Webex Suite Meetings: KMS-encrypted meeting content and data residency
 Feedback?
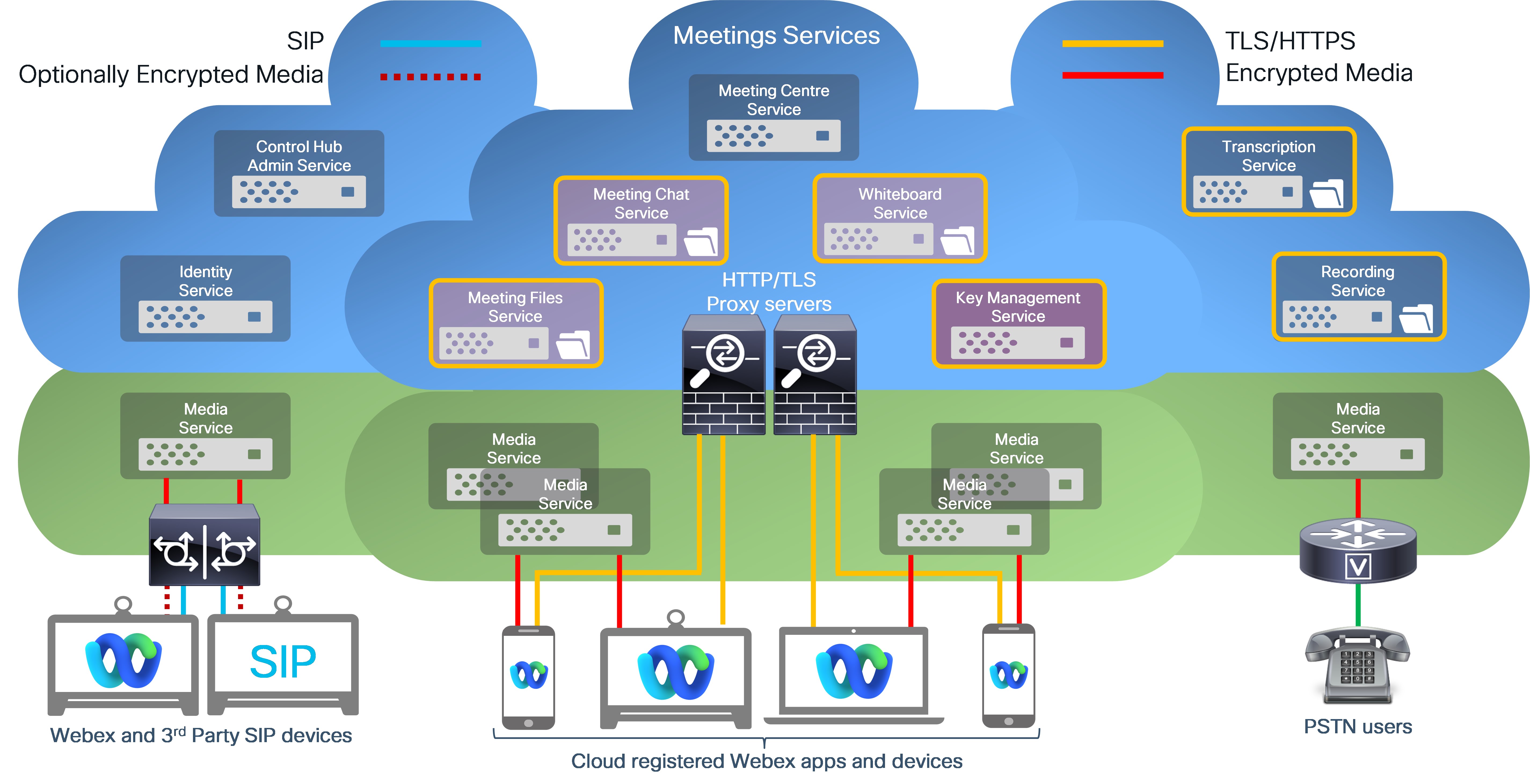
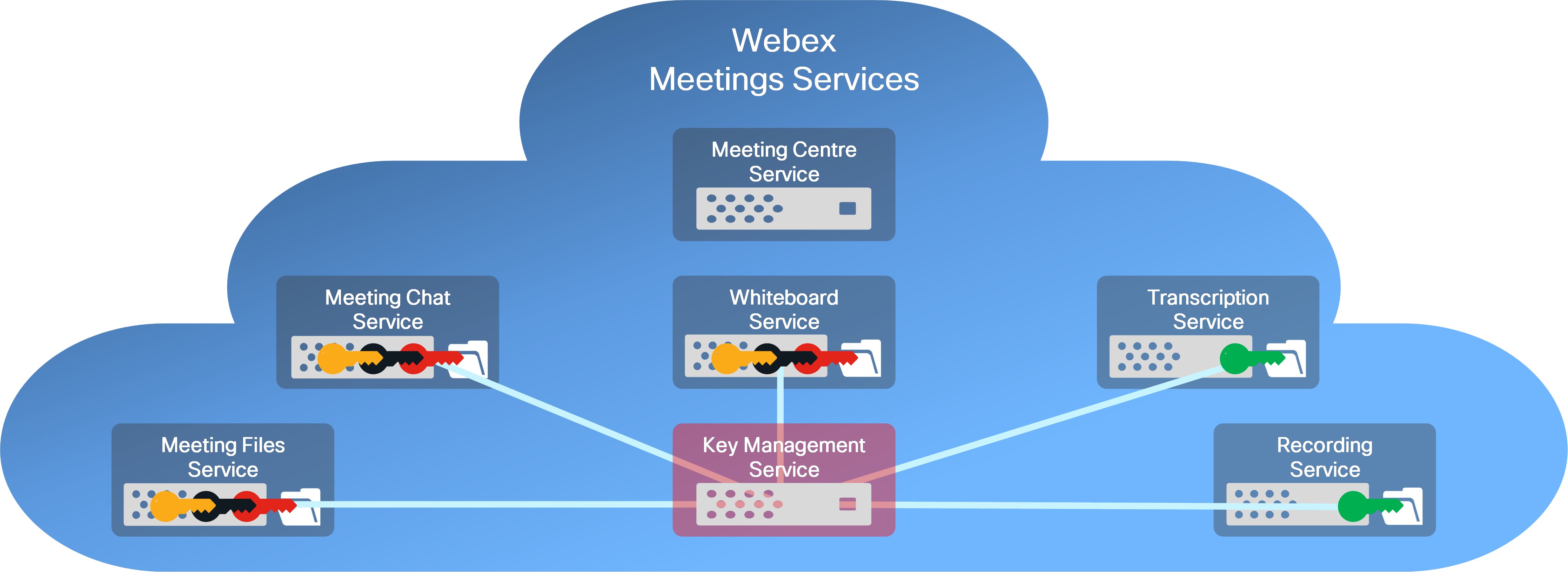
Feedback?The Webex Key Management Service (KMS) was originally developed to add an extra layer of encryption for Webex Messaging content, such as exchanged messages and files. Now Webex Suite allows Meetings to use KMS as a common encryption service for user-generated content. Webex Suite services now use KMS to encrypt the following data types:
Webex Messaging
- Messages
- Files
Webex Meetings
- Chat messages (new)
- Shared files (new)
- Annotations (new)
- Recordings
- Transcripts
- Whiteboards
- Voicemails
- Voicemail transcripts
Webex end-to-end encryption uses KMS to generate, distribute and manage the encryption keys used to encrypt the user-generated content listed above.
- Webex App and Cisco video devices use Webex end-to-end encryption for all user-generated content, such as messages, files, and whiteboards, and also encrypt this data using transport layer security (TLS) for data in transit.
- For data at rest, this end-to-end encrypted content is stored on encrypted content servers in the Webex cloud.
- This additional layer of security protects user-generated content in transit from TLS interception attacks, and stored user data from potential bad actors in the Webex cloud.
With Webex end-to-end encryption, Webex services can use end-to-end encryption keys to decrypt data to deliver Webex core services, such as:
- Message indexing for search functions
- Data loss prevention (compliance)
- File transcoding
- eDiscovery
- Data archival
- Malware scanning (with Extended Security Pack)
If you need higher levels of security and confidentiality for your meetings, you can use Zero Trust End-to-End Encrypted Webex Meetings. With Zero Trust Security, the meeting encryption key is generated by, and only accessible to, the participants in the meeting; the Webex service cannot access the meeting encryption keys.
See End-to-end encryption with identity verification for Webex meetings to compare Webex End-to-End Encryption and Zero-Trust End-to-End Encryption.
Webex Meetings recordings and transcripts are encrypted using a KMS-generated encryption key (encryption cipher = AES-256-GCM). A single encryption key is used to encrypt all recordings and transcripts for your organization.
Webex provides the following controls for meeting recordings and transcripts:
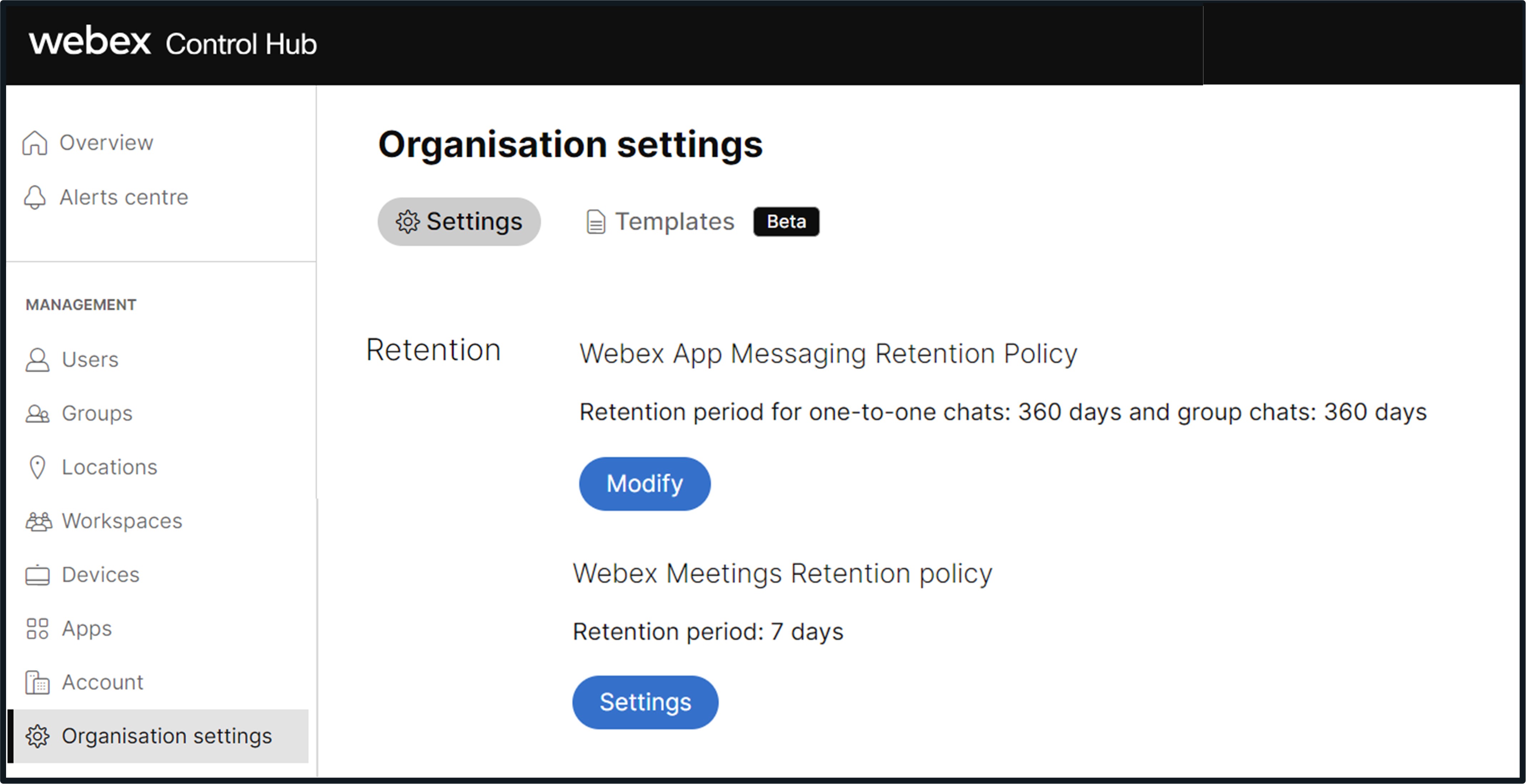
- Retention policy for recordings and transcripts (7–3600 days)
- Purge user-deleted recordings within 30 days
- Secure playback and download: Only allowed from defined networks
- Recording passwords and password policies
- Recording storage management
With KMS-based content encryption, unique content encryption keys are generated for each Webex meeting. These encryption keys are used to encrypt the chat messages, captions, shared files, whiteboards, and annotations shared in your meeting. Recordings and transcripts stored in the Webex cloud by your organization are secured using a single KMS-generated AES-256-GCM encryption key.
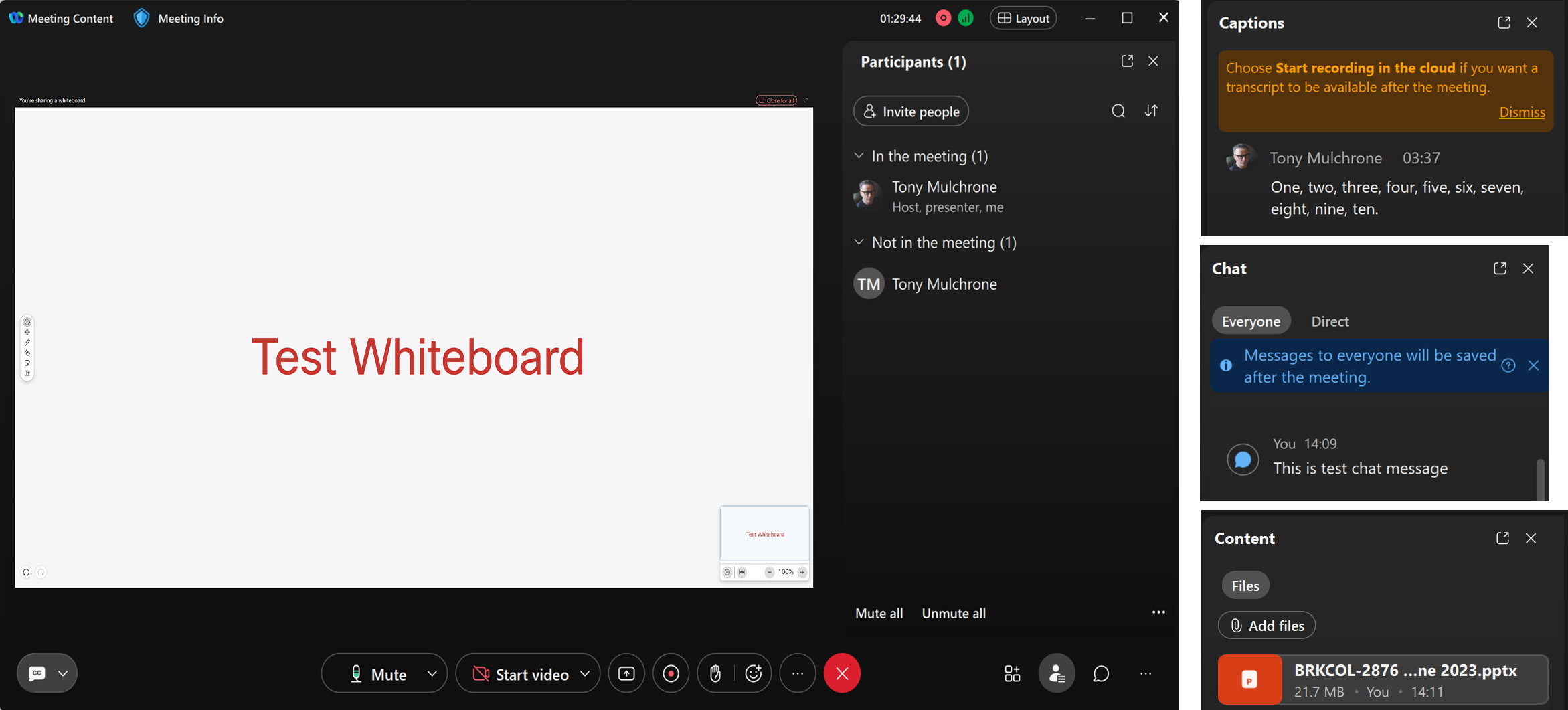
Content that is shared/created during a Webex Meeting (chat, recordings, transcripts, and whiteboards) can be viewed after the meeting ends.
You can view chat, recordings, and transcripts in Webex App's Calendar and Meeting Content tabs. All meeting participants with a Webex account can access chat messages and recordings in Webex App. Unverified meeting participants, who did not sign in, only have access to shared content during the meeting.
Whiteboards created by participants in a meeting are automatically stored in the meeting participant’s Webex whiteboard space.
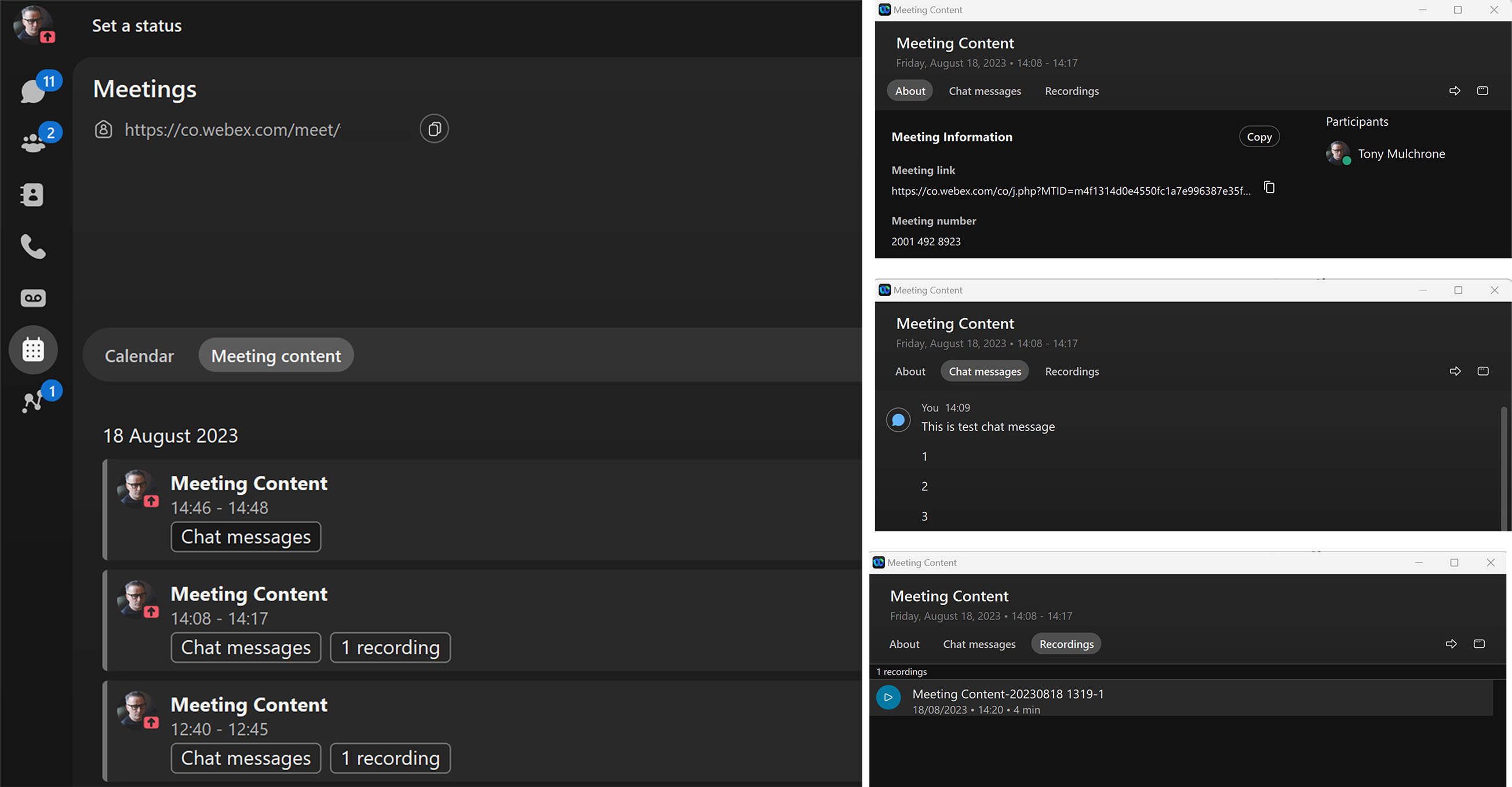
Chat messages, recordings, and recording transcripts
Chat messages, recordings, and recording transcripts use the Control Hub Webex Meetings Retention policy setting.
Whiteboards
Whiteboards created in Webex Meetings use the Webex Messaging Retention Policy. The Whiteboard retention policy is that of the organization to which the creator of the whiteboard belongs.
Recordings and recording transcripts are stored in the Webex Meetings region selected by your organization when you signed up for Webex. For details of Webex Meetings regions and data center locations, see the Webex Meetings Privacy datasheet.
Chat messages and whiteboards created in your meetings are stored in Webex Messaging data center regions. Currently, Webex Messaging uses two data center regions to store chat messages and whiteboard content—North America & Rest of the World and European Union. During provisioning, the administrator who sets up an organization sees a Country Selector drop-down menu in Control Hub. We determine the geographic region in which the organization's messaging data resides. For more information on this process and the region a particular country maps to, see Find the data residency region that maps to a country.

For more information on Webex Messaging data residency, see the Webex App & Webex Messaging Privacy Data Sheet and Data Residency in Webex.
If required, the persistent storage of Webex Meetings chat messages can be disabled for your organization in Control Hub. See Save or clear your organization's in-meeting chats after a meeting. Control Hub administrators can disable whiteboard usage in your organization on a per user/user group basis for internal and/or external meetings.
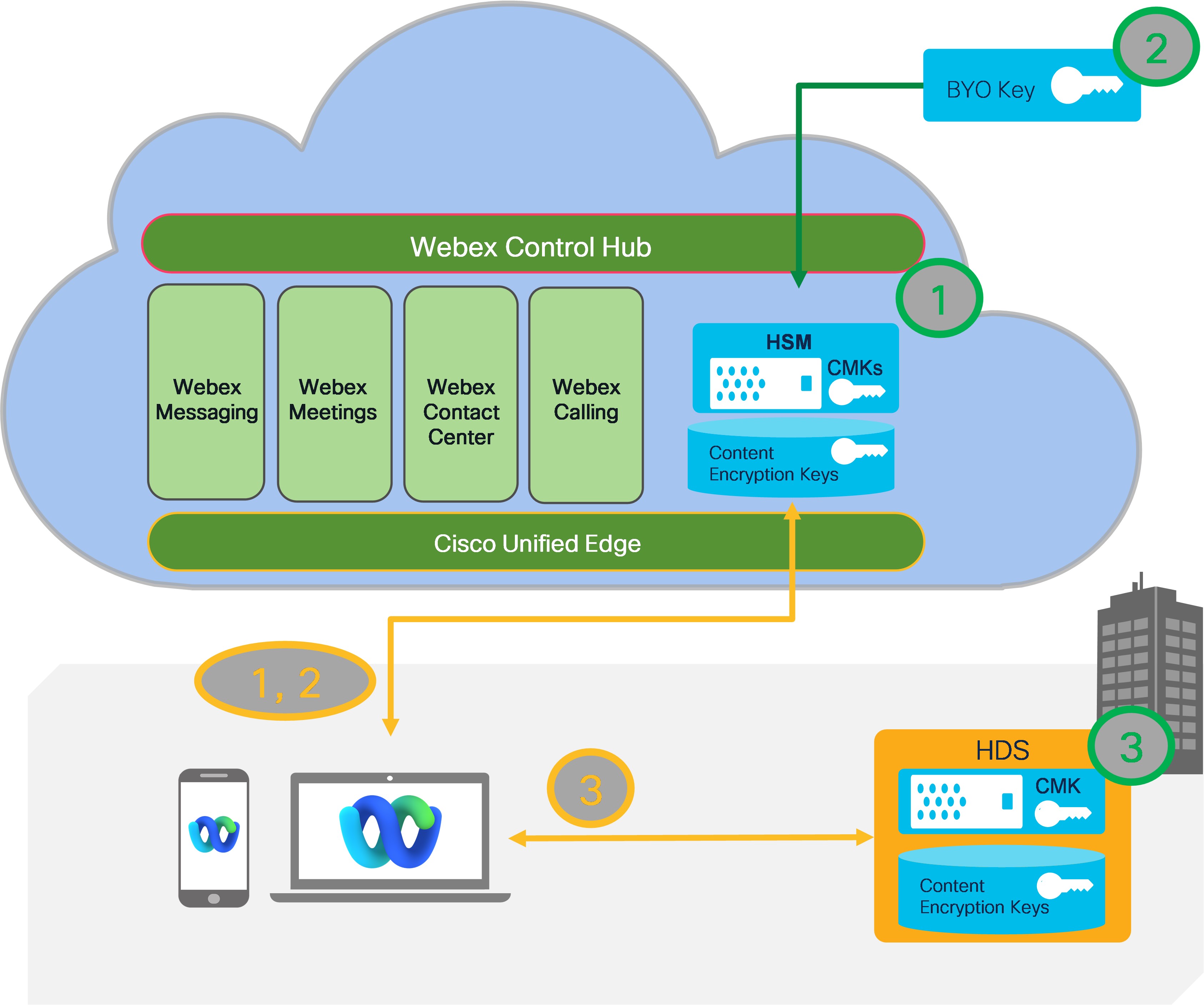
Webex KMS provides an additional layer of encryption at rest for your organization’s user-generated content, and supports a number of deployment options, depending on the level of security and control that your organization requires:
- Webex Cloud-based KMS with Webex Cloud HSM-derived Customer Main Key.
- Webex Cloud-based KMS with Customer Main Key derived from customer key (BYOK). For more information, see Manage your own customer main key.
- Webex Cloud-based KMS with Customer Main Key from customer's AWS KMS. For more information, see Manage your own customer main key
- Customer premises-based KMS (Hybrid Data Security (HDS)) – keys stored on premises. For more information, see Deployment guide for Webex Hybrid Data Security.
- Partner managed premises-based KMS (Hybrid Data Security (HDS)) – keys stored on premises. For more information, see Deployment guide for Webex Hybrid Data Security.
For technical details on KMS operation, see Webex Messaging Security Cloud Collaboration Security Technical Paper.
Webex Meetings that use KMS for content encryption also benefit from a common set of compliance tools that can be used to manage, archive, and enforce customer policies on user-generated content in Webex Meetings. This common compliance architecture uses the Webex Events API to provide the following services for meetings, chat, files, whiteboards, annotations, recordings, and transcripts:
- Legal hold (overrides retention policy)
- e-Discovery (compliance officer search)
- Data Loss Prevention–send messages and files to your DLP application for data policing
- Data archival


