNS. Se preferir usar seu próprio servidor DNS, essas configurações locais não são necessárias. Aqui está uma explicação dos campos para a configuração: O comando a seguir cria um registro de recurso DNS SRV. Crie um registro para cada host e tronco UCM: ip host _sip._udp.pstntocucm.io srv 2 1 5060 ucmsub5.mydomain.com _sip._udp.pstntocucm.io: Nome do registro de recurso SRV 2: A prioridade do registro de recursos SRV 1: O peso do registro de recursos SRV 5060: O número da porta a ser usada para o host de destino neste registro de recurso. ucmsub5.mydomain.com: O host de destino do registro de recursos Para resolver os nomes de host de destino dos registros de recursos, crie registros DNS A locais. Por exemplo: host ip ucmsub5.mydomain.com 192.168.80.65 host ip: Cria um registro no banco de dados local do IOS XE. ucmsub5.mydomain.com: O nome do host do registro A. 192.168.80.65: O endereço IP do host. Crie os registros de recursos SRV e os registros A para refletir seu ambiente UCM e a estratégia de distribuição de chamadas preferida. |
| 3 |
Configure os seguintes dial-peers: |
| 4 |
Adicione o roteamento de chamadas usando as seguintes configurações: |
As Assinaturas de Diagnóstico (DS) detectam proativamente problemas observados no Gateway local baseado no IOS XE e gera notificação de e-mail, syslog ou mensagem terminal do evento. Você também pode instalar o DS para automatizar a coleta de dados de diagnóstico e transferir os dados coletados para o caso no Cisco TAC, acelerando o tempo de resolução.
As assinaturas de diagnóstico (DS) são arquivos XML que contêm informações sobre eventos de acionador de problemas e ações a serem tomadas para informar, solucionar o problema e solucionar o problema. Você pode definir a lógica de detecção de problemas usando mensagens syslog, eventos SNMP e por meio do monitoramento periódico de saídas de comandos show específicos.
Os tipos de ação incluem a coleta de saídas mostrar comandos:
-
Gerando um arquivo de registro consolidado
-
Envio do arquivo para um local de rede fornecido pelo usuário, como um servidor HTTPS, SCP ou FTP.
Os engenheiros do TAC autorizam os arquivos DS e os assinam digitalmente para uma proteção de integridade. Cada arquivo DS possui uma ID numérica exclusiva atribuída pelo sistema. AFerramenta de Busca de Assinaturas de Diagnóstico (DSLT) é uma fonte única para encontrar assinaturas aplicáveis para monitoramento e solução de diversos problemas.
Antes de você começar:
-
Não edite o arquivo DS que você baixa do DSLT. Os arquivos que você modifica falham na instalação devido ao erro de verificação de integridade.
-
Um servidor de Protocolo de Transferência de E-mail Simples (SMTP) que você precisa para o Gateway Local enviar notificações por e-mail.
-
Certifique-se de que o Gateway Local está executando o IOS XE 17.6.1 ou superior se você desejar usar o servidor SMTP seguro para notificações por e-mail.
Pré-requisitos
Gateway local executando IOS XE 17.6.1a ou superior
-
As Assinaturas de diagnóstico estão ativadas por padrão.
-
Configure o servidor de e-mail seguro para ser usado no envio de notificações proativas caso o dispositivo esteja executando o Cisco IOS XE 17.6.1a ou superior.
configure terminal call-home mail-server :@ priority 1 secure tls end -
Configure a variável de ambiente ds_email com o endereço de e-mail do administrador para notificá-lo.
configure terminal call-home diagnostic-signature environment ds_email end
A seguir, é apresentado um exemplo de configuração de um Gateway Local em execução no Cisco IOS XE 17.6.1a ou superior para enviar notificações proativas para tacfaststart@gmail.com usando o Gmail como servidor SMTP seguro:
Recomendamos que você utilize o Cisco IOS XE Bengaluru versão 17.6.x ou posterior.
call-home
mail-server tacfaststart:password@smtp.gmail.com priority 1 secure tls
diagnostic-signature
environment ds_email "tacfaststart@gmail.com" Um Gateway local em execução no software Cisco IOS XE não é um cliente do Gmail comum baseado na web que suporta o OAuth, então é preciso configurar uma configuração específica de conta de Gmail e fornecer permissão específica para que o e-mail do dispositivo seja processado corretamente:
-
Acesse e ative a configuração Acesso a aplicativos menos seguros.
-
Responda "Sim, foi eu" quando você recebeu um e-mail do Gmail indicando "O Google impediu alguém de entrar na sua conta usando um aplicativo que não é o Google".
Instalar assinaturas de diagnóstico para monitoramento proativo
Monitoramento de alta utilização da CPU
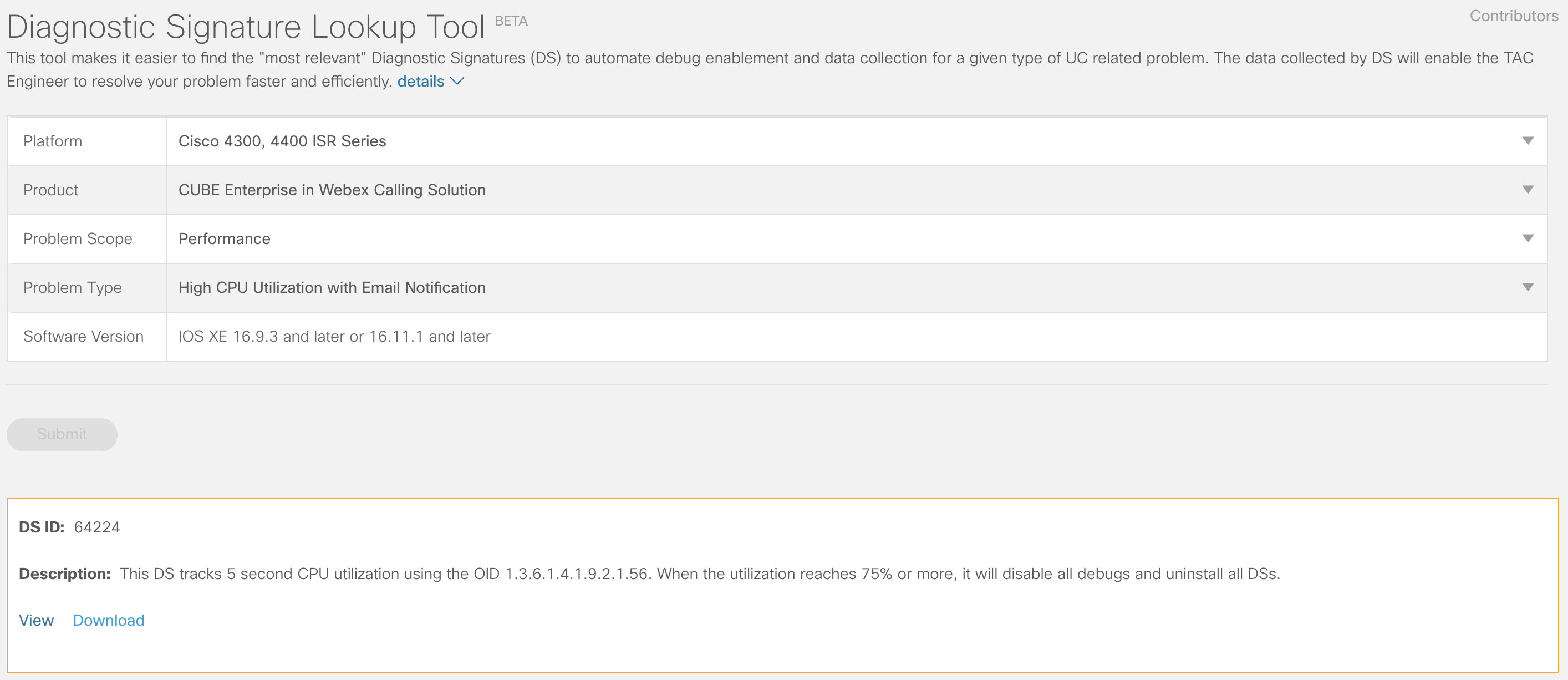
Este DS monitora a utilização da CPU por cinco segundos usando o OID SNMP. 1.3.6.1.4.1.9.2.1.56. Quando a utilização atingir 75% ou mais, ela desativa todas as depurações e desinstala todas as assinaturas de diagnóstico que estão instaladas no Gateway local. Use as etapas abaixo para instalar a assinatura.
-
Use o comando show snmp para habilitar o SNMP. Se você não habilitar, configure o comando snmp-server manager.
show snmp %SNMP agent not enabled config t snmp-server manager end show snmp Chassis: ABCDEFGHIGK 149655 SNMP packets input 0 Bad SNMP version errors 1 Unknown community name 0 Illegal operation for community name supplied 0 Encoding errors 37763 Number of requested variables 2 Number of altered variables 34560 Get-request PDUs 138 Get-next PDUs 2 Set-request PDUs 0 Input queue packet drops (Maximum queue size 1000) 158277 SNMP packets output 0 Too big errors (Maximum packet size 1500) 20 No such name errors 0 Bad values errors 0 General errors 7998 Response PDUs 10280 Trap PDUs Packets currently in SNMP process input queue: 0 SNMP global trap: enabled -
Baixe o DS 64224 usando as seguintes opções suspensas na Ferramenta de pesquisa de assinaturas de diagnóstico:
Nome do campo
Valor do campo
Plataforma
Cisco 4300, 4400 ISR Series ou Cisco CSR 1000V Series
Produto
CUBE Enterprise na solução do Webex Calling
Escopo do problema
Desempenho
Tipo de problema
Alta utilização da CPU com notificação por e-mail.
-
Copie o arquivo DS XML para o flash do Gateway local.
LocalGateway# copy ftp://username:password@/DS_64224.xml bootflash:O exemplo a seguir mostra a cópia do arquivo de um servidor FTP para o Gateway Local.
copy ftp://user:pwd@192.0.2.12/DS_64224.xml bootflash: Accessing ftp://*:*@ 192.0.2.12/DS_64224.xml...! [OK - 3571/4096 bytes] 3571 bytes copied in 0.064 secs (55797 bytes/sec) -
Instale o arquivo DS XML no Gateway local.
call-home diagnostic-signature load DS_64224.xml Load file DS_64224.xml success -
Use o comando mostrar assinatura de diagnóstico de chamada de casa para verificar se a assinatura foi instalada com êxito. A coluna de status deve ter um valor "registrado".
show call-home diagnostic-signature Current diagnostic-signature settings: Diagnostic-signature: enabled Profile: CiscoTAC-1 (status: ACTIVE) Downloading URL(s): https://tools.cisco.com/its/service/oddce/services/DDCEService Environment variable: ds_email: username@gmail.comBaixe o DSes:
ID de DS
Nome DS
Revisão
Status
Última atualização (GMT+00:00)
64224
DS_LGW_CPU_MON75
0.0.10
Registrado
2020-11-07 22:05:33
Quando acionada, esta assinatura desinstala todos os DSs em execução, incluindo ela própria. Caso necessário, reinstale o DS 64224 para continuar monitorando a alta utilização da CPU no Gateway Local.
Monitoramento de registro de tronco SIP
Este DS verifica a irretribuição de um gateway local Tronco SIP com Webex Calling nuvem a cada 60 segundos. Assim que o evento de cancelamento de registro for detectado, o programa gerará uma notificação por e-mail e no syslog e se desinstalará após duas ocorrências de cancelamento de registro. Siga os passos abaixo para instalar a assinatura:
-
Baixe o DS 64117 usando as seguintes opções suspensas na Ferramenta de pesquisa de assinaturas de diagnóstico:
Nome do campo
Valor do campo
Plataforma
Cisco 4300, 4400 ISR Series ou Cisco CSR 1000V Series
Produto
CUBE Enterprise na solução do Webex Calling
Escopo do problema
SIP-SIP
Tipo de problema
Tronco SIP não-aviso com a notificação por e-mail.
-
Copie o arquivo DS XML para o Gateway local.
copy ftp://username:password@/DS_64117.xml bootflash: -
Instale o arquivo DS XML no Gateway local.
call-home diagnostic-signature load DS_64117.xml Load file DS_64117.xml success LocalGateway# -
Use o comando mostrar assinatura de diagnóstico de chamada de casa para verificar se a assinatura foi instalada com êxito. A coluna status deve ter um valor "registrado".
Monitorando desconectações anormals de chamada
Esta assinatura digital utiliza sondagem SNMP a cada 10 minutos para detectar desconexões anormais de chamadas com erros SIP 403, 488 e 503. Se o incremento na contagem de erros for maior ou igual a 5 em relação à última sondagem, ela gera um registro no syslog e uma notificação por e-mail. Siga os passos abaixo para instalar a assinatura.
-
Use o comando show snmp para verificar se o SNMP está habilitado. Se não estiver habilitado, configure o comando snmp-server manager.
show snmp %SNMP agent not enabled config t snmp-server manager end show snmp Chassis: ABCDEFGHIGK 149655 SNMP packets input 0 Bad SNMP version errors 1 Unknown community name 0 Illegal operation for community name supplied 0 Encoding errors 37763 Number of requested variables 2 Number of altered variables 34560 Get-request PDUs 138 Get-next PDUs 2 Set-request PDUs 0 Input queue packet drops (Maximum queue size 1000) 158277 SNMP packets output 0 Too big errors (Maximum packet size 1500) 20 No such name errors 0 Bad values errors 0 General errors 7998 Response PDUs 10280 Trap PDUs Packets currently in SNMP process input queue: 0 SNMP global trap: enabled -
Baixe o DS 65221 usando as seguintes opções na Ferramenta de pesquisa de assinaturas de diagnóstico:
Nome do campo
Valor do campo
Plataforma
Cisco 4300, 4400 ISR Series ou Cisco CSR 1000V Series
Produto
CUBE Enterprise na solução do Webex Calling
Escopo do problema
Desempenho
Tipo de problema
Detecção anormal de desconexão de chamada SIP com e-mail e notificação Syslog.
-
Copie o arquivo DS XML para o Gateway local.
copy ftp://username:password@/DS_65221.xml bootflash: -
Instale o arquivo DS XML no Gateway local.
call-home diagnostic-signature load DS_65221.xml Load file DS_65221.xml success -
Use o comando mostrar assinatura de diagnóstico de chamada de casa para verificar se a assinatura foi instalada com êxito. A coluna status deve ter um valor "registrado".
Instalar assinaturas de diagnóstico para solucionar um problema
Use assinaturas de diagnóstico (DS) para resolver os problemas rapidamente. Os engenheiros do TAC da Cisco criaram várias assinaturas que permitem as depurações necessárias que são necessárias para solucionar um determinado problema, detectar a ocorrência do problema, coletar o conjunto certo de dados de diagnóstico e transferir os dados automaticamente para o caso do CISCO TAC. As assinaturas de diagnóstico (DS) eliminam a necessidade de verificar manualmente a ocorrência do problema e facilitam muito a resolução de problemas intermitentes e transitórios.
Você pode usar a Ferramenta de pesquisa de assinaturas de diagnóstico para encontrar as assinaturas aplicáveis e instalá-las para auto-resolver um determinado problema ou você pode instalar a assinatura que é recomendada pelo engenheiro de TAC como parte do envolvimento do suporte.
Aqui está um exemplo de como encontrar e instalar um DS para detectar a ocorrência "%VOICE_IEC-3-GW: CCAPI: Erro interno (limite de pico de chamadas): IEC=1.1.181.1.29.0" syslog e automatize a coleta de dados de diagnóstico usando as seguintes etapas:
-
Configure uma variável de ambiente DS adicional ds_fsurl_prefixque seja o caminho do servidor de arquivos do Cisco TAC (cxd.cisco.com) para o qual os dados de diagnóstico coletados serão enviados. O nome de usuário no caminho do arquivo é o número do caso e a senha é o token de upload de arquivo, que pode ser obtido em Support Case Manager no seguinte comando. O token de upload de arquivo pode ser gerado na seção Attachments do Support Case Manager, conforme necessário.
configure terminal call-home diagnostic-signature LocalGateway(cfg-call-home-diag-sign)environment ds_fsurl_prefix "scp://:@cxd.cisco.com" endExemplo:
call-home diagnostic-signature environment ds_fsurl_prefix " environment ds_fsurl_prefix "scp://612345678:abcdefghijklmnop@cxd.cisco.com" -
Certifique-se de que o SNMP está habilitado usando o comando show snmp. Se não estiver habilitado, configure o comando snmp-server manager.
show snmp %SNMP agent not enabled config t snmp-server manager end -
Certifique-se de instalar o monitoramento de alta CPU DS 64224 como uma medida proativa para desativar todas as assinaturas de depuração e diagnósticos durante o momento de alta utilização da CPU. Baixe o DS 64224 usando as seguintes opções na Ferramenta de pesquisa de assinaturas de diagnóstico:
Nome do campo
Valor do campo
Plataforma
Cisco 4300, 4400 ISR Series ou Cisco CSR 1000V Series
Produto
CUBE Enterprise na solução do Webex Calling
Escopo do problema
Desempenho
Tipo de problema
Alta utilização da CPU com notificação por e-mail.
-
Baixe o DS 65095 usando as seguintes opções na Ferramenta de pesquisa de assinaturas de diagnóstico:
Nome do campo
Valor do campo
Plataforma
Cisco 4300, 4400 ISR Series ou Cisco CSR 1000V Series
Produto
CUBE Enterprise na solução do Webex Calling
Escopo do problema
Syslogs
Tipo de problema
Syslog - %VOICE_IEC-3-GW: CCAPI: Erro interno (limite de pico de chamadas): IEC=1.1.181.1.29.0
-
Copie os arquivos DS XML para o Gateway local.
copy ftp://username:password@/DS_64224.xml bootflash: copy ftp://username:password@/DS_65095.xml bootflash: -
Instale o monitoramento de Alta CPU DS 64224 e, em seguida, o arquivo XML do DS 65095 no Gateway local.
call-home diagnostic-signature load DS_64224.xml Load file DS_64224.xml success call-home diagnostic-signature load DS_65095.xml Load file DS_65095.xml success -
Verifique se a assinatura foi instalada com sucesso usando o comando show call-home diagnostic-signature. A coluna status deve ter um valor "registrado".
show call-home diagnostic-signature Current diagnostic-signature settings: Diagnostic-signature: enabled Profile: CiscoTAC-1 (status: ACTIVE) Downloading URL(s): https://tools.cisco.com/its/service/oddce/services/DDCEService Environment variable: ds_email: username@gmail.com ds_fsurl_prefix: scp://612345678:abcdefghijklmnop@cxd.cisco.comDSes baixados:
ID de DS
Nome DS
Revisão
Status
Última atualização (GMT+00:00)
64224
00:07:45
DS_LGW_CPU_MON75
0.0.10
Registrado
2020-11-08
65095
00:12:53
DS_LGW_IEC_Call_spike_threshold
0.0.12
Registrado
2020-11-08
Verificar a execução de assinaturas de diagnóstico
No comando a seguir, a coluna “Status” do comando show call-home diagnostic-signature muda para “running” enquanto o Gateway Local executa a ação definida na assinatura. O resultado de mostrar as estatísticas de diagnóstico de chamada de casa é a melhor maneira de verificar se uma assinatura de diagnóstico detecta um evento de interesse e executa a ação. A coluna "Acionado/Máximo/Desinstalação" indica o número de vezes que a assinatura dada acionou um evento, o número máximo de vezes que é definido para detectar um evento e se a assinatura desinstala-se depois de detectar o número máximo de eventos acionados.
show call-home diagnostic-signature
Current diagnostic-signature settings:
Diagnostic-signature: enabled
Profile: CiscoTAC-1 (status: ACTIVE)
Downloading URL(s): https://tools.cisco.com/its/service/oddce/services/DDCEService
Environment variable:
ds_email: carunach@cisco.com
ds_fsurl_prefix: scp://612345678:abcdefghijklmnop@cxd.cisco.com DSes baixados:
|
ID de DS |
Nome DS |
Revisão |
Status |
Última atualização (GMT+00:00) |
|---|---|---|---|---|
| 64224 |
DS_LGW_CPU_MON75 |
0.0.10 |
Registrado |
2020-11-08 00:07:45 |
|
65095 |
DS_LGW_IEC_Call_spike_threshold |
0.0.12 |
Em execução |
2020-11-08 00:12:53 |
mostrar estatísticas de assinatura do diagnóstico de chamada de casa
|
ID de DS |
Nome DS |
Provocado/Max/Deinstall |
Tempo médio de execução (segundos) |
Tempo máximo de execução (segundos) |
|---|---|---|---|---|
| 64224 |
DS_LGW_CPU_MON75 |
0/0/N |
0.000 |
0.000 |
|
65095 |
DS_LGW_IEC_Call_spike_threshold |
1/20/Y |
23.053 |
23.053 |
O e-mail de notificação que é enviado durante a execução da assinatura de diagnóstico contém informações importantes como tipo de problema, detalhes do dispositivo, versão do software, configuração em execução e mostra saídas de comando que são relevantes para solucionar o problema dado.
Desinstalar assinaturas de diagnóstico
Use assinaturas de Diagnóstico para fins de solução de problemas são tipicamente definidas para desinstalar após a detecção de algumas ocorrências de problemas. Se você deseja desinstalar uma assinatura manualmente, recupere o ID DS da saída do comando show call-home diagnostic-signature e execute o seguinte comando:
call-home diagnostic-signature deinstall
Exemplo:
call-home diagnostic-signature deinstall 64224
Novas assinaturas são adicionadas à Ferramenta de pesquisa de assinaturas de diagnóstico periodicamente, com base em problemas que são geralmente observados nas implantações. Atualmente, o TAC não oferece suporte a solicitações de criação de novas assinaturas personalizadas.
Para um melhor gerenciamento dos gateways Cisco IOS XE, recomendamos que você registre e gerencie os gateways por meio do Control Hub. É uma configuração opcional. Após a inscrição, você pode usar a opção de validação de configuração no Control Hub para validar a configuração do seu Gateway Local e identificar quaisquer problemas de configuração. Atualmente, apenas os troncos baseados em registro suportam essa funcionalidade.
Para obter mais informações, consulte o seguinte:
Esta seção descreve como configurar um Cisco Unified Border Element (CUBE) como um gateway local para chamadas Webex usando um tronco SIP TLS mútuo (mTLS) baseado em certificado. A primeira parte deste documento ilustra como configurar um gateway PSTN simples. Neste caso, todas as chamadas da PSTN são encaminhadas para o Webex Calling e todas as chamadas do Webex Calling são encaminhadas para a PSTN. A imagem a seguir destaca essa solução e a configuração de roteamento de chamadas de alto nível que será adotada.
Neste projeto, são utilizadas as seguintes configurações principais:
-
inquilinos da classe de voz: Used para criar configurações específicas do tronco.
-
uri da classe de voz: Utilizado para classificar mensagens SIP para a seleção de um dial-peer de entrada.
-
dial-peer de entrada: Fornece tratamento para mensagens SIP de entrada e determina a rota de saída usando um grupo de dial-peers.
-
grupo de pares de discagem: Define os dial-peers de saída usados para o encaminhamento de chamadas subsequentes.
-
discagem de saída: Fornece tratamento para mensagens SIP de saída e as encaminha para o destino necessário.
Ao conectar uma solução Cisco Unified Communications Manager local com o Webex Calling, você pode usar a configuração simples do gateway PSTN como base para criar a solução ilustrada no diagrama a seguir. Nesse caso, um Gerenciador de Comunicações Unificadas fornece roteamento e tratamento centralizados de todas as chamadas PSTN e Webex Calling.
Ao longo deste documento, serão utilizados os nomes de host, endereços IP e interfaces ilustrados na imagem a seguir. São fornecidas opções para endereçamento público ou privado (atrás de um NAT). Os registros DNS SRV são opcionais, a menos que se trate de balanceamento de carga entre várias instâncias do CUBE.
Utilize as orientações de configuração presentes no restante deste documento para concluir a configuração do seu Gateway Local da seguinte forma:
Configuração básica
O primeiro passo para preparar seu roteador Cisco como um Gateway Local para o Webex Calling é criar uma configuração básica que proteja sua plataforma e estabeleça a conectividade.
-
Todas as implementações de Local Gateway baseadas em certificado exigem o Cisco IOS XE 17.9.1a ou versões posteriores. Recomenda-se o uso do Cisco IOS XE 17.12.2 ou posterior. Para as versões recomendadas, consulte a página Cisco Software Research. Procure a plataforma e selecione uma das versões sugeridas.
-
Os roteadores da série ISR4000 devem ser configurados com licenças de tecnologia de Comunicações Unificadas e de Segurança.
-
Os roteadores da série Catalyst Edge 8000 equipados com placas de voz ou DSPs requerem licenciamento DNA Advantage. Roteadores sem placas de voz ou DSPs exigem, no mínimo, uma licença DNA Essentials.
-
Para requisitos de alta capacidade, você também pode precisar de uma licença de Alta Segurança (HSEC) e de uma autorização adicional de taxa de transferência.
Consulte Códigos de autorização para obter mais detalhes.
-
-
Crie uma configuração básica para sua plataforma que esteja de acordo com as políticas da sua empresa. Em particular, configure e verifique o seguinte:
-
Ntp
-
Acls
-
Autenticação de usuário e acesso remoto
-
DNS
-
Roteamento IP
-
Endereços IP
-
-
A rede para o Webex Calling deve usar um endereço IPv4. Os endereços de nome de domínio totalmente qualificado (FQDN) ou registro de serviço (SRV) do gateway local configurados no Hub de Controle devem ser resolvidos para um endereço IPv4 público na internet.
-
Todas as portas SIP e de mídia na interface do Gateway Local voltada para o Webex devem ser acessíveis pela internet, seja diretamente ou via NAT estático. Certifique-se de atualizar seu firewall adequadamente.
-
Siga os passos de configuração detalhados fornecidos abaixo para instalar um certificado assinado no Gateway Local:
-
Uma Autoridade de Certificação (CA) pública, conforme detalhado em Quais Autoridades de Certificação Raiz são suportadas para chamadas para plataformas de áudio e vídeo Cisco Webex? deve assinar o certificado do dispositivo.
-
São suportados certificados que contenham apenas o uso estendido de chave de autenticação de servidor (EKU). O Webex Calling não valida nem impõe a presença do EKU de autenticação do cliente durante o estabelecimento do handshake TLS.
Alguns controladores de borda de sessão (SBC) de terceiros podem impor uma validação EKU rigorosa e podem rejeitar certificados que não incluam a EKU de autenticação do cliente. Nesses casos, certifique-se de que o SBC esteja configurado para aceitar apenas certificados com EKU de Autenticação de Servidor ou para desativar a validação rigorosa de EKU (se compatível).
-
O nome comum (CN) do sujeito do certificado, ou um dos nomes alternativos do sujeito (SAN), deve ser o mesmo que o FQDN configurado no Hub de Controle.
Ao adquirir um certificado com Nome Comum (CN) ou Nome Alternativo da Matéria (SAN), certifique-se de que o certificado utilize apenas letras minúsculas. Na configuração do Control Hub, todas as entradas de FQDN são convertidas automaticamente para letras minúsculas, e qualquer discrepância entre as letras maiúsculas e minúsculas do FQDN e do certificado impedirá o registro bem-sucedido do tronco.
Por exemplo:
-
Se um tronco configurado no Hub de Controle da sua organização tiver cube1.lgw.com:5061 Se o nome de domínio totalmente qualificado (FQDN) do gateway local for verdadeiro, o CN ou SAN no certificado do roteador deve conter cube1.lgw.com.
-
Se um tronco configurado no Hub de Controle da sua organização tiver lgws.lgw.com como o endereço SRV do(s) Gateway(s) Local(is) acessível(is) a partir do tronco, então o CN ou SAN no certificado do roteador deve conter lgws.lgw.com. Os registros que o SRV de usuário resolve para (CNAME, Um Registro ou Endereço IP) são opcionais em SAN.
-
Quer você use um FQDN ou um SRV para o tronco, o endereço de contato para todos os novos diálogos SIP do seu Gateway Local deve usar o nome configurado no Hub de Controle.
-
-
-
Faça o upload do pacote de certificados raiz da Cisco para o gateway local. Este pacote inclui o certificado raiz da Autoridade Certificadora (CA) usado para verificar a plataforma Webex.
Configuração
| 1 |
Certifique-se de atribuir endereços IP válidos e roteáveis a todas as interfaces de Camada 3, por exemplo:
|
| 2 |
Proteja as credenciais STUN no roteador usando criptografia simétrica. Configure a chave de criptografia primária e o tipo de criptografia da seguinte forma: |
| 3 |
Crie um ponto de confiança de criptografia com um certificado para o seu domínio, assinado por uma Autoridade de Certificação (AC)suportada. |
| 4 |
Forneça o certificado da CA intermediária para autenticar o certificado do seu host. Digite o seguinte comando de execução ou configuração:
|
| 5 |
Importe o certificado de host assinado usando o seguinte comando exec ou de configuração:
|
| 6 |
Habilite a exclusividade TLS 1.2 e especifique o ponto de confiança padrão a ser usado para aplicativos de voz usando os seguintes comandos de configuração:
|
| 7 |
Instale o pacote de certificados raiz da Cisco, que inclui o certificado IdenTrust Commercial Root CA 1 usado pelo Webex Calling. Use o comando crypto pki trustpool import clean url url para baixar o pacote de certificados raiz da CA a partir da URL especificada e para limpar o pool de certificados da CA atual. Em seguida, instale o novo pacote de certificados: Se você precisar usar um proxy para acessar a internet via HTTPS, adicione a seguinte configuração antes de importar o pacote de CA: ip http client proxy-server yourproxy.com proxy-port 80 |
| 1 |
Crie um tronco PSTN baseado em certificado CUBE para um local existente no Hub de Controle. Para obter mais informações, consulte Configurar troncos, grupos de rotas e planos de discagem para Webex Calling. Anote as informações do tronco ao criá-lo. Esses detalhes, destacados na ilustração a seguir, são usados nas etapas de configuração deste guia.
|
| 2 |
Insira os seguintes comandos para configurar o CUBE como um Gateway Local de Chamadas Webex: Aqui está uma explicação dos campos para a configuração:
Habilita os recursos do Cisco Unified Border Element (CUBE) na plataforma. permitir conexões sip para sipAtive a funcionalidade básica de agente de usuário SIP back-to-back do CUBE. Para obter mais informações, consulte Permitir conexões. Por padrão, o transporte de fax T.38 está ativado. Para obter mais informações, consulte protocolo de fax t38 (serviço de voz). Habilita o STUN (Session Traversal of UDP through NAT) globalmente. Esses comandos stun globais são necessários apenas ao implantar seu Gateway Local atrás de um NAT.
Para obter mais informações, consulte stun flowdata agent-ide stun flowdata shared-secret. carga útil assimétrica completaConfigura o suporte a payloads assimétricos SIP para payloads DTMF e de codecs dinâmicos. Para obter mais informações sobre este comando, consulte carga útil assimétrica. oferta antecipada forçadaForça o Gateway Local a enviar informações SDP na mensagem INVITE inicial, em vez de esperar pelo reconhecimento do par vizinho. Para obter mais informações sobre este comando, consulte oferta-antecipada. perfis sip de entradaPermite que o CUBE utilize perfis SIP para modificar as mensagens à medida que são recebidas. Os perfis são aplicados por meio de dial-peers ou tenants. |
| 3 |
Configure voice class codec 100 permitindo somente codecs G.711 para todos os troncos. Essa abordagem simples é adequada para a maioria das implementações. Se necessário, adicione à lista os tipos de codecs adicionais suportados pelos sistemas de origem e destino. Soluções mais complexas envolvendo transcodificação usando módulos DSP são suportadas, mas não estão incluídas neste guia. Aqui está uma explicação dos campos para a configuração: codec de classe de voz 100Utilizado para permitir apenas codecs preferenciais para chamadas de tronco SIP. Para obter mais informações, consulte codec de classe de voz. |
| 4 |
Configure voice class stun-usage 100 para habilitar o ICE no tronco Webex Calling. (Esta etapa não se aplica ao Webex para Governo) Aqui está uma explicação dos campos para a configuração: uso de atordoamento gelo leveUtilizado para habilitar o ICE-Lite para todos os dial-peers do Webex Calling, permitindo a otimização de mídia sempre que possível. Para mais informações, consulte uso de atordoamento da classe de voz e uso de atordoamento gelo leve. O comandostun usage firewall-traversal flowdatasó é necessário ao implantar seu Gateway Local atrás de um NAT. A otimização de mídia é negociada sempre que possível. Se uma chamada exigir serviços de mídia na nuvem, como gravação, a mídia não poderá ser otimizada. |
| 5 |
Configure a política de criptografia de mídia para o tráfego do Webex. (Esta etapa não se aplica ao Webex para Governo) Aqui está uma explicação dos campos para a configuração: classe de voz srtp-crypto 100Especifica SHA1_80 como o único conjunto de cifras SRTP que o CUBE oferece no SDP em mensagens de oferta e resposta. O Webex Calling suporta apenas SHA1_80. Para obter mais informações, consulte classe de voz srtp-crypto. |
| 6 |
Configurar cifras GCM compatíveis com FIPS (Esta etapa se aplica somente ao Webex para Governo). Aqui está uma explicação dos campos para a configuração: classe de voz srtp-crypto 100Especifica o GCM como o conjunto de cifras oferecido pelo CUBE. É obrigatório configurar as cifras GCM para o Gateway Local do Webex para Governo. |
| 7 |
Configure um padrão para identificar exclusivamente as chamadas para um tronco de Gateway Local com base em seu FQDN ou SRV de destino: Aqui está uma explicação dos campos para a configuração: aula de voz uri 100 golesDefine um padrão para associar um convite SIP recebido a um dial-peer de tronco também recebido. Ao inserir esse padrão, use o FQDN ou SRV do tronco configurado no Hub de Controle para o tronco. Durante a configuração, no lado do locatário, de troncos baseados em certificado para o Webex Calling, utilize apenas o endereço Webex Calling Edge baseado em SRV no Gateway Local. Os FQDNs não são mais suportados. |
| 8 |
Configure perfis de manipulação de mensagens SIP. Se o seu gateway estiver configurado com um endereço IP público, configure um perfil da seguinte forma ou pule para a próxima etapa se estiver usando NAT. Neste exemplo, cube1.lgw.com é o FQDN configurado para o Gateway Local: Aqui está uma explicação dos campos para a configuração: regras 10 e 20Para permitir que o Webex autentique mensagens do seu gateway local, o cabeçalho 'Contact' em uma solicitação SIP e em mensagens de resposta deve conter o valor provisionado para o tronco no Hub de Controle. Este será o FQDN de um único host ou o nome SRV usado para um cluster de dispositivos. |
| 9 |
Se o seu gateway estiver configurado com um endereço IP privado por trás de um NAT estático, configure os perfis SIP de entrada e saída da seguinte forma. Neste exemplo, cube1.lgw.com é o FQDN configurado para o Gateway Local, "10.80.13.12" é o endereço IP da interface voltada para o Webex Calling e "192.65.79.20" é o endereço IP público do NAT. Perfis SIP para mensagens de saída para o Webex Calling
Aqui está uma explicação dos campos para a configuração: regras 10 e 20Para permitir que o Webex autentique mensagens do seu gateway local, o cabeçalho 'Contact' nas mensagens de solicitação e resposta SIP deve conter o valor provisionado para o tronco no Hub de Controle. Este será o FQDN de um único host ou o nome SRV usado para um cluster de dispositivos. regras 30 a 81Converter referências de endereço privado para o endereço público externo do site, permitindo que o Webex interprete e encaminhe corretamente as mensagens subsequentes. Perfil SIP para mensagens recebidas do Webex CallingAqui está uma explicação dos campos para a configuração: regras 10 a 80Converter referências de endereço público para o endereço privado configurado, permitindo que o CUBE processe as mensagens do Webex. Para obter mais informações, consulte voice class sip-profiles. O provedor PSTN dos Estados Unidos ou do Canadá pode oferecer a verificação do ID do chamador para chamadas de spam e fraude, com a configuração adicional mencionada no artigo Indicação de chamada de spam ou fraude no Webex Calling. |
| 10 |
Configure um perfil de keepalive com opções SIP e modificação de cabeçalho.
|
| 11 |
Configurar tronco de chamadas Webex: |
| 12 |
(Opcional) Para configurar dispositivos de rede como o CUBE e encaminhar cabeçalhos do Protocolo de Iniciação de Sessão (SIP) que o dispositivo não processa, use estes comandos. Esses comandos permitem que o dispositivo transmita cabeçalhos SIP não suportados, incluindo cabeçalhos de geolocalização e PIDF-LO (Presence Information Data Format - Location Object), no gateway local. Essa funcionalidade auxilia os serviços Nomadic E-911, garantindo que as informações críticas de localização sejam preservadas e encaminhadas corretamente. |
Após criar um tronco para o Webex Calling conforme descrito acima, utilize a seguinte configuração para criar um tronco não criptografado para um provedor PSTN baseado em SIP:
Se o seu provedor de serviços oferecer um tronco PSTN seguro, você poderá seguir uma configuração semelhante à detalhada acima para o tronco de chamadas do Webex. O CUBE oferece suporte ao roteamento seguro de chamadas.
Se você estiver usando um TDM / Tronco PSTN ISDN, pule para a próxima seção Configurar Gateway Local com tronco PSTN TDM.
Para configurar interfaces TDM para pernas de chamadas PSTN nos gateways Cisco TDM-SIP, consulte Configurando ISDN PRI.
| 1 |
Configure o seguinte URI de classe de voz para identificar chamadas recebidas do tronco PSTN: Aqui está uma explicação dos campos para a configuração: aula de voz uri 200 golesDefine um padrão para associar um convite SIP recebido a um dial-peer de tronco também recebido. Ao inserir esse padrão, use o endereço IP do seu gateway PSTN. Para obter mais informações, consulte voice class uri. |
| 2 |
Configure o seguinte dial-peer IP PSTN: Aqui está uma explicação dos campos para a configuração: Define um dial-peer VoIP com uma tag de 200 e fornece uma descrição significativa para facilitar o gerenciamento e a resolução de problemas. Para obter mais informações, consulte dial-peer voice. padrão de destino RUIM.RUIMÉ necessário um padrão de destino fictício ao rotear chamadas de saída usando um grupo de dial-peers de entrada. Neste caso, qualquer padrão de destino válido pode ser usado. Para obter mais informações, consulte destination-pattern (interface). sessão protocolo sipv2Especifica que este dial-peer lida com as pernas de chamada SIP. Para obter mais informações, consulte protocolo de sessão (dial peer). destino da sessão ipv4: 192.168.80.13Especifica o endereço de destino para chamadas enviadas ao provedor PSTN. Isso pode ser um endereço IP ou um nome de host DNS. Para obter mais informações, consulte destino da sessão (VoIP dial peer). uri de entrada via 200Especifica a classe de voz usada para corresponder as chamadas recebidas a este dial-peer usando o URI do cabeçalho INVITE VIA. Para obter mais informações, consulte URL de entrada. classe de voz gole id afirmado pai
(Opcional) Ativa o processamento do cabeçalho P-Asserted-Identity e controla como ele é usado para o tronco PSTN. Se este comando for utilizado, a identidade da parte que está chamando, fornecida pelo dial-peer de entrada, será usada nos cabeçalhos From e P-Asserted-Identity de saída. Caso este comando não seja utilizado, a identidade da parte chamadora fornecida pelo dial-peer de entrada será utilizada nos cabeçalhos From e Remote-Party-ID de saída. Para obter mais informações, consulte voice-class sip asserted-id. vincular interface de origem de controle GigabitEthernet0/0/0
Configura a interface de origem e o endereço IP associado para mensagens enviadas à PSTN. Para obter mais informações, consulte bind. vincular interface de origem de mídia GigabitEthernet0/0/0Configura a interface de origem e o endereço IP associado para mídia enviada à PSTN. Para obter mais informações, consulte bind. codec de classe de voz 100Configura o dial-peer para usar a lista de filtros de codec comum 100. Para obter mais informações, consulte codec de classe de voz. dtmf-relay rtp-nteDefine o RTP-NTE (RFC2833) como o recurso DTMF esperado no retorno de chamada. Para obter mais informações, consulte DTMF Relay (Voz sobre IP). sem vadDesativa a detecção de atividade de voz. Para obter mais informações, consulte vad (dial peer). |
| 3 |
Se você estiver configurando seu Gateway Local para rotear chamadas somente entre o Webex Calling e a PSTN, adicione a seguinte configuração de roteamento de chamadas. Se você estiver configurando seu Gateway Local com uma plataforma Unified Communications Manager, pule para a próxima seção. |
Após criar um tronco para o Webex Calling, utilize a seguinte configuração para criar um tronco TDM para o seu serviço PSTN com roteamento de chamadas em loopback, permitindo a otimização de mídia na chamada do Webex.
Se você não precisa de otimização de mídia IP, siga os passos de configuração para um tronco SIP PSTN. Utilize uma porta de voz e um dial-peer POTS (conforme mostrado nas etapas 2 e 3) em vez do dial-peer VoIP PSTN.
| 1 |
A configuração de dial-peer de loopback usa grupos de dial-peers e tags de roteamento de chamadas para garantir que as chamadas sejam transmitidas corretamente entre o Webex e a PSTN, sem criar loops de roteamento de chamadas. Configure as seguintes regras de tradução que serão usadas para adicionar e remover as tags de roteamento de chamadas: Aqui está uma explicação dos campos para a configuração: regra de tradução de vozUtiliza expressões regulares definidas em regras para adicionar ou remover tags de roteamento de chamadas. Os dígitos acima da decimal ('A') são usados para maior clareza na resolução de problemas. Nessa configuração, a tag adicionada pelo translation-profile 100 é usada para direcionar as chamadas do Webex Calling para a PSTN por meio dos dial-peers de loopback. Da mesma forma, a tag adicionada pelo perfil de tradução 200 é usada para direcionar chamadas da PSTN para o Webex Calling. Os perfis de tradução 11 e 12 removem essas tags antes de encaminhar as chamadas para os troncos Webex e PSTN, respectivamente. Este exemplo pressupõe que os números chamados pelo Webex Calling sejam apresentados em +E.164 formatar. A regra 100 remove o primeiro + Para manter um número chamado válido. A regra 12 adiciona então um ou mais dígitos de roteamento nacional ou internacional ao remover a etiqueta. Use dígitos que correspondam ao seu plano de discagem nacional ISDN local. Se o Webex Calling apresentar números no formato nacional, ajuste as regras 100 e 12 para simplesmente adicionar e remover a tag de roteamento, respectivamente. Para obter mais informações, consulte voice translation-profile e voice translation-rule. |
| 2 |
Configure as portas da interface de voz TDM conforme exigido pelo tipo de tronco e protocolo utilizado. Para obter mais informações, consulte Configurando ISDN PRI. Por exemplo, a configuração básica de uma interface ISDN de taxa primária instalada no slot NIM 2 de um dispositivo pode incluir o seguinte: |
| 3 |
Configure o seguinte dial-peer TDM PSTN: Aqui está uma explicação dos campos para a configuração: Define um dial-peer VoIP com a tag 200 e fornece uma descrição significativa para facilitar o gerenciamento e a resolução de problemas. Para obter mais informações, consulte dial-peer voice. padrão de destino RUIM.RUIMÉ necessário um padrão de destino fictício ao rotear chamadas de saída usando um grupo de dial-peers de entrada. Qualquer padrão de destino válido pode ser usado neste caso. Para obter mais informações, consulte destination-pattern (interface). perfil de tradução recebido 200Atribui o perfil de tradução que adicionará uma etiqueta de encaminhamento de chamadas ao número chamado de entrada. discagem direta para dentroEncaminha a chamada sem fornecer um tom de discagem secundário. Para obter mais informações, consulte direct-inward-dial. porta 0/2/0:15A porta de voz física associada a este dial-peer. |
| 4 |
Para habilitar a otimização de mídia dos caminhos IP para gateways locais com fluxos de chamadas TDM-IP, você pode modificar o roteamento de chamadas introduzindo um conjunto de dial-peers de loopback internos entre o Webex Calling e os troncos PSTN. Configure os seguintes dial-peers de loopback. Neste caso, todas as chamadas recebidas serão inicialmente encaminhadas para o dial-peer 10 e, a partir daí, para o dial-peer 11 ou 12, com base na tag de roteamento aplicada. Após a remoção da etiqueta de roteamento, as chamadas serão encaminhadas para o tronco de saída usando grupos de dial-peer. Aqui está uma explicação dos campos para a configuração: Define um dial-peer VoIP e fornece uma descrição significativa para facilitar o gerenciamento e a resolução de problemas. Para obter mais informações, consulte dial-peer voice. perfil de tradução recebido 11Aplica o perfil de tradução definido anteriormente para remover a etiqueta de roteamento de chamadas antes de passar para o tronco de saída. padrão de destino RUIM.RUIMÉ necessário um padrão de destino fictício ao rotear chamadas de saída usando um grupo de dial-peers de entrada. Para obter mais informações, consulte destination-pattern (interface). sessão protocolo sipv2Especifica que este dial-peer lida com as pernas de chamada SIP. Para obter mais informações, consulte protocolo de sessão (dial peer). destino da sessão ipv4: 192.168.80.14Especifica o endereço da interface do roteador local como o destino da chamada para o loopback. Para obter mais informações, consulte destino da sessão (voip dial peer). vincular interface de origem de controle GigabitEthernet0/0/0Configura a interface de origem e o endereço IP associado para mensagens enviadas através do loopback. Para obter mais informações, consulte bind. vincular interface de origem de mídia GigabitEthernet0/0/0Configura a interface de origem e o endereço IP associado para mídias enviadas através do loopback. Para obter mais informações, consulte bind. dtmf-relay rtp-nteDefine o RTP-NTE (RFC2833) como o recurso DTMF esperado no retorno de chamada. Para obter mais informações, consulte DTMF Relay (Voz sobre IP). codec g711alaw Força todas as chamadas PSTN a utilizarem G.711. Selecione a-law ou u-law para corresponder ao método de compressão utilizado pelo seu serviço ISDN. sem vadDesativa a detecção de atividade de voz. Para obter mais informações, consulte vad (dial peer). |
| 5 |
Adicione a seguinte configuração de roteamento de chamadas: Isso conclui a configuração do seu Gateway Local. Salve a configuração e recarregue a plataforma se esta for a primeira vez que os recursos do CUBE são configurados.
|
A configuração de chamadas PSTN-Webex nas seções anteriores pode ser modificada para incluir troncos adicionais em um cluster Cisco Unified Communications Manager (UCM). Neste caso, todas as chamadas são encaminhadas através do Unified CM. As chamadas originadas no UCM pela porta 5060 são encaminhadas para a PSTN e as chamadas originadas pela porta 5065 são encaminhadas para o Webex Calling. As seguintes configurações incrementais podem ser adicionadas para incluir esse cenário de chamada.
| 1 |
Configure as seguintes URIs de classe de voz: |
| 2 |
Configure os seguintes registros DNS para especificar o roteamento SRV para hosts do Unified CM: O IOS XE utiliza esses registros para determinar localmente os hosts e portas UCM de destino. Com essa configuração, não é necessário configurar registros no seu sistema DNS. Se preferir usar seu próprio servidor DNS, essas configurações locais não são necessárias. Aqui está uma explicação dos campos para a configuração: O comando a seguir cria um registro de recurso DNS SRV. Crie um registro para cada host e tronco UCM: ip host _sip._udp.pstntocucm.io srv 2 1 5060 ucmsub5.mydomain.com _sip._udp.pstntocucm.io: Nome do registro de recurso SRV 2: A prioridade do registro de recursos SRV 1: O peso do registro de recursos SRV 5060: O número da porta a ser usada para o host de destino neste registro de recurso. ucmsub5.mydomain.com: O host de destino do registro de recursos Para resolver os nomes de host de destino dos registros de recursos, crie registros DNS A locais. Por exemplo: host ip ucmsub5.mydomain.com 192.168.80.65 host ip: Cria um registro no banco de dados local do IOS XE. ucmsub5.mydomain.com: O nome do host do registro A. 192.168.80.65: O endereço IP do host. Crie os registros de recursos SRV e os registros A para refletir seu ambiente UCM e a estratégia de distribuição de chamadas preferida. |
| 3 |
Configure os seguintes dial-peers: |
| 4 |
Adicione o roteamento de chamadas usando as seguintes configurações: |
As Assinaturas de Diagnóstico (DS) detectam proativamente problemas observados no Gateway local baseado no Cisco IOS XE e gera notificações por e-mail, syslog ou mensagem terminal do evento. Você também pode instalar o DS para automatizar a coleta de dados de diagnóstico e transferir os dados coletados para o caso do TAC da Cisco a fim de acelerar o tempo de resolução.
Assinaturas de Diagnóstico (DS) são arquivos XML que contêm informações sobre eventos de acionador de problemas e ações para informar, solucionar problemas e resolver o problema. Use mensagens syslog, eventos SNMP e através do monitoramento periódico de mostrar saídas de comando específicas para definir a lógica de detecção de problemas. Os tipos de ações incluem:
-
Coletando saídas de comando show
-
Gerando um arquivo de registro consolidado
-
Carregando o arquivo para um usuário fornecido localização de rede como HTTPS, SCP, servidor FTP
Os arquivos DS dos engenheiros do TAC são assinados digitalmente para uma proteção de integridade. Cada arquivo DS tem a ID numérica exclusiva atribuída pelo sistema. AFerramenta de Busca de Assinaturas de Diagnóstico (DSLT) é uma fonte única para encontrar assinaturas aplicáveis para monitoramento e solução de diversos problemas.
Antes de você começar:
-
Não edite o arquivo DS que você baixa do DSLT. Os arquivos que você modifica falham na instalação devido ao erro de verificação de integridade.
-
Um servidor de Protocolo de Transferência de E-mail Simples (SMTP) que você precisa para o Gateway Local enviar notificações por e-mail.
-
Certifique-se de que o Gateway Local está executando o IOS XE 17.6.1 ou superior se você desejar usar o servidor SMTP seguro para notificações por e-mail.
Pré-requisitos
Gateway local executando o IOS XE 17.6.1 ou superior
-
As Assinaturas de diagnóstico estão ativadas por padrão.
-
Configure o servidor de e-mail seguro que você usa para enviar uma notificação proativa se o dispositivo estiver executando o IOS XE 17.6.1 ou superior.
configure terminal call-home mail-server :@ priority 1 secure tls end -
Configure a variável de ambiente ds_email com o endereço de e-mail do administrador para você notificar.
configure terminal call-home diagnostic-signature LocalGateway(cfg-call-home-diag-sign)environment ds_email end
Instalar assinaturas de diagnóstico para monitoramento proativo
Monitoramento de alta utilização da CPU
Este DS rastreia a utilização da CPU de 5 segundos usando o OID SNMP 1.3.6.1.4.1.9.2.1.56. Quando a utilização atingir 75% ou mais, ela desativa todas as depurações e desinstala todas as assinaturas de diagnóstico que você instalar no Gateway local. Use as etapas abaixo para instalar a assinatura.
-
Certifique-se de que você habilitar o SNMP usando o comando mostrar snmp. Se o SNMP não estiver habilitado, configure o comando snmp-server manager.
show snmp %SNMP agent not enabled config t snmp-server manager end show snmp Chassis: ABCDEFGHIGK 149655 SNMP packets input 0 Bad SNMP version errors 1 Unknown community name 0 Illegal operation for community name supplied 0 Encoding errors 37763 Number of requested variables 2 Number of altered variables 34560 Get-request PDUs 138 Get-next PDUs 2 Set-request PDUs 0 Input queue packet drops (Maximum queue size 1000) 158277 SNMP packets output 0 Too big errors (Maximum packet size 1500) 20 No such name errors 0 Bad values errors 0 General errors 7998 Response PDUs 10280 Trap PDUs Packets currently in SNMP process input queue: 0 SNMP global trap: enabled Baixe o DS 64224 usando as seguintes opções suspensas na Ferramenta de pesquisa de assinaturas de diagnóstico:
copy ftp://username:password@/DS_64224.xml bootflash:Nome do campo
Valor do campo
Plataforma
Software Cisco Edge para Cisco 4300, 4400 ISR Series ou Catalyst 8000V
Produto
CUBE Enterprise na solução de chamadas Webex
Escopo do problema
Desempenho
Tipo de problema
Alta utilização da CPU com notificação por e-mail
-
Copie o arquivo DS XML para o flash do Gateway local.
copy ftp://username:password@/DS_64224.xml bootflash:O exemplo a seguir mostra a cópia do arquivo de um servidor FTP para o Gateway Local.
copy ftp://user:pwd@192.0.2.12/DS_64224.xml bootflash: Accessing ftp://*:*@ 192.0.2.12/DS_64224.xml...! [OK - 3571/4096 bytes] 3571 bytes copied in 0.064 secs (55797 bytes/sec) -
Instale o arquivo DS XML no Gateway local.
call-home diagnostic-signature load DS_64224.xml Load file DS_64224.xml success -
Use o comando mostrar assinatura de diagnóstico de chamada de casa para verificar se a assinatura foi instalada com êxito. A coluna status deve ter um valor "registrado".
show call-home diagnostic-signature Current diagnostic-signature settings: Diagnostic-signature: enabled Profile: CiscoTAC-1 (status: ACTIVE) Downloading URL(s): https://tools.cisco.com/its/service/oddce/services/DDCEService Environment variable: ds_email: username@gmail.comBaixe o DSes:
ID de DS
Nome DS
Revisão
Status
Última atualização (GMT+00:00)
64224
DS_LGW_CPU_MON75
0.0.10
Registrado
2020-11-07 22:05:33
Quando acionada, esta assinatura desinstala todos os DSs em execução, incluindo ela própria. Se necessário, reinstale o DS 64224 para continuar a monitorar a alta utilização da CPU no Gateway local.
Monitorando desconectações anormals de chamada
Esta assinatura digital utiliza sondagem SNMP a cada 10 minutos para detectar desconexões anormais de chamadas com erros SIP 403, 488 e 503. Se o incremento na contagem de erros for maior ou igual a 5 em relação à última sondagem, ela gera um registro no syslog e uma notificação por e-mail. Siga os passos abaixo para instalar a assinatura.
-
Certifique-se de que o SNMP está habilitado usando o comando mostrar snmp. Se o SNMP não estiver habilitado, configure o comando snmp-server manager.
show snmp %SNMP agent not enabled config t snmp-server manager end show snmp Chassis: ABCDEFGHIGK 149655 SNMP packets input 0 Bad SNMP version errors 1 Unknown community name 0 Illegal operation for community name supplied 0 Encoding errors 37763 Number of requested variables 2 Number of altered variables 34560 Get-request PDUs 138 Get-next PDUs 2 Set-request PDUs 0 Input queue packet drops (Maximum queue size 1000) 158277 SNMP packets output 0 Too big errors (Maximum packet size 1500) 20 No such name errors 0 Bad values errors 0 General errors 7998 Response PDUs 10280 Trap PDUs Packets currently in SNMP process input queue: 0 SNMP global trap: enabled -
Baixe o DS 65221 usando as seguintes opções na Ferramenta de pesquisa de assinaturas de diagnóstico:
Nome do campo
Valor do campo
Plataforma
Software Cisco Edge para Cisco 4300, 4400 ISR Series ou Catalyst 8000V
Produto
CUBE Enterprise na solução do Webex Calling
Escopo do problema
Desempenho
Tipo de problema
Detecção anormal de desconexão de chamada SIP com e-mail e notificação Syslog.
-
Copie o arquivo DS XML para o Gateway local.
copy ftp://username:password@/DS_65221.xml bootflash: -
Instale o arquivo DS XML no Gateway local.
call-home diagnostic-signature load DS_65221.xml Load file DS_65221.xml success -
Use o comando show call-home diagnostic-signature para verificar se a assinatura foi instalada com sucesso. A coluna de status deve ter um valor "registrado".
Instalar assinaturas de diagnóstico para solucionar um problema
Você também pode usar Assinaturas de Diagnóstico (DS) para resolver os problemas rapidamente. Os engenheiros do TAC da Cisco criaram várias assinaturas que permitem as depurações necessárias que são necessárias para solucionar um determinado problema, detectar a ocorrência do problema, coletar o conjunto certo de dados de diagnóstico e transferir os dados automaticamente para o caso do CISCO TAC. Isso elimina a necessidade de verificar manualmente a ocorrência do problema e torna a solução de problemas intermitentes e temporários muito mais fácil.
Você pode usar a Ferramenta de pesquisa de assinaturas de diagnóstico para encontrar as assinaturas aplicáveis e instalá-las para se auto-resolver um determinado problema ou você pode instalar a assinatura que é recomendada pelo engenheiro de TAC como parte do envolvimento do suporte.
Aqui está um exemplo de como encontrar e instalar um DS para detectar a ocorrência "%VOICE_IEC-3-GW: CCAPI: Erro interno (limite de pico de chamadas): IEC=1.1.181.1.29.0" syslog e automatize a coleta de dados de diagnóstico usando as seguintes etapas:
Configure outra variável de ambiente DS ds_fsurl_prefixcomo o caminho do servidor de arquivos do Cisco TAC (cxd.cisco.com) para carregar os dados de diagnóstico. O nome de usuário no caminho do arquivo é o número do caso e a senha é o token de upload do arquivo, que pode ser obtido em Support Case Manager conforme mostrado a seguir. O token de upload do arquivo pode ser gerado na seção Attachments do Support Case Manager, se necessário.
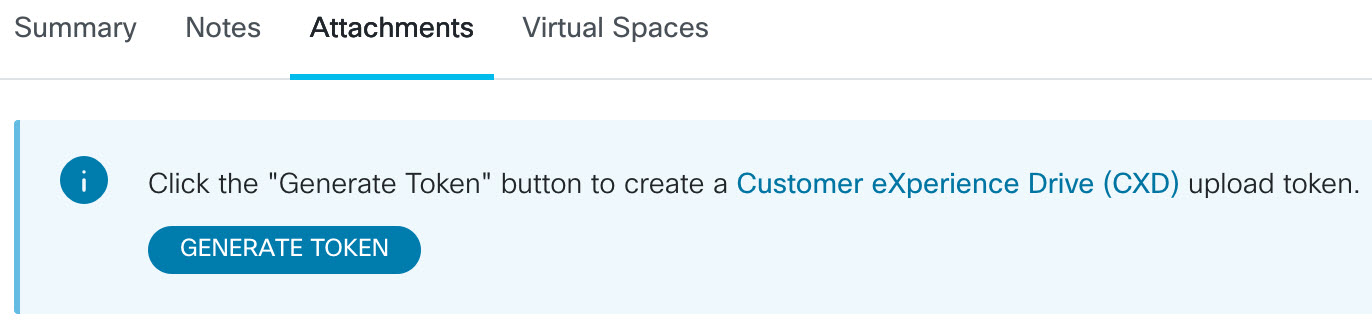
configure terminal call-home diagnostic-signature LocalGateway(cfg-call-home-diag-sign)environment ds_fsurl_prefix "scp://:@cxd.cisco.com" endExemplo:
call-home diagnostic-signature environment ds_fsurl_prefix " environment ds_fsurl_prefix "scp://612345678:abcdefghijklmnop@cxd.cisco.com"-
Certifique-se de que o SNMP está habilitado usando o comando mostrar snmp. Se o SNMP não estiver habilitado, configure o comando snmp-server manager.
show snmp %SNMP agent not enabled config t snmp-server manager end -
Recomendamos instalar o monitoramento de alta CPU DS 64224 como uma medida proativa para desativar todas as assinaturas de depuração e diagnósticos durante o momento de alta utilização da CPU. Baixe o DS 64224 usando as seguintes opções na Ferramenta de pesquisa de assinaturas de diagnóstico:
Nome do campo
Valor do campo
Plataforma
Software Cisco Edge para Cisco 4300, 4400 ISR Series ou Catalyst 8000V
Produto
CUBE Enterprise na solução do Webex Calling
Escopo do problema
Desempenho
Tipo de problema
Alta utilização da CPU com notificação por e-mail.
-
Baixe o DS 65095 usando as seguintes opções na Ferramenta de pesquisa de assinaturas de diagnóstico:
Nome do campo
Valor do campo
Plataforma
Software Cisco Edge para Cisco 4300, 4400 ISR Series ou Catalyst 8000V
Produto
CUBE Enterprise na solução do Webex Calling
Escopo do problema
Syslogs
Tipo de problema
Syslog - %VOICE_IEC-3-GW: CCAPI: Erro interno (limite de pico de chamadas): IEC=1.1.181.1.29.0
-
Copie os arquivos DS XML para o Gateway local.
copy ftp://username:password@/DS_64224.xml bootflash: copy ftp://username:password@/DS_65095.xml bootflash: -
Instale o arquivo XML DS 64224, que monitora alto uso da CPU, e em seguida o arquivo XML DS 65095 no Gateway Local.
call-home diagnostic-signature load DS_64224.xml Load file DS_64224.xml success call-home diagnostic-signature load DS_65095.xml Load file DS_65095.xml success -
Verifique se a assinatura foi instalada com êxito usando show call-home diagnostic-signature. A coluna de status deve ter um valor "registrado".
show call-home diagnostic-signature Current diagnostic-signature settings: Diagnostic-signature: enabled Profile: CiscoTAC-1 (status: ACTIVE) Downloading URL(s): https://tools.cisco.com/its/service/oddce/services/DDCEService Environment variable: ds_email: username@gmail.com ds_fsurl_prefix: scp://612345678:abcdefghijklmnop@cxd.cisco.comDSes baixados:
ID de DS
Nome DS
Revisão
Status
Última atualização (GMT+00:00)
64224
00:07:45
DS_LGW_CPU_MON75
0.0.10
Registrado
2020-11-08:00:07:45
65095
00:12:53
DS_LGW_IEC_Call_spike_threshold
0.0.12
Registrado
2020-11-08:00:12:53
Verificar a execução de assinaturas de diagnóstico
No seguinte comando, a coluna "Status" do comando mostra as alterações de assinatura de diagnóstico de chamada de casa para "em execução" enquanto o Gateway local executa a ação definida dentro da assinatura. O resultado de mostrar as estatísticas de diagnóstico de chamada de casa é a melhor maneira de verificar se uma assinatura de diagnóstico detecta um evento de interesse e executa a ação. A coluna "Acionado/Máximo/Desinstalação" indica o número de vezes que a assinatura dada acionou um evento, o número máximo de vezes que é definido para detectar um evento e se a assinatura desinstala-se depois de detectar o número máximo de eventos acionados.
show call-home diagnostic-signature
Current diagnostic-signature settings:
Diagnostic-signature: enabled
Profile: CiscoTAC-1 (status: ACTIVE)
Downloading URL(s): https://tools.cisco.com/its/service/oddce/services/DDCEService
Environment variable:
ds_email: carunach@cisco.com
ds_fsurl_prefix: scp://612345678:abcdefghijklmnop@cxd.cisco.com DSes baixados:
|
ID de DS |
Nome DS |
Revisão |
Status |
Última atualização (GMT+00:00) |
|---|---|---|---|---|
|
64224 |
DS_LGW_CPU_MON75 |
0.0.10 |
Registrado |
2020-11-08 00:07:45 |
|
65095 |
DS_LGW_IEC_Call_spike_threshold |
0.0.12 |
Em execução |
2020-11-08 00:12:53 |
mostrar estatísticas de assinatura do diagnóstico de chamada de casa
|
ID de DS |
Nome DS |
Provocado/Max/Deinstall |
Tempo médio de execução (segundos) |
Tempo máximo de execução (segundos) |
|---|---|---|---|---|
| 64224 |
DS_LGW_CPU_MON75 |
0/0/N |
0.000 |
0.000 |
|
65095 |
DS_LGW_IEC_Call_spike_threshold |
1/20/Y |
23.053 |
23.053 |
O e-mail de notificação que é enviado durante a execução da Assinatura de Diagnóstico contém informações importantes como tipo de problema, detalhes do dispositivo, versão do software, configuração em execução e mostra saídas de comando que são relevantes para solucionar o problema dado.
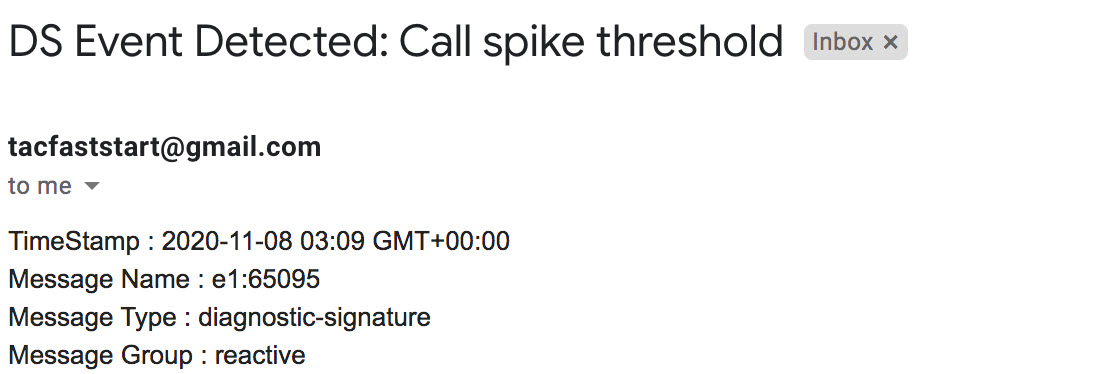
Desinstalar assinaturas de diagnóstico
Use as assinaturas de diagnóstico para fins de solução de problemas que são tipicamente definidas para desinstalar após a detecção de algumas ocorrências de problemas. Se você desejar desinstalar uma assinatura manualmente, recupere a ID DS da saída da assinatura de diagnóstico de chamada de entrada de chamada de entrada e execute o seguinte comando:
call-home diagnostic-signature deinstall Exemplo:
call-home diagnostic-signature deinstall 64224
Novas assinaturas são adicionadas periodicamente à Ferramenta de Pesquisa de Assinaturas de Diagnósticos, com base nos problemas que são observados nas implantações. Atualmente, o TAC não oferece suporte a solicitações de criação de novas assinaturas personalizadas.