- Startseite
- /
- Artikel





Cisco IOS-verwaltete Gateways bei Webex Cloud anmelden
 In diesem Artikel
In diesem Artikel Feedback?
Feedback?Durch die Verbindung Ihrer IOS-verwalteten Gateway-Geräte mit Cisco Webex Control Hub können Sie diese zusammen mit dem Rest Ihrer Unified Communications-Infrastruktur von überall aus verwalten und überwachen.
Verwaltete Gateways
Durch die Registrierung Ihrer Cisco IOS-Gateways beim Control Hub wird die Geräteverwaltung vereinfacht und Sie können neue Webex Calling-Dienste nutzen. Da die Gateways eine Verbindung zum Control Hub aufrechterhalten, können Sie sie zusammen mit Ihren übrigen Webex Calling-Geräten von überall aus verwalten und überwachen. Um ein Gateway zu registrieren, müssen Sie eine Management-Connector-Anwendung installieren und sicherstellen, dass eine sichere Verbindung zur Cisco Webex-Cloud besteht. Nachdem Sie diese Verbindung hergestellt haben, können Sie das Gateway registrieren, indem Sie sich im Control Hub anmelden.
Dieser Prozess gilt nicht für Cisco IOS Voice Gateways wie den VG400, der vollständig als Gerät im Control Hub verwaltet wird.
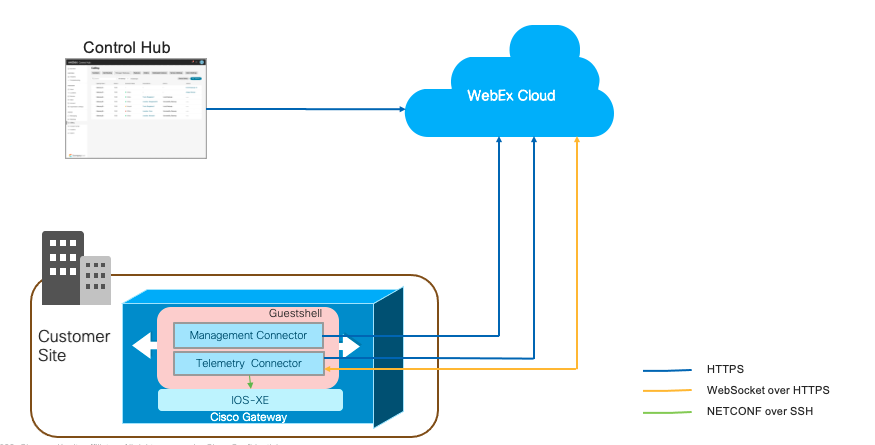
Eine kleine Verbindungsanwendung, bekannt als GuestShell, ist für den Aufbau und die Aufrechterhaltung einer Verbindung vom Gateway zum Control Hub zuständig. Die GuestShell- und Connector-Anwendungen werden mithilfe eines Skripts konfiguriert und eingerichtet, das während des Registrierungsprozesses vom Webex-Cloud-Server auf dem Gateway ausgeführt wird.
Um den Installationsprozess zu vereinfachen, fügt das Skript eine Reihe notwendiger Gateway-Konfigurationen hinzu.
Gateway-Anschlüsse
Gateway-Konnektoren sind kleine Anwendungen, die in der Gateway-Gastshell ausgeführt werden, um eine Verbindung zum Control Hub aufrechtzuerhalten, Ereignisse zu koordinieren und Statusinformationen zu sammeln. Weitere Informationen zu GuestShell finden Sie unter GuestShell.
Die Gateway-Konnektoren sind im Cisco IOS XE GuestShell-Container installiert.
Es gibt zwei Arten von Steckverbindern:
-
Management-Connector
-
Telemetrieanschluss
Ein interaktives, menügesteuertes TCL-Skript hilft bei der Einrichtung der Gast-Shell sowie bei der Installation und Wartung des Management-Connectors.
Der Management-Connector kümmert sich um die Gateway-Registrierung und das Lebenszyklusmanagement des Telemetrie-Connectors.
Nach erfolgreichem Abschluss der Registrierung lädt der Management-Connector den neuesten Telemetrie-Connector herunter und installiert ihn.
Die folgende Grafik zeigt, wie die verschiedenen Komponenten in einer Webex Calling-Lösung miteinander verbunden sind:
Im Rahmen der TCL-Skriptausführung werden folgende Informationen vom Benutzer erfasst:
-
Externe Schnittstelle
-
DNS-Serveradressen
-
Proxy-Details
-
Connector-IP-Adresse
-
Gateway-Zugangsdaten (Benutzername und Passwort)
Das TCL-Skript führt die folgenden Konfigurationen durch:
-
Virtuelle Portgruppe – Erforderlich für die Gastshell-Konfiguration.
-
Gästehaus
-
NETCONF Yang
-
SNMP-Trap-Konfiguration – Erforderlich für Benachrichtigungen von Cisco IOS XE.
-
IP-Route – Um den mit Connectors verbundenen Datenverkehr über eine virtuelle Portgruppe zu leiten.
Das TCL-Skript führt die folgenden Konfigurationen durch:
!
interface VirtualPortGroup 0
ip unnumbered GigabitEthernet1
no mop enabled
no mop sysid
!
!
app-hosting appid guestshell
app-vnic gateway0 virtualportgroup 0 guest-interface 0
guest-ipaddress 10.65.125.227 netmask 255.255.255.128
app-default-gateway 10.65.125.142 guest-interface 0
app-resource profile custom
cpu 800
memory 256
persist-disk 500
name-server0 72.163.128.140
name-server1 8.8.8.8
!
!
netconf-yang
netconf-yang cisco-ia snmp-trap-control trap-list 1.3.6.1.4.1.9.9.41.2.0.1
netconf-yang cisco-ia snmp-community-string Gateway-Webex-Cloud
!
!
logging snmp-trap emergencies
logging snmp-trap alerts
logging snmp-trap critical
logging snmp-trap errors
logging snmp-trap warnings
logging snmp-trap notifications
!
!
snmp-server community Gateway-Webex-Cloud RO
snmp-server enable traps syslog
snmp-server manager
!
!
ip route 10.65.125.227 255.255.255.255 VirtualPortGroup0
!
Für die Beispielkonfiguration:
-
GigabitEthernet1 ist als externe Schnittstelle zugewiesen. Die IP-Adresse von GigabitEthernet1 lautet 10.65.125.142.
-
Die IP-Adresse des Connectors muss sich im selben Netzwerk befinden wie die für die externe Verbindung gewählte Adresse. Es kann sich um eine private Netzwerkadresse handeln, aber sie muss über HTTPS-Zugang zum Internet verfügen.
-
Das TCL-Skript verfolgt und speichert die Konfigurationsänderungen in der Cisco IOS XE-Startkonfiguration.
-
Im Rahmen des Deinstallationsprozesses entfernt das TCL-Skript die Konfigurationsänderungen.
Einschränkungen und Beschränkungen
Beachten Sie vor der Installation, dass die Connector-Anwendung nicht mit Folgendem kompatibel ist:
- Cisco 1100 Integrated Services Router-Plattformen
- Plattformen, die im Hochverfügbarkeitsmodus (HA) konfiguriert sind
- Plattformen, die im Controller-Modus für SD-WAN-Netzwerke konfiguriert sind
Bei Cisco IOS Voice Gateways wie dem VG400 ist die Installation der Connector-Anwendung nicht erforderlich. Über den Control Hub können Sie es vollständig konfigurieren und verwalten.
Beachten Sie Folgendes bei der Konfiguration Ihres Routers für die Verwendung mit einer Connector-Anwendung:
-
IOS XE verwendet Proxy-ARP, um den Datenverkehr an die Gast-Shell weiterzuleiten. Konfigurieren Sie nicht den Befehl no ip proxy-arp, um diese Funktion zu deaktivieren.
-
Verwenden Sie keine Netzwerkadressübersetzung (NAT) auf Plattformen, die für ein Cisco Unified Border Element (CUBE) konfiguriert sind. Konfigurieren Sie daher die Connector-Anwendung mit einer routingfähigen IP-Adresse. Das heißt, es kann die Router-Schnittstellenadresse nicht gemeinsam nutzen.
Voraussetzungen
Bereiten Sie Ihr Gerät für die Gateway-Registrierung vor:
-
Zugriff auf den Control Hub als Organisationsadministrator
-
IP-Adresse, Benutzername und Passwort für die Geräte, die Sie konfigurieren möchten.
-
Cisco IOS XE Version:
-
Lokale Gateways – Cisco IOS XE Bengaluru 17.12.3 oder höher
-
Survivability Gateways – Cisco IOS XE Dublin 17.12.3 oder höher
Die empfohlenen Versionen finden Sie unter Cisco Software Research. Suchen Sie nach der Plattform und wählen Sie eine der vorgeschlagenen Versionen aus.
-
-
Systemvoraussetzungen
-
Mindestens 256 MB freier Speicherplatz.
-
Mindestspeicherplatz – Die an das Gateway angeschlossene Festplatte (SSD), die für die Konnektorinstallation verwendet wird, muss über 2000 MB freien Speicherplatz verfügen. Außerdem müssen auf dem Bootflash-Speicher 50 MB freier Speicherplatz vorhanden sein. Es dient zum Speichern der Protokolle und RPM-Dateien.
Wenn keine Festplatte an das Gateway angeschlossen ist, wird Bootflash für die Anschlussinstallation verwendet. Dann müssen auf dem Bootflash-Laufwerk 2000 MB freier Speicherplatz vorhanden sein.
-
Wenn der Bootflash Ihres Routers 4 GB groß ist und weniger als 2 GB Speicherplatz zur Verfügung stehen (die Mindestkapazität), löschen Sie alle IOS-Binärdateien (.bin) außer derjenigen, die aktuell ausgeführt wird. Nachdem Sie die Dateien gelöscht haben, schaffen Sie zusätzlichen Speicherplatz.
Die folgenden Schritte sind optional, um Speicherplatz auf dem Bootflash-Speicher freizugeben. Führen Sie die folgenden Schritte nur dann aus und ändern Sie die Bootdateien in den Installationsmodus, wenn:
-
Der Router verwendet den mitgelieferten Boot-Modus (Booten von .bin).
-
Die Datei .pkgs ist noch nicht extrahiert (Installationsmodus).
Führen Sie die folgenden Schritte aus, um das Binärabbild zu erweitern und von den Komponenten zu booten:
-
Erstellen Sie ein neues Verzeichnis mit folgendem Befehl:
mkdir bootflash:/image -
Erweitern Sie das IOS-Binärimage mithilfe von
request platform software package expand file bootflash:/.bin to bootflash:/image
-
Im Konfigurationsmodus werden die aktuellen Boot-Optionen entfernt.
no boot system -
Konfigurieren Sie eine neue Boot-Anweisung:
boot system bootflash:/image/packages.conf. -
Beenden Sie den Konfigurationsmodus, speichern Sie die Konfiguration und starten Sie das System neu.
-
Sobald der Router neu gestartet wurde, verwenden Sie
show version[ ], um zu überprüfen, ob der Router vonbootflash:/image/packages.confgestartet wurde. Falls ja:-
Überprüfen Sie, ob das Verzeichnis
bootflash:/sysbootleer ist. -
Löschen Sie das verbleibende IOS-Binärabbild.
-
Löschen Sie alle Core-Images mit Hilfe von
delete /f /r bootflash:/core/* -
Löschen Sie Trace-Protokolldateien mit folgendem Befehl:
delete /f /r bootflash:/tracelogs/* -
Sollte der Speicherplatz weiterhin nicht ausreichen, überprüfen Sie die verbleibenden Dateien im Bootflash-Ordner: und löschen Sie alle anderen nicht benötigten Dateien wie Protokolle und CDRs.
-
-
Ein unterstützter Cisco-Router, der mit einem Netzwerk verbunden ist, das über einen Internetzugang verfügt. Die Basiskonfiguration muss Folgendes umfassen:
-
Der DNS-Server ist so konfiguriert, dass er öffentliche Domänennamen auflöst.
-
Um den DNS-Server zu konfigurieren, verwenden Sie folgenden Befehl:
-
IP-Nameserver <IP address>
-
-
HTTP-Proxy-Server, falls Sie über einen Proxy auf das Internet zugreifen möchten.
-
Gateway-Zugangsdaten: Für den Zugriff des Konnektors auf das Gateway über seine NETCONF-Schnittstelle werden lokale Anmeldeinformationen (Benutzername und Passwort) mit Zugriffsberechtigungsstufe 15 benötigt.
Um den NETCONF-Zugriff zu authentifizieren und zu autorisieren, stellen Sie sicher, dass die Standard-AAA-Listen wie im folgenden Beispiel dargestellt konfiguriert sind. Nur die in diesem Dokument aufgeführten Befehle wurden validiert und werden für Managed Gateways unterstützt. Konfigurationen, die andere Methoden (z. B. TACACS oder ISE) beinhalten, wurden nicht validiert und werden derzeit nicht unterstützt.
aaa new-model aaa authentication login default local aaa authorization exec default local if-authenticated username test privilege 15 secret
Netzwerkvoraussetzungen
-
Die IP-Adresse des Connectors muss sich im selben Netzwerk befinden wie die für die externe Verbindung gewählte Adresse. Es kann sich um eine private Netzwerkadresse handeln, aber sie muss über HTTPS-Zugang zum Internet verfügen.
Wenn Sie Virtual CUBE auf Amazon Web Services (AWS) als Ihr lokales Gateway verwenden, finden Sie unter Zuordnen einer sekundären IP-Adresse für Virtual CUBE auf AWS Anweisungen zum Zuordnen einer sekundären IP-Adresse für die Connector-Nutzung.
-
Um den Registrierungsprozess abzuschließen, müssen Sie mit dem Control Hub und den Geräten vor Ort verbunden sein.
-
URLs für Webex-Dienste:
-
*.ucmgmt.cisco.com
-
*.webex.com
-
*.wbx2.com
-
-
Transportprotokolle: Transport Layer Security (TLS) Version 1.2
-
Importieren Sie das öffentliche iOS-Zertifizierungsstellen-Bundle. Die dem Gateway-Vertrauenspool hinzugefügten Zertifikate werden verwendet, um den Zugriff auf Webex-Server zu überprüfen. Verwenden Sie den folgenden Konfigurationsbefehl, um das Bundle zu importieren.
crypto pki trustpool import url https://www.cisco.com/security/pki/trs/ios.p7b
-
Ordnen Sie Virtual CUBE auf AWS eine sekundäre IP-Adresse zu.
Wenn Sie Virtual CUBE auf AWS als Ihr lokales Gateway verwenden, führen Sie die folgenden Schritte auf der AWS-Oberfläche durch, um eine sekundäre IP-Adresse für die Connector-Nutzung zuzuordnen.
Wir empfehlen Ihnen, diese Aktivität während eines Wartungsfensters durchzuführen.
Vorbereitungen
-
Um Virtual CUBE auf Amazon Web Services (AWS) als Ihr lokales Gateway zu verwenden, müssen Sie der Gateway-Schnittstelle eine sekundäre private IP-Adresse zuordnen. Sie können diese IP-Adresse als Connector-IP-Adresse verwenden.
-
Ordnen Sie der sekundären IP-Adresse eine Elastic öffentliche IP-Adresse zu, damit die sekundäre IP-Adresse für die Gateway-Registrierung öffentlich verfügbar ist.
-
Die zugehörige Sicherheitsgruppenrichtlinie muss HTTPS-Eingangsverkehr zulassen, damit die Registrierung erfolgreich ist. Sie können dies entfernen, sobald die Anmeldung abgeschlossen ist.
| 1 |
Gehen Sie zu Dienste > EC2 > Instanzenund wählen Sie die Cisco-Gateway-Instanz aus. |
| 2 |
Klicken Sie im Fenster Netzwerkschnittstellen auf eth0. In einem Dialogfeld werden detaillierte Informationen zur eth0 Schnittstelle angezeigt. |
| 3 |
Klicken Sie auf Schnittstellen-ID-Wert. |
| 4 |
Klicken Sie auf Aktionenund wählen Sie in der Dropdown-Liste IP-Adresse verwalten aus. |
| 5 |
Erweitern Sie eth0 und wählen Sie neue IP-Adresse zuweisen und bestätigen Sie die Zuweisung. Beachten Sie diese sekundäre IP-Adresse. |
| 6 |
Klicken Sie auf Aktionen und wählen Sie Zugeordnete Adresse aus der Dropdown-Liste aus. |
| 7 |
Wählen Sie eine verfügbare öffentliche IP-Adresse aus der Liste Elastic IP-Adresse aus. Prüfen Sie, ob die ausgewählte IP-Adresse mit der von Ihnen notierten sekundären IP-Adresse übereinstimmt. |
| 8 |
(Optional) Um eine öffentliche IP-Adresse, die derzeit verwendet wird und einer anderen elastischen Netzwerkschnittstelle (ENI) zugeordnet ist, neu zuzuweisen, klicken Sie auf Neuzuordnung zulassen. |
| 9 |
Klicken Sie auf Adresse zuordnen, um die öffentliche IP-Adresse (Amazon Elastic IP) mit der privaten IP-Adresse der Netzwerkschnittstelle zu verknüpfen. |
Sie können diese private IP-Adresse nun als Connector-IP-Adresse während der Connector-Installation verwenden. Verwenden Sie die entsprechende öffentliche IP-Adresse (Amazon Elastic IP-Adresse) für die Registrierung im Control Hub.
Fügen Sie im Control Hub eine neue Gateway-Instanz hinzu.
Wenn Sie das Gateway bereits zum Control Hub hinzugefügt und den Management Connector installiert haben, können Sie diesen Schritt überspringen. Gehen Sie zu Schritt 5 von Gateway beim Control Hub anmelden, um den Anmeldevorgang abzuschließen.
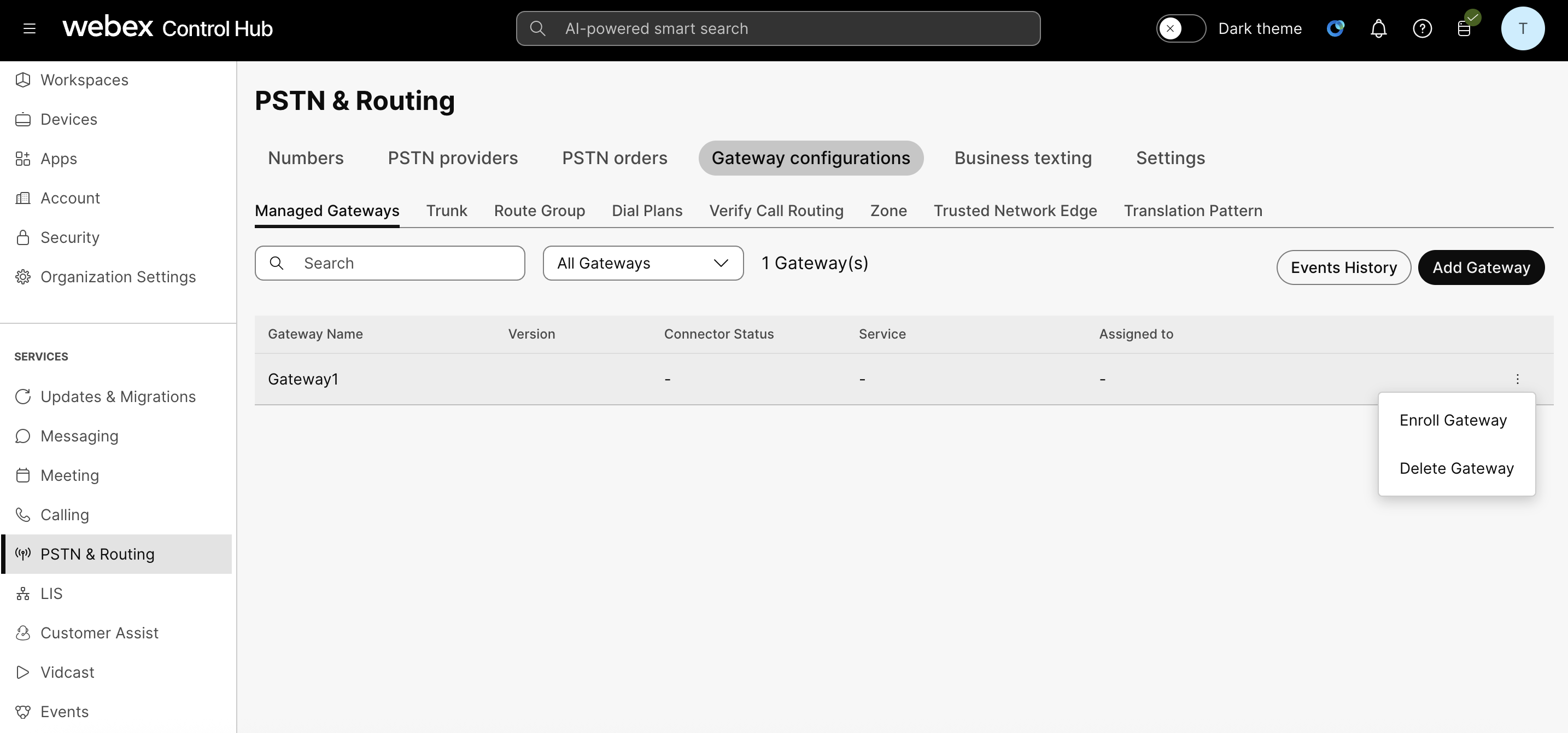
| 1 | |
| 2 |
Gehen Sie zu . |
| 3 |
Klicken Sie auf Gateway hinzufügen. |
| 4 |
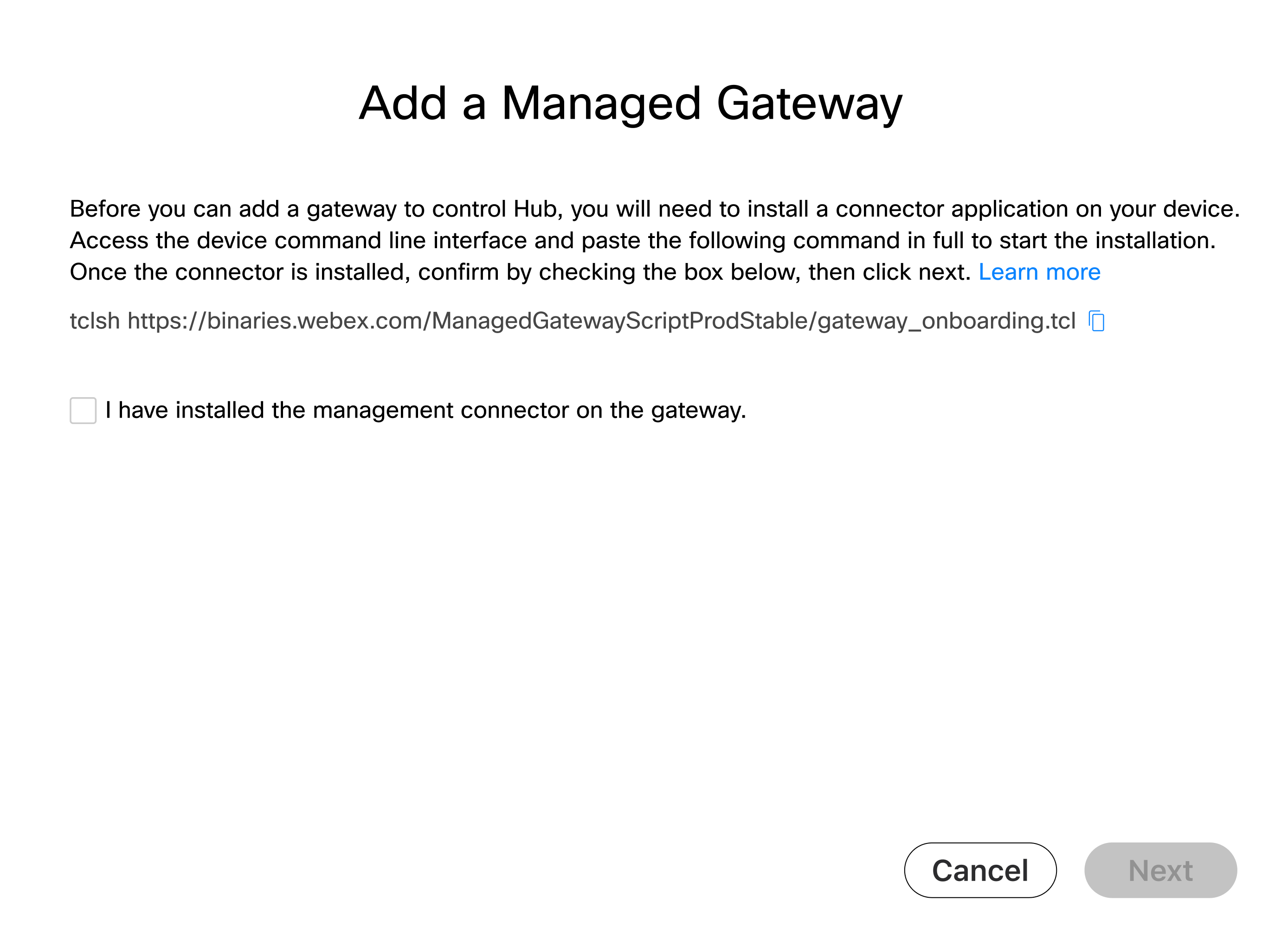
Kopieren Sie den im Fenster „Verwaltetes Gateway hinzufügen“ angezeigten tclsh - Befehl. Sie müssen den Befehl während der Installation des Management-Connectors auf der Gateway-CLI ausführen. |
Nächste Schritte
Sie können den Registrierungsprozess im Control Hub fortsetzen, nachdem der Konnektor auf dem Gateway installiert wurde.
Installieren Sie den Gateway-Connector.
Bevor Sie mit der Installation des Management-Connectors fortfahren, stellen Sie sicher, dass Sie alle Voraussetzungenerfüllen.
Führe das Skript aus
|
Melden Sie sich über eine Konsolen- oder SSH-Verbindung am Gateway an und fügen Sie anschließend die folgende Zeichenfolge in die Befehlszeile des Routers ein: tclsh https://binaries.webex.com/ManagedGatewayScriptProdStable/gateway_onboarding.tcl
|
Starten Sie die Installation
Wenn der Konnektor noch nicht eingerichtet ist, werden Sie vom Skript zum Installationsmenü weitergeleitet; wenn der Konnektor eingerichtet ist, werden Sie zum Startmenü weitergeleitet.
| 1 |
Wählen Sie die Schnittstelle, die sich im selben Netzwerk befindet wie die für den Connector reservierte Adresse.
|
| 2 |
Konfigurieren Sie den DNS-Server, der vom Connector verwendet werden soll. Standardmäßig werden die in IOS konfigurierten Server verwendet.
Y ist hier die Standardeingabe. Wenn Sie und danndrücken, wird Y als Eingabe interpretiert. Die erkannten Einstellungen können bei Bedarf überschrieben werden: |
| 3 |
Falls Sie einen Proxy benötigen, um auf das Internet zuzugreifen, geben Sie die Proxy-Daten ein, wenn Sie dazu aufgefordert werden. Wenn das Gateway bereits mit einem Proxy konfiguriert wurde, werden standardmäßig die folgenden Details verwendet. Geben Sie n ein, um diese Einstellungen bei Bedarf zu überschreiben.
|
| 4 |
Konfigurieren Sie die SNMP-Trap-Einstellungen. Um Benachrichtigungen an die Cisco Webex Cloud zu senden, aktualisiert das Skript die SNMP-Trap-Konfigurationsebene im Router, falls diese unterhalb der Benachrichtigungsebene eingestellt ist. Das System fordert Sie auf, zu bestätigen, ob die SNMP-Trap-Konfiguration auf die Benachrichtigungsebene geändert werden soll. Um die aktuelle SNMP-Trap-Konfigurationsebene beizubehalten, wählen Sie n. |
| 5 |
Geben Sie die IP-Adresse des Connectors ein.
|
| 6 |
Geben Sie den Benutzernamen und das Passwort ein, die der Connector für den Zugriff auf die NETCONF-Schnittstelle des Routers verwendet.
Geben Sie das Passwort manuell ein. Kopieren und Einfügen funktioniert möglicherweise nicht. Geben Sie die Gateway-Zugangsdaten ein, die Sie im Abschnitt Voraussetzungen angegeben haben. Der Konnektor verwendet die Anmeldeinformationen, um auf die IOS NETCONF-Schnittstelle des Routers zuzugreifen. Nach
Sie können das Skript nach erfolgreicher Installation durch Auswahl der Option „q“ beenden. Im Falle eines Installationsfehlers können Sie die Option „h“ wählen, um beliebige Einstellungen zu ändern, Protokolle zu sammeln usw. Weitere Einzelheiten finden Sie im Abschnitt Aktivitäten nach der Installation. Wenn Sie die Installation wiederholen möchten, können Sie die Deinstallation auswählen und anschließend das Skript erneut starten, um die Installation erneut zu versuchen. Sie können das TCL-Skript jederzeit direkt mit |
Melden Sie das Gateway beim Control Hub an.
Vorbereitungen
| 1 | |
| 2 |
Gehen Sie zu . |
| 3 |
Klicken Sie auf Gateway hinzufügen. |
| 4 |
Im Fenster Verwaltendes Gateway hinzufügen, aktivieren Sie Ich habe den Management Connector auf dem Gateway installiert und klicken Sie auf Weiter. Stellen Sie sicher, dass der Stecker ordnungsgemäß installiert ist, bevor Sie diesen Schritt ausführen.
|
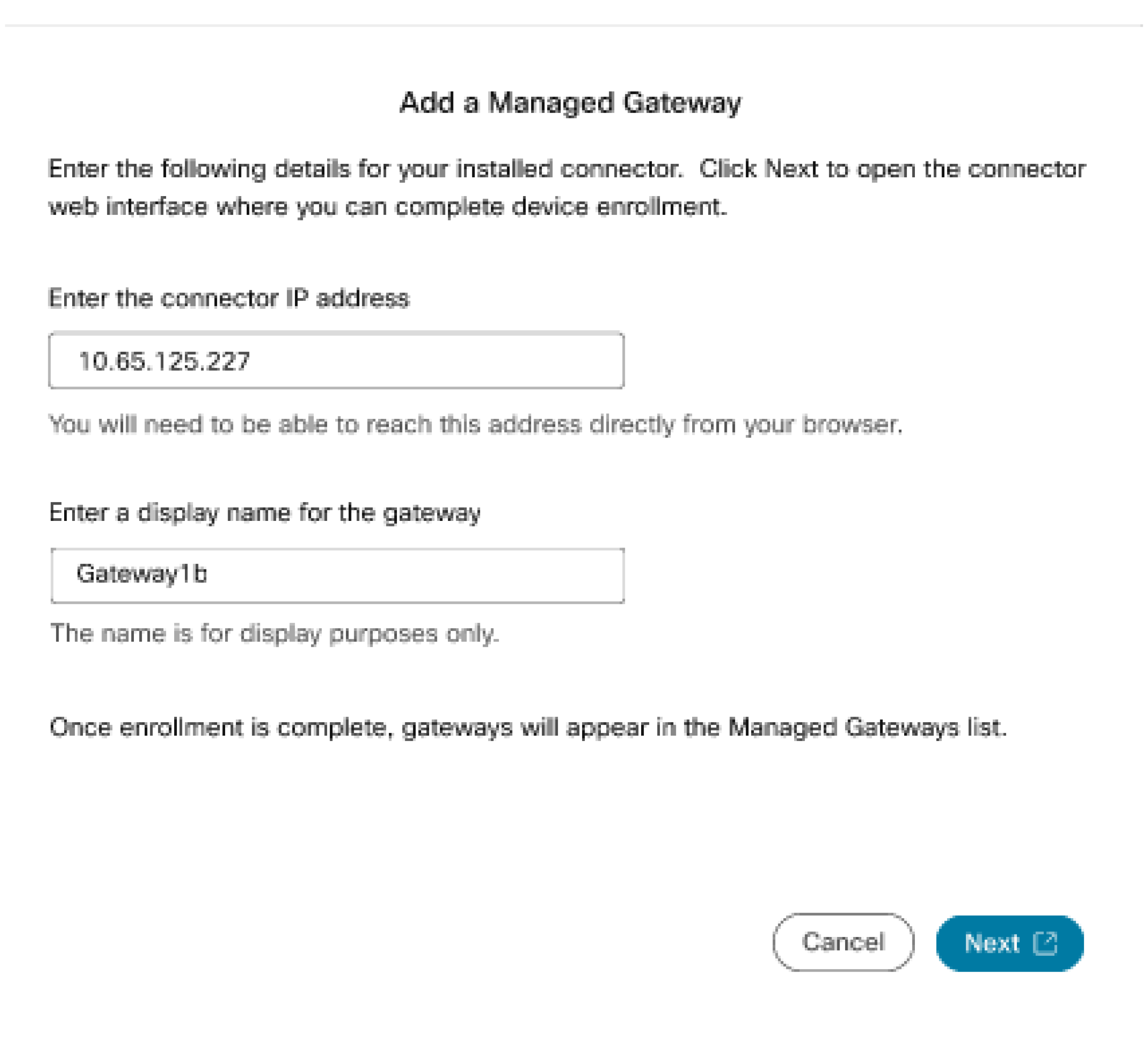
| 5 |
Geben Sie auf der Seite "Verwaltetes Gateway hinzufügen" die folgenden Details ein:
|
| 6 |
Klicken Sie auf Weiter.
Es öffnet sich ein Browser-Tab, der eine Verbindung zur Connector-Verwaltungsseite des Routers herstellt, damit Sie die Registrierung abschließen können.
|
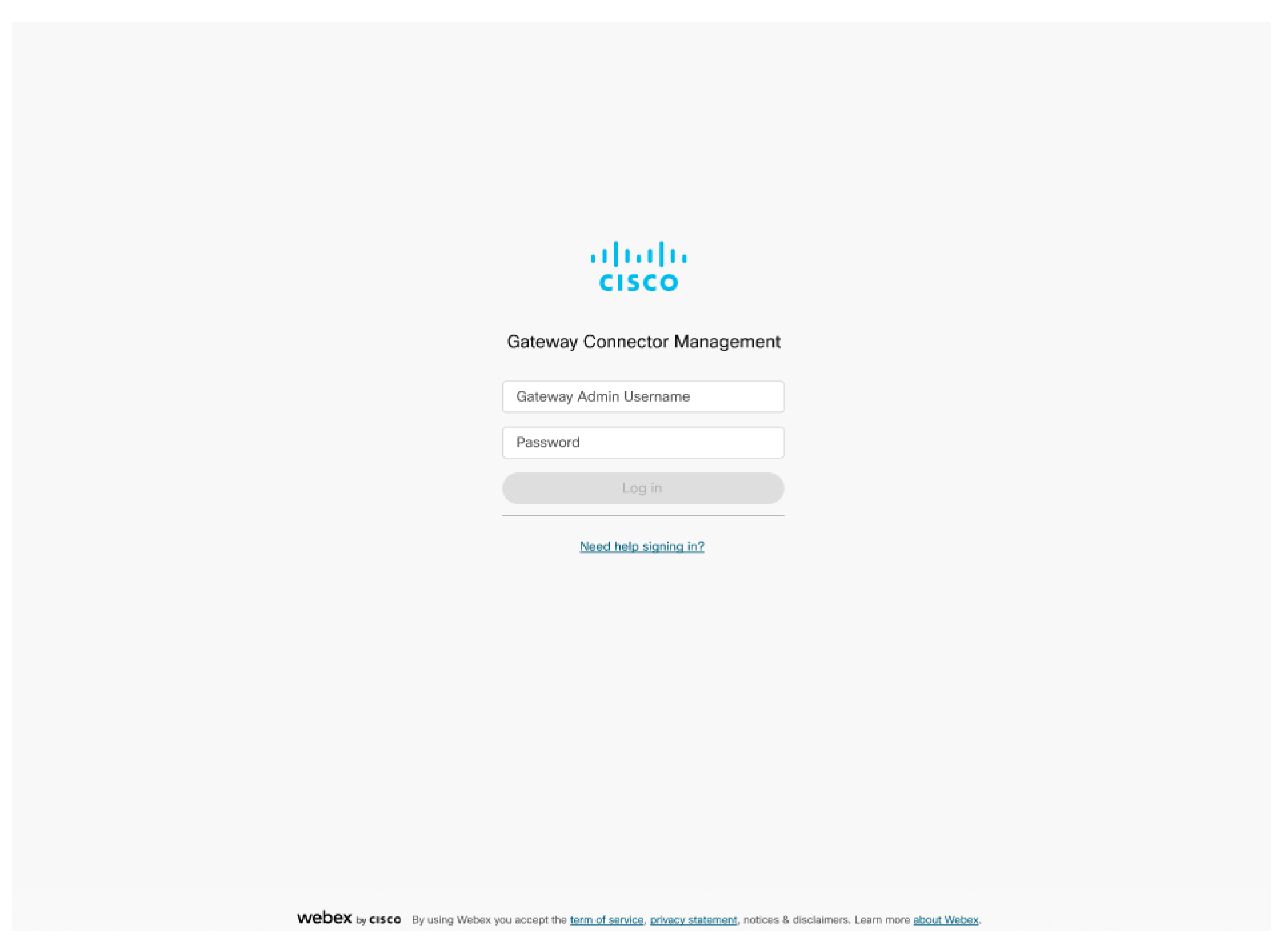
| 7 |
Zum Anmelden geben Sie den Gateway-Administrator-Benutzernamen und das Passwort ein, die Sie während der Konnektorinstallationsprozedur verwendet haben, die in Schritt 6 aufgeführt ist.
|
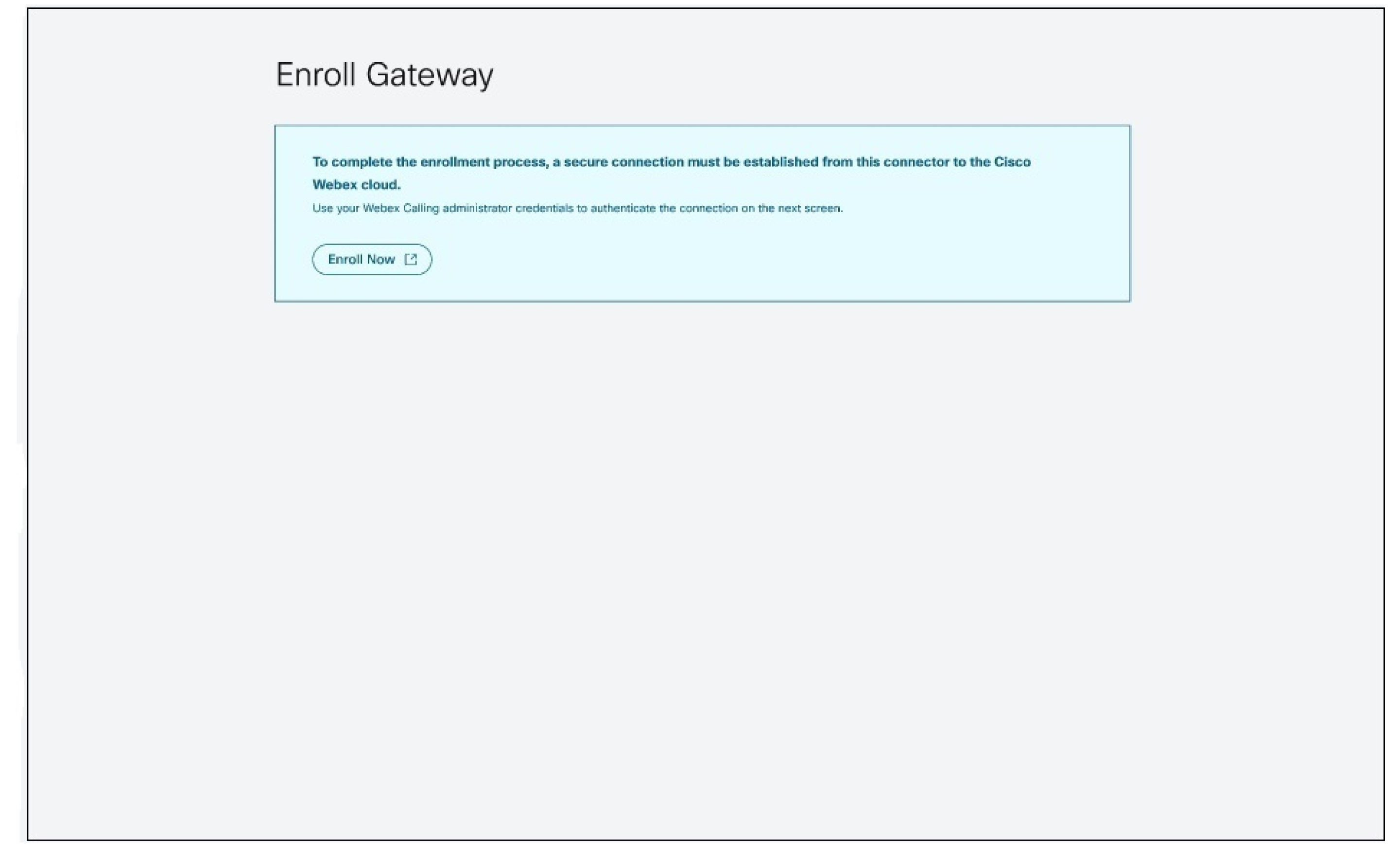
| 8 |
Klicken Sie auf Jetzt anmelden, um ein neues Fenster zur Authentifizierung des Connectors an die Webex-Cloud zu öffnen. Stellen Sie sicher, dass Ihr Browser Pop-ups zulässt.
|
| 9 |
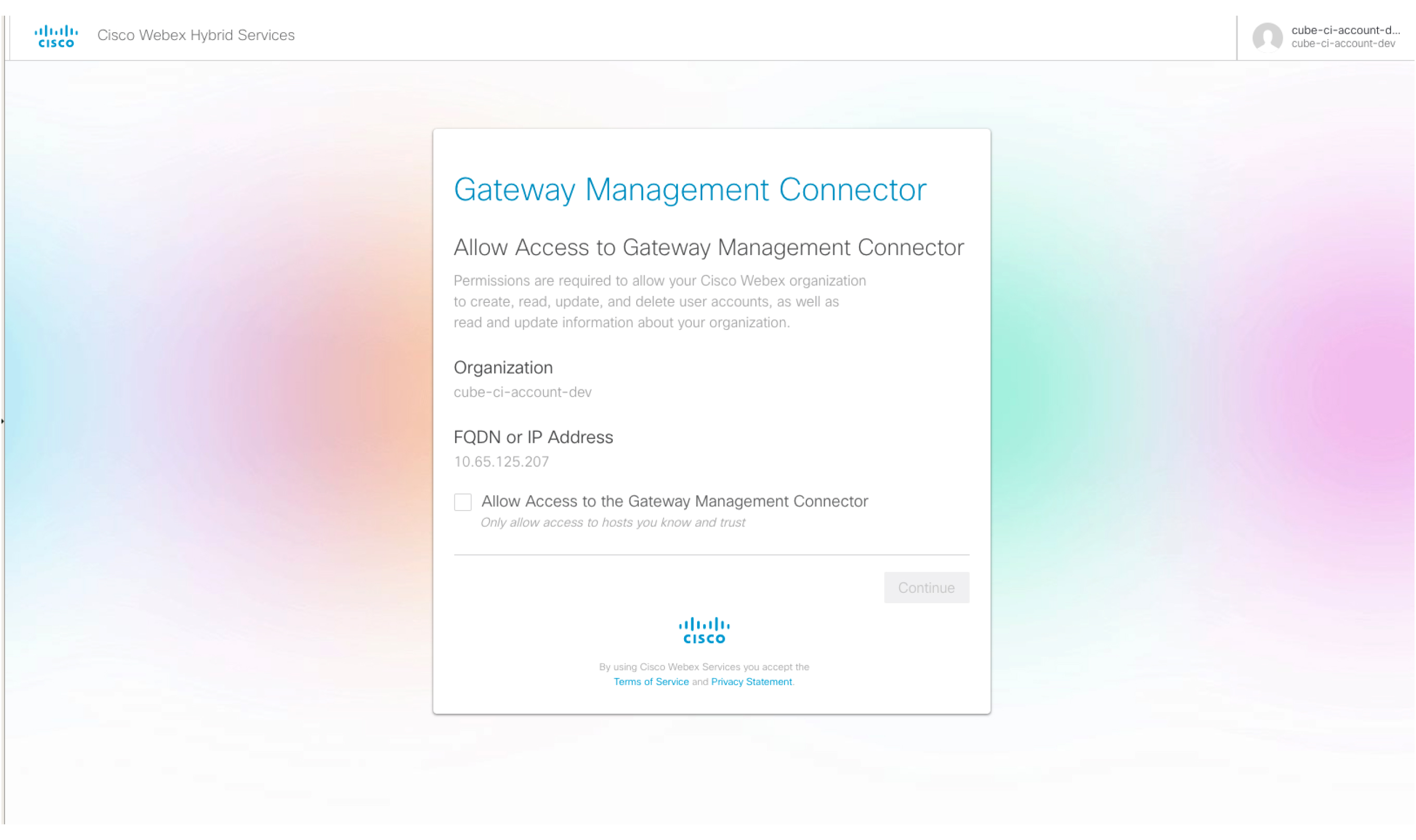
Melden Sie sich mit einem Webex-Administratorkonto an. |
| 10 |
Aktivieren Sie Zugriff auf den Gateway-Verwaltungskonnektor zulassen .
|
Gateway-Connector-Zustände
Der Gesamtstatus des im Control Hub angezeigten Konnektors hängt vom Status der Telemetrie- und Management-Konnektoren auf dem Managed Gateway ab.
| Verbindungszustände im Control Hub | Beschreibung |
|---|---|
| Online | Zeigt an, dass der Connector mit der Cisco Webex Cloud verbunden ist. |
| Offline | Zeigt an, dass der Connector nicht mit der Cisco Webex Cloud verbunden ist. |
| Angehalten | Zeigt an, dass der Stecker angeschlossen , aber vorübergehend pausiert ist. |
Verbindungsalarme und -ereignisse
Dieser Abschnitt beschreibt Alarme, die im Telemetrie-Anschlussmodul generiert werden. Der Telemetrie-Connector sendet Alarme an die Cisco Webex Cloud. Im Control Hub, Seite zeigt diese Alarme an.
Mithilfe der auf der Ereignisdetailseite angezeigten Tracking-ID können Sie diese mit den entsprechenden Protokollen auf der Konnektorseite korrelieren.
Die folgende Tabelle beschreibt die mit dem Konnektor verbundenen Meldungen:
|
Titel |
Beschreibung |
Schweregrad |
Lösung |
|---|---|---|---|
|
Telemetriemodul gestartet. |
Diese Nachricht wird gesendet, sobald das Telemetriemodul funktionsfähig ist. |
Meldung |
k. A. |
|
Telemetriemodul aktualisiert. |
Diese Meldung wird gesendet, wenn das Telemetriemodul von "old_version" auf "new_version" aktualisiert wurde. |
Meldung |
k. A. |
|
NETCONF-Verbindungsfehler. |
Dieser Alarm wird ausgelöst, wenn das Telemetriemodul keine NETCONF-Verbindung zum Gateway herstellen kann. |
Kritisch |
Vergewissern Sie sich, dass NETCONF auf dem Gateway aktiviert ist und dass es vom Konnektor erreichbar ist. Versuchen Sie, den Konnektor-Container zu deaktivieren und anschließend zu aktivieren. Sollte das Problem weiterhin bestehen, gehen Sie zu https://help.webex.com/contact, klicken Sie auf Supportund eröffnen Sie einen Fall. |
|
NETCONF-Authentifizierungsfehler. |
Dieser Alarm wird ausgelöst, wenn das Telemetriemodul keine NETCONF-Verbindung zum Gateway herstellen kann. |
Kritisch |
Überprüfen Sie, ob Benutzername und Passwort auf dem Gateway korrekt konfiguriert sind. Versuchen Sie, den Konnektor-Container zu deaktivieren und anschließend zu aktivieren. Sollte das Problem weiterhin bestehen, gehen Sie zu https://help.webex.com/contact, klicken Sie auf Supportund eröffnen Sie einen Fall. |
|
NETCONF SNMP-Ereignisabonnement fehlgeschlagen. |
Dieser Alarm wird ausgelöst, wenn das Telemetriemodul kein NETCONF-Abonnement für SNMP-Ereignisse erstellen kann. |
Kritisch |
Überprüfen Sie, ob NETCONF auf dem Gateway aktiviert ist und ob es im Connector erreichbar ist. Versuchen Sie, den Konnektor-Container zu deaktivieren und anschließend zu aktivieren. Sollte das Problem weiterhin bestehen, gehen Sie zu https://help.webex.com/contact, klicken Sie auf Supportund eröffnen Sie einen Fall. Weitere Informationen zum Aktivieren und Deaktivieren finden Sie unter Aktivitäten nach der Installation. |
|
Fehler bei der Erfassung von Telemetriedaten. |
Dieser Alarm wird ausgelöst, wenn das Telemetriemodul keine Metriken vom Gateway über eine NETCONF GET-Abfrage erfassen kann. |
Kritisch |
Vergewissern Sie sich, dass NETCONF auf dem Gateway aktiviert ist und dass es vom Konnektor erreichbar ist. Versuchen Sie, den Konnektor-Container zu deaktivieren und anschließend zu aktivieren. Sollte das Problem weiterhin bestehen, gehen Sie zu https://help.webex.com/contact, klicken Sie auf Supportund eröffnen Sie einen Fall. Weitere Informationen zum Aktivieren und Deaktivieren finden Sie unter Aktivitäten nach der Installation. |
|
Fehler bei der Verbindung zum Telemetrie-Gateway. |
Dieser Alarm wird ausgelöst, wenn der Konnektor keine WebSocket-Verbindung zum Telemetrie-Gateway herstellen kann. |
Kritisch |
Überprüfen Sie, ob die URL des Telemetrie-Gateways (*.ucmgmt.cisco.com) ist in der Zulassungsliste der Unternehmensfirewall enthalten und vom Gateway aus erreichbar. Sollte das Problem weiterhin bestehen, gehen Sie zu https://help.webex.com/contact, klicken Sie auf Supportund eröffnen Sie einen Fall. |
|
Fehler bei der Telemetrie-Gateway-Verbindung über den Proxy. |
Dieser Alarm wird ausgelöst, wenn der Konnektor keine Verbindung zum konfigurierten Proxy herstellen kann. |
Kritisch |
Überprüfen Sie, ob die Proxy-Details (IP-Adresse und Port-Zugangsdaten) auf dem Connector korrekt konfiguriert sind und ob der Proxy erreichbar ist. Sollte das Problem weiterhin bestehen, gehen Sie zu https://help.webex.com/contact, klicken Sie auf Supportund eröffnen Sie einen Fall. |
Connector-Anmeldung
Auf der Seite mit den Verbindungsdetails werden die Verbindungsstatus sowohl der Management- als auch der Telemetrieverbindungen angezeigt.
Melden Sie sich auf der Seite mit den Konnektordetails unter an. https://<connector-ip-address>
Zum Anmelden verwenden Sie die Anmeldedaten, die Sie während der Installation eingegeben haben.
Sie können den Verbindungsstatus auch überprüfen, indem Sie s auswählen. : Option „Statusseite anzeigen “ im TCL-Skript. Siehe Aktivitäten nach der Installation.
In den Tabellen können Sie die Zustände der Anschlussmodule nachvollziehen.
Management-Connector-Zustände
|
Management-Connector-Zustände |
Verbindungsstatus |
Beschreibung |
|---|---|---|
|
Läuft |
Verbunden |
Zeigt an, dass sich der Connector im Status running befindet und das Gerät verbunden mit der Cisco Webex Cloud ist. |
|
Läuft |
Nicht verbunden |
Zeigt an, dass sich der Connector im Status running befindet, das Gerät jedoch nicht mit der Cisco Webex Cloud verbunden ist. |
|
Läuft |
Herzschlag versagte |
Zeigt an, dass sich der Konnektor im Status running befindet, aber der Heartbeat für das registrierte Gerät fehlgeschlagen ist. |
|
Läuft |
Einschreibung fehlgeschlagen |
Zeigt an, dass sich der Connector im Status running befindet, die Anmeldung des Geräts bei der Cisco Webex Cloud jedoch fehlgeschlagen ist. |
Zustände des Telemetrieanschlusses
|
Telemetrie-Anschlusszustände |
Verbindungsstatus |
Beschreibung |
|---|---|---|
|
Nicht installiert |
Nicht verfügbar |
Zeigt an, dass der Telemetrieanschluss nicht installiert ist. |
|
Wird heruntergeladen |
Nicht verfügbar |
Zeigt an, dass der Download des Telemetrie-Connectors gerade läuft. |
|
Wird installiert |
Nicht verfügbar |
Zeigt an, dass die Installation des Telemetrieanschlusses im Gange ist. |
|
Nicht konfiguriert |
Nicht verfügbar |
Zeigt an, dass die Installation des Telemetrie-Connectors erfolgreich war, die Dienste jedoch noch nicht gestartet oder konfiguriert wurden. |
|
Läuft |
Nicht verfügbar |
Zeigt an, dass der Telemetrie-Connector läuft, aber Informationen über seine Verbindung zur Cisco Webex-Cloud nicht verfügbar sind. |
|
Läuft |
Verbunden |
Zeigt an, dass sich der Telemetrie-Connector im Status running befindet und mit der Cisco Webex Cloud verbunden ist. |
|
Läuft |
Nicht verbunden |
Zeigt an, dass sich der Telemetrie-Connector im Status running befindet, aber nicht mit der Cisco Webex Cloud verbunden ist. |
|
Läuft |
Herzschlag versagte |
Zeigt an, dass sich der Telemetrie-Connector im Status running befindet und der Telemetrie-Heartbeat zur Cisco Webex Cloud fehlgeschlagen ist. |
|
Deaktiviert |
Nicht verfügbar |
Zeigt an, dass sich der Telemetrie-Connector im Wartungsmodus (deaktivierter Zustand) befindet und Informationen über seine Verbindung zur Cloud nicht verfügbar sind. |
|
Angehalten |
Verbindung getrennt |
Zeigt an, dass sich der Telemetrie-Connector im Zustand gestoppt befindet (möglicherweise ist er nur teilweise gestoppt oder sowohl der Telemetrie-Dienst als auch der WebSocket-Broker-Dienst sind gestoppt) und dass er nicht mit der Cisco Webex-Cloud verbunden ist. |
Aktivitäten nach der Installation
Lokale Verwaltung des Management Connectors
Sie können Webex Calling mit Ihrem Gateway nutzen, nachdem Sie den Connector erfolgreich installiert haben. Bei Bedarf können Sie mithilfe der im Skriptmenü verfügbaren Optionen verschiedene Konnektoreinstellungen aktualisieren:
Sie können das Skript jederzeit mit folgendem Befehl neu starten: tclsh
bootflash:/gateway_connector/gateway_onboarding.tcl.
===============================================================
Webex Managed Gateway Connector
===============================================================
Options
s : Display Status Page
v : View and Modify Cloud Connector Settings
e : Enable Guestshell
d : Disable Guestshell
l : Collect Logs
r : Clear Logs
u : Uninstall Connector
q : Quit
===============================================================
Select an option from the menu:Anzeigestatus
Verwenden Sie die Menüoption s: Display Status Page. Das System zeigt den Status verschiedener Anschlussmodule an.
===============================================================
Webex Managed Gateway Connector
===============================================================
-------------------------------------------------------
*** Interface Status ***
-------------------------------------------------------
Interface IP-Address Status
-------------------------------------------------------
GigabitEthernet1 10.123.221.224 up
Connector 10.123.221.223 up
-------------------------------------------------------
*** App Status ***
-------------------------------------------------------
Service Status
-------------------------------------------------------
Guestshell RUNNING
Management Connector RUNNING
-------------------------------------------------------
===============================================================
Select option h for home menu or q to quit: q
Gastshell aktivieren
Aktivieren Sie den Cloud-Connector über die Menüoption e: Enable Guestshell. Dadurch ändert sich der Status des Konnektors von INACTIVE zu ACTIVE.
Gastshell deaktivieren
Deaktivieren Sie den Cloud-Connector über die Menüoption d: Disable Guestshell. Dadurch ändert sich der Status des Konnektors von ACTIVE zu INACTIVE.
Connector deinstallieren
Deinstallieren Sie den Cloud-Connector über die Menüoption u: Uninstall Connector. Dadurch werden alle Daten im Guestshell-Container gelöscht und alle Konfigurationen entfernt, die mit dem Cloud-Connector zusammenhängen.
Sammeln von Protokollen
Sammeln Sie die Protokolle mithilfe der Menüoption l: Collect Logs. Das System zeigt nach dem Sammeln der Protokolle den Speicherort an, an dem diese Protokolle gespeichert sind.
Wenn Sie einen aktiven Supportfall bei Cisco TAC haben, können Sie die Protokolle direkt an Ihre Serviceanfrage anhängen, indem Sie den Befehl copy
bootflash:/guest-share/
scp://:@cxd.cisco.comverwenden.
Nachfolgend ein Beispielbefehl:
vcubeprod#copy bootflash:/guest-share/gateway_webex_cloud_logs_2022114090628.tar.gz scp://123456789:a1b2c3d4e5@cxd.cisco.comProtokolle löschen
Löschen Sie alle Protokolldateien auf dem Gerät mit der Menüoption r: Clear Logs. Dadurch werden alle vorhandenen Protokolle gelöscht, mit Ausnahme der neuesten Protokolle des TCL-Skripts und der Konnektoren.
Cloud Connector-Einstellungen anzeigen und ändern
Nehmen Sie mithilfe der Menüoption v: View and Modify Cloud Connector Settings die folgenden Änderungen an den bestehenden Einstellungen eines Cloud-Connectors vor.
===============================================================
Webex Managed Gateway Connector
===============================================================
Script Version : 2.0.2
Hostname/IP Addr : 10.65.125.188
DNS Server(s) : 10.64.86.70
Gateway Username : lab
External Interface : GigabitEthernet1
Proxy Hostname/IP Addr : proxy-wsa.esl.cisco.com:80
===============================================================
Options
c : Update Gateway Credentials
e : Update External Interface
p : Update Proxy Details
n : Update DNS Server
k : Update Connector Package Verification Key
l : Modify log level for Cloud Connector
h : Go to home menu
q : Quit
===============================================================
Select an option from the menu: cGateway-Anmeldeinformationen aktualisieren
Aktualisieren Sie den Benutzernamen und das Passwort des Gateways über die Menüoption c: Update Gateway
Credentials.
Externe Schnittstelle aktualisieren
Ändern Sie die Schnittstelle, an die der Konnektor gebunden ist, und die IP-Adresse des Konnektors mithilfe der Menüoption v: View and Modify Cloud Connector Settings.
Proxy-Details aktualisieren
Folgende Aufgaben können Sie über die Menüoption p: Update Proxy
Details ausführen:
-
i: Update Proxy IP and Port -
c: Update Proxy Credentials -
r: Remove Proxy Credentials -
a: Remove All Proxy Details -
h: Go to home menu
Verifizierungsschlüssel für das Aktualisierungs-Connector-Paket
Im Falle eines technischen Problems und falls der Support-Techniker Sie auffordert, Ihren Paketverifizierungsschlüssel zu ersetzen, laden Sie die neue gateway-webex-connectors.gpg Datei in bootflash:/gateway_connector/ hoch und verwenden Sie die Menüoption k: Update
Connector Package Verification Key zur Verifizierung.
Ändern Sie den Protokollierungsgrad für den Management Connector.
Ändern Sie den Protokollierungsgrad für den Konnektor über die Menüoption l: Modify log level for
Cloud Connector und wählen Sie dann eine der folgenden Optionen aus:
=====================================
Number Log Level
=====================================
1 DEBUG
2 INFO
3 WARNING
4 ERROR
5 CRITICAL
======================================
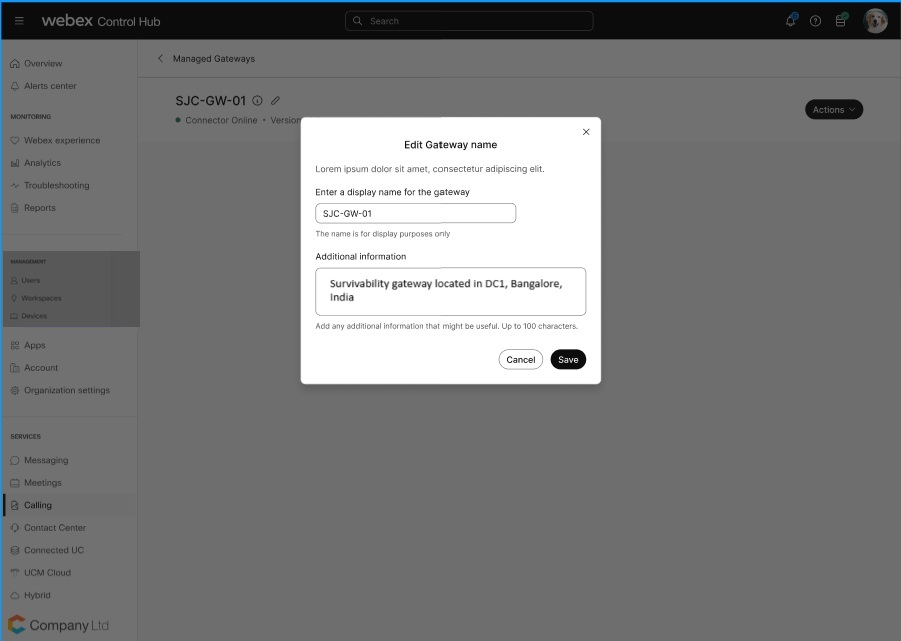
Verwalten Sie Ihre Gateway-Instanz im Control Hub.
So verwalten Sie Ihre Gateway-Instanz:
Verbindung anhalten oder fortsetzen
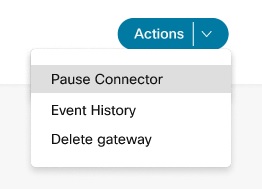
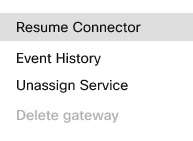
Der Pause Connector weist den Management Connector an, den Telemetrie-Connector zu stoppen. Sie können diese Option nutzen, um die Telemetrieverbindung vorübergehend zu unterbrechen, während Sie etwaige Probleme mit einem Gateway beheben. Wenn Sie den Connector pausieren, funktionieren Dienste wie die Konfigurationsvalidierung nicht. Verwenden Sie die Aktion Resume Connector, um den Telemetrie-Connector neu zu starten.
| 1 |
Wählen Sie im Menü Aktionen die Option Connector pausieren, um Ihren Management Connector anzuhalten. |
| 2 |
Um die unterbrochene Verbindung fortzusetzen, klicken Sie im Menü Aktionen auf Verbindung fortsetzen. |
Ereignisverlauf
Der Control Hub zeichnet den Ereignisverlauf Ihrer verwalteten Gateways auf und zeigt ihn an. Sehen Sie sich die Details eines einzelnen Gateways oder die konsolidierten Details aller Ihrer verwalteten Gateways an.
| 1 |
Klicken Sie auf der Seite Aufruf auf Ereignisverlauf, um die Ereignisdetails aller Ihrer verwalteten Gateways anzuzeigen. |
| 2 |
Für ereignisspezifische Details zu einem Gateway klicken Sie im Menü [ Aktionen für dieses Gateway auf Ereignisverlauf. |
Gateway löschen
| 1 |
Klicken Sie im Menü Aktionen auf Gateway löschen, um eine beliebige Gateway-Instanz zu löschen. |
| 2 |
Klicken Sie auf Bestätigen. 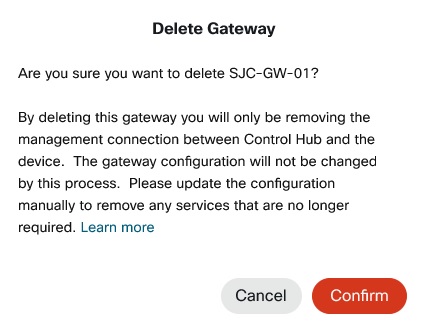 Eine Gateway-Instanz mit zugewiesenen Diensten kann nicht gelöscht werden. Zuerst die Dienste heben. |
Wohin als Nächstes?
Nach der Registrierung des Gateways können Sie die Konfiguration unter Dienste verwalteten Gateways zuweisenfortsetzen.

 und wählen Sie die entsprechende Aktion aus.
und wählen Sie die entsprechende Aktion aus.