- Strona główna
- /
- Artykuł






Przeżywalność witryny dla Webex Calling
 W tym artykule
W tym artykule Opinia?
Opinia?Dzięki funkcji Site Survivability możesz mieć pewność, że Twoja firma pozostanie dostępna, nawet jeśli połączenie z Webex zostanie utracone. Wykorzystuje lokalną bramę sieciową w celu zapewnienia awaryjnych usług połączeń do punktów końcowych na miejscu w przypadku przerw w działaniu sieci.
Rozważania dotyczące wdrożenia
Domyślnie punkty końcowe usługi Webex Calling działają w trybie aktywnym, łącząc się z chmurą Webex w celu rejestracji SIP i kontroli połączeń. Jeśli połączenie sieciowe z Webex zostanie utracone, punkty końcowe automatycznie przełączą się w tryb przetrwania i zarejestrują się w lokalnej bramce Survivability Gateway. W tym trybie brama zapewnia podstawowe usługi połączeń zapasowych. Po przywróceniu połączenia sieciowego z Webex, kontrola połączeń i rejestracja zostaną przełączone z powrotem do chmury Webex.
W trybie przetrwania obsługiwane są następujące połączenia:
-
Połączenia wewnętrzne (wewnątrz lokalizacji) między obsługiwanymi punktami końcowymi usługi Webex Calling
-
Połączenia zewnętrzne (przychodzące i wychodzące) z wykorzystaniem lokalnego łącza PSTN lub łącza SIP do numerów zewnętrznych i dostawców E911
Aby skorzystać z tej funkcji, należy skonfigurować router Cisco IOS XE w sieci lokalnej jako bramę Survivability Gateway. Survivability Gateway codziennie synchronizuje informacje o połączeniach z chmury Webex dla punktów końcowych w danej lokalizacji. Jeśli punkty końcowe przełączą się w tryb przetrwania, brama może wykorzystać tę informację do przejęcia rejestracji SIP i świadczenia podstawowych usług połączeń.
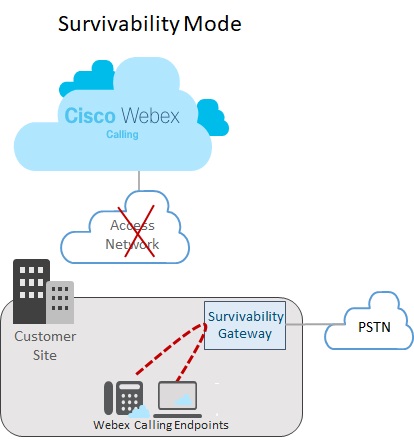
Konfiguracja pojedynczej lokalizacji
Poniższy rysunek przedstawia scenariusz awarii sieci, w którym połączenie z Webex zostaje zerwane, a punkty końcowe w witrynie Webex działają w trybie przetrwania. Na ilustracji widać, że Survivability Gateway kieruje wewnętrznym połączeniem między dwoma lokalnymi punktami końcowymi bez konieczności połączenia z Webex. W tym przypadku bramka Survivability Gateway jest skonfigurowana przy użyciu lokalnego połączenia PSTN. Dzięki temu punkty końcowe na miejscu w trybie przetrwania mogą używać sieci PSTN do połączeń przychodzących i wychodzących na numery zewnętrzne i do dostawców E911.
Konfiguracja wielu lokalizacji
Poniższy rysunek przedstawia scenariusz awarii sieci, w którym połączenie z Webex zostaje zerwane, a punkty końcowe zlokalizowane w różnych lokalizacjach działają w trybie przetrwania. W sieci LAN znajduje się wiele mniejszych lokalizacji, które są mapowane na jedną bramę Survivability. Wdrożenie to optymalizuje wykorzystanie zasobów bramy, jednocześnie zachowując konfiguracje specyficzne dla danej lokalizacji w zakresie kierowania połączeń.
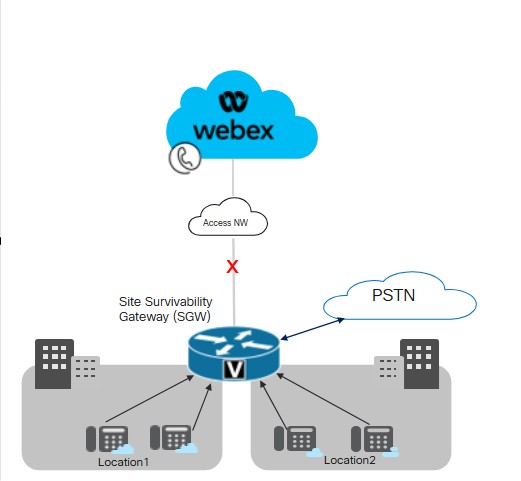
Firma Cisco zaleca utrzymanie opóźnienia na poziomie 50 milisekund w celu zapewnienia łączności między bramką Survivability Gateway a punktami końcowymi w różnych lokalizacjach w sieci LAN.
Kluczowe warunki przetrwania miejsca
W przypadku Survivability Gateway obowiązują następujące warunki:
-
Chmura Webex uwzględnia adres IP, nazwę hosta i port Survivability Gateway w pliku konfiguracyjnym urządzenia. Dzięki temu punkty końcowe mogą nawiązać kontakt z Survivability Gateway w celu rejestracji, jeśli połączenie z Webex zostanie zerwane.
-
Codzienna synchronizacja danych połączeń między chmurą Webex a Survivability Gateway obejmuje informacje uwierzytelniające dla zarejestrowanych użytkowników. Dzięki temu punkty końcowe mogą utrzymywać bezpieczne rejestracje nawet podczas działania w trybie przetrwania. Synchronizacja obejmuje również informacje o trasach dla tych użytkowników.
-
Brama Survivability Gateway może automatycznie kierować połączenia wewnętrzne, korzystając z informacji o routingu udostępnianych przez Webex. Dodaj konfigurację łącza PSTN do Survivability Gateway, aby umożliwić wykonywanie połączeń zewnętrznych.
-
Każda witryna wdrażająca usługę Site Survivability wymaga bramy Survivability w sieci lokalnej.
-
Rejestracje i kontrola połączeń zostaną przeniesione do chmury Webex po przywróceniu połączenia sieciowego Webex na co najmniej 30 sekund.
Kolokacja z Unified SRST
Survivability Gateway obsługuje kolokację konfiguracji Webex Survivability i konfiguracji Unified SRST na tej samej bramie. Brama może zapewnić przetrwanie zarówno dla punktów końcowych Webex Calling, jak i dla punktów końcowych rejestrujących się w Unified Communications Manager. Aby skonfigurować kolokację:
-
Skonfiguruj obsługę Unified SRST dla punktów końcowych rejestrujących się w Unified Communications Manager. Aby zapoznać się z konfiguracją, zobacz Cisco Unified SRST Administration Guide.
-
Na tej samej bramie wykonaj czynności opisane w Przepływie zadań konfiguracji funkcji Site Survivability w tym artykule, aby skonfigurować bramę z funkcją Site Survivability dla punktów końcowych usługi Webex Calling.
Rozważania dotyczące trasowania połączeń w przypadku kolokacji
Konfigurując routing połączeń w scenariuszach kolokacji, należy wziąć pod uwagę następujące kwestie:
-
Brama Survivability automatycznie kieruje połączenia wewnętrzne pod warunkiem, że oba punkty końcowe w połączeniu są zarejestrowane w Bramie Survivability. Połączenia wewnętrzne są automatycznie przekierowywane między dowolnymi zarejestrowanymi klientami (SRST lub Webex Calling).
-
Może wystąpić sytuacja, w której połączenie z jednym systemem sterowania połączeniami zostanie zerwane, a połączenie z drugim systemem pozostanie aktywne. W rezultacie jeden zestaw punktów końcowych rejestruje się w Survivability Gateway, podczas gdy inny zestaw punktów końcowych w tej samej lokalizacji rejestruje się w głównym kontrolerze połączeń. W takim przypadku może zaistnieć konieczność skierowania połączeń między dwoma zestawami punktów końcowych do łącza SIP lub obwodu PSTN.
-
Połączenia zewnętrzne i połączenia E911 mogą być kierowane do łącza SIP lub obwodu PSTN.
Obsługiwane funkcje i komponenty
W poniższej tabeli znajdują się informacje na temat obsługiwanych funkcji.
| Funkcja | Urządzenia MPP i aplikacja Webex | VG4xx ATA |
|---|---|---|
|
Połączenia wewnętrzne |
Obsługiwane automatycznie, bez konieczności specjalnej konfiguracji routingu w Survivability Gateway. |
Obsługiwane automatycznie, bez konieczności specjalnej konfiguracji routingu w Survivability Gateway. Numery alternatywne nie są obsługiwane. |
|
Połączenia między lokalizacjami i połączenia PSTN (przychodzące i wychodzące) |
Połączenia PSTN oparte na łączach telekomunikacyjnych lub łączu SIP. |
Połączenia PSTN oparte na łączach telekomunikacyjnych lub łączu SIP. |
|
Obsługa połączeń E911 |
Do wywołania E911 wymagany jest obwód PSTN lub łącze SIP. Połączenia wychodzące korzystają z określonego zarejestrowanego numeru ELIN (Emergency Location Identification Number) dla określonej lokalizacji reagowania kryzysowego (Emergency Response Location, ERL). Jeśli operator alarmowy oddzwoni na rozłączone połączenie, bramka Survivability Gateway przekieruje połączenie na ostatnie urządzenie, z którego dzwoniono na numer alarmowy. |
Do wywołania E911 wymagany jest obwód PSTN lub łącze SIP. Połączenia wychodzące korzystają z określonego zarejestrowanego numeru ELIN (Emergency Location Identification Number) dla określonej lokalizacji reagowania kryzysowego (Emergency Response Location, ERL). Jeśli operator alarmowy oddzwoni na rozłączone połączenie, bramka Survivability Gateway przekieruje połączenie na ostatnie urządzenie, z którego dzwoniono na numer alarmowy. |
|
Wstrzymanie i wznowienie połączenia |
Obsługiwane Jeśli korzystasz z funkcji Music on Hold (MOH), ręcznie skonfiguruj bramkę Survivability Gateway za pomocą pliku MOH. |
Linie analogowe VG4xx ATA nie umożliwiają wstrzymania ani wznowienia połączeń. Ta funkcja jest obsługiwana tylko wtedy, gdy połączenie przychodzące jest odbierane na VG4xx ATA. |
|
Przekierowanie połączeń z obsługą |
Obsługiwane |
Ta funkcja jest obsługiwana tylko wtedy, gdy połączenie przychodzące jest odbierane na VG4xx ATA. |
|
Przekierowanie połączeń w ciemno |
Obsługiwane |
Ta funkcja jest obsługiwana tylko wtedy, gdy połączenie przychodzące jest odbierane na VG4xx ATA. |
|
Identyfikator dzwoniącego przychodzącego (nazwa) |
Obsługiwane |
Obsługiwane |
|
Identyfikator dzwoniącego przychodzącego (nazwa & Numer) |
Obsługiwane |
Obsługiwane |
|
Połączenie wideo typu punkt-punkt |
Obsługiwane |
Nieobsługiwany |
|
Połączenia trójstronne |
Nieobsługiwany |
Nieobsługiwany |
|
Linie współdzielone |
Obsługiwane |
Obsługiwane |
|
Linie wirtualne |
Obsługiwane |
Nieobsługiwany |
|
Przekierowanie połączenia |
Obsługiwane przekierowywanie połączeń w stanach: zajęty, brak odpowiedzi i stan zajęty. |
Obsługiwane |
|
Grupa poszukiwania |
Obsługiwane dla następujących elementów: Sekwencyjny, równoległy, równorzędny i najdłuższy czas bezczynności. |
Obsługiwane |
|
Automatyczny asystent |
Obsługiwane dla wybierania numeru wewnętrznego |
Obsługiwane |
Po skonfigurowaniu tej funkcji funkcja Site Survivability będzie dostępna dla następujących obsługiwanych punktów końcowych.
| Typ | Modele | Minimalna wersja |
|---|---|---|
| Telefon IP Cisco z oprogramowaniem układowym Multiplatform (MPP) |
6821, 6841, 6851, 6861, 6861 Wi-Fi, 6871 7811, 7821, 7841, 7861 8811, 8841, 8851, 8861 8845 (tylko dźwięk), 8865 (tylko dźwięk), 8875 (wideo) 9800 Aby uzyskać więcej informacji na temat obsługiwanych telefonów IP Cisco z oprogramowaniem układowym Multiplatform (MPP), zobacz: |
12.0(1) Dla telefonów 8875 – Phone OS 3.2 i nowsze wersje Dla serii 9800 – PhoneOS 3.2(1) |
|
Telefon konferencyjny IP Cisco |
7832, 8832 |
12.0(1) |
|
Aplikacja Cisco Webex |
Windows, Mac |
43.2 |
|
Punkty końcowe analogowe |
VG400 ATA, VG410 ATA i VG420 ATA Cisco ATA 191 i 192 |
17.16.1a 11.3(1) dla ATA 191 i 192 |
Survivability Gateway nie obsługuje urządzeń innych firm.
Poniższa tabela pomoże Ci skonfigurować routery Cisco IOS XE jako bramę Survivability Gateway. W tej tabeli wymieniono maksymalną liczbę punktów końcowych obsługiwanych przez każdą platformę oraz minimalną wersję systemu IOS XE.
Funkcje Webex Calling Survivability Gateway są dostępne w systemie Cisco IOS XE Dublin w wersji 17.12.3 lub nowszych. Funkcje Hunt Group, przekierowywania połączeń i automatycznej obsługi są dostępne w systemie IOS od wersji 17.18.2.
| Model | Maksymalna liczba rejestracji punktów końcowych | Minimalna wersja |
|---|---|---|
|
Router usług zintegrowanych 4321 | 50 |
Cisco IOS XE Dublin 17.12.3 lub nowsze wersje |
|
Router usług zintegrowanych 4331 | 100 | |
|
Router usług zintegrowanych 4351 | 700 | |
|
Router usług zintegrowanych 4431 | 1200 | |
|
Router usług zintegrowanych 4451-X | 2000 | |
|
Router usług zintegrowanych 4461 | 2000 | |
|
Katalizator Edge 8200L-1N-4T | 1500 | |
|
Katalizator Edge 8200-1N-4T | 2500 | |
|
Katalizator Edge 8300-1N1S-6T | 2500 | |
|
Katalizator Edge 8300-2N2S-6T | 2500 | |
|
Katalizator Edge 8300-1N1S-4T2X | 2500 | |
|
Katalizator Edge 8300-2N2S-4T2X | 2500 | |
|
Mała konfiguracja oprogramowania Catalyst Edge 8000V | 500 | |
|
Konfiguracja nośnika oprogramowania Catalyst Edge 8000V | 1000 | |
|
Duża konfiguracja oprogramowania Catalyst Edge 8000V | 2000 |
Informacje referencyjne portu dla Survivability Gateway
|
Cel połączenia |
Adresy źródłowe |
Porty źródłowe |
Protokół |
Adresy docelowe |
Porty docelowe |
|---|---|---|---|---|---|
|
Sygnalizacja połączeń do bramy Survivability Gateway (SIP TLS) |
Urządzenia |
5060-5080 |
TLS |
Brama utrzymania |
8933 |
|
Zadzwoń do mediów na Survivability Gateway (SRTP) |
Urządzenia |
19560-19660 |
UDP |
Brama utrzymania |
8000-14198 (SRTP przez UDP) |
|
Sygnalizacja połączeń do bramki PSTN (SIP) |
Brama utrzymania |
Krótkotrwałe |
TCP lub UDP |
Twoja bramka PSTN ITSP |
5060 |
|
Wywołanie nośnika do bramy PSTN (SRTP) |
Brama utrzymania |
8000-48198 |
UDP |
Twoja bramka PSTN ITSP |
Krótkotrwałe |
|
Synchronizacja czasu (NTP) |
Brama utrzymania |
Krótkotrwałe |
UDP |
Serwer NTP |
123 |
|
Rozpoznawanie nazw (DNS) |
Brama utrzymania |
Krótkotrwałe |
UDP |
Serwer DNS |
53 |
|
Zarządzanie chmurą |
Łącznik |
Krótkotrwałe |
Protokół HTTPS |
Usługi Webex |
443, 8433 |
Aby uzyskać wskazówki dotyczące trybu chmury, zapoznaj się z artykułem pomocy Informacje dotyczące portów dla połączeń Webex.
Można dostosować wartości ustawień portu na routerach Cisco IOS XE. W tabeli zastosowano wartości domyślne w celu zapewnienia wskazówek.
Konfiguracja funkcji
Przebieg zadań konfiguracji przeżywalności witryny
Aby dodać funkcję Site Survivability do istniejącej lokalizacji usługi Webex Calling, wykonaj następujące zadania. Jeśli połączenie z chmurą Webex zostanie zerwane, brama Survivability Gateway w sieci lokalnej może zapewnić zapasową kontrolę połączeń dla punktów końcowych w danej lokalizacji.
Przed rozpoczęciem
Jeśli musisz skonfigurować nową bramę, która będzie pełnić funkcję bramy Survivability Gateway, zapoznaj się z artykułem Webex Rejestracja bram zarządzanych Cisco IOS w chmurze Webex, aby dodać bramę do Control Hub.
| Kroki | Polecenie lub działanie | Cel |
|---|---|---|
|
1 | Przypisz usługę przetrwania do bramy |
W Control Hub przypisz usługę Survivability Gateway do bramy. |
|
2 | Pobierz szablon konfiguracji |
Pobierz szablon konfiguracji z Control Hub. Szablon będzie potrzebny podczas konfiguracji wiersza poleceń bramy. |
|
3 |
Skonfiguruj licencje dla Survivability Gateway. | |
|
4 |
Skonfiguruj certyfikaty dla Survivability Gateway. | |
|
5 |
Użyj pobranego wcześniej szablonu konfiguracji jako przewodnika po konfiguracji wiersza poleceń bramy. Uzupełnij wszystkie obowiązkowe konfiguracje zawarte w szablonie. |
Przypisz usługę przetrwania do bramy
Przed rozpoczęciem
| 1 |
Przejdź do Połączenia w obszarze Usługi, a następnie kliknij kartę Bramy zarządzane. Widok Bramy zarządzane wyświetla listę bram, którymi zarządzasz za pomocą Control Hub.
|
| 2 |
Wybierz bramę, którą chcesz przypisać jako bramę przetrwania i wybierz jedną z następujących opcji, w zależności od wartości pola Usługa :
|
| 3 |
Z listy rozwijanej typu usługi wybierz Brama przetrwania i wypełnij następujące pola:
Po zakończeniu rejestracji szczegóły lokalizacji zostaną wyświetlone na stronie Bramy zarządzane. |
| 4 |
Kliknij Przypisz. Widok Bramy zarządzane wyświetla listę lokalizacji przypisanych do bramy.
|
Pobierz szablon konfiguracji
| 1 |
Zaloguj się do centrum sterowania. Jeśli jesteś organizacją partnerską, uruchomi się Partner Hub. Aby otworzyć Control Hub, kliknij widok Klient w Partner Hub i wybierz odpowiedniego klienta lub wybierz Moja organizacja, aby otworzyć ustawienia Control Hub dla organizacji partnerskiej. |
| 2 |
Przejdź do . |
| 3 |
Kliknij odpowiednią Bramkę Przetrwania. |
| 4 |
Kliknij Pobierz szablon konfiguracji i pobierz szablon na swój komputer stacjonarny lub laptop. |
Konfiguruj licencjonowanie
| 1 |
Wejdź w tryb konfiguracji globalnej na routerze: |
| 2 |
Skonfiguruj licencje za pomocą poleceń, które dotyczą wyłącznie konkretnej platformy.
W przypadku konfigurowania przepustowości większej niż 250 Mbp wymagana jest licencja platformy HSEC. |
Konfiguruj certyfikaty
Konfigurowanie certyfikatów w systemie Cisco IOS XE
Aby poprosić o certyfikaty dla Survivability Gateway i je utworzyć, wykonaj następujące kroki. Używaj certyfikatów podpisanych przez publicznie znany Urząd Certyfikacji.
Platforma Survivability Gateway obsługuje wyłącznie publicznie znane certyfikaty CA. Prywatnych lub korporacyjnych certyfikatów CA nie można używać w przypadku Survivability Gateway.
Aby uzyskać listę głównych urzędów certyfikacji obsługiwanych w ramach usługi Webex Calling, zobacz Jakie główne urzędy certyfikacji są obsługiwane w przypadku połączeń z platformami audio i wideo Cisco Webex?.
Platforma Survivability Gateway nie obsługuje certyfikatu wieloznacznego.
Aby ukończyć kroki, uruchom polecenia z przykładowego kodu. Aby uzyskać dodatkowe informacje na temat tych poleceń, wraz z dodatkowymi opcjami konfiguracji, zapoznaj się z rozdziałem „ Obsługa protokołu SIP TLS” w podręczniku Cisco Unified Border Element Configuration Guide.
| 1 |
Aby przejść do trybu konfiguracji globalnej, uruchom następujące polecenia: |
| 2 |
Wygeneruj klucz prywatny RSA, uruchamiając następujące polecenie. Moduł klucza prywatnego musi mieć co najmniej 2048 bitów. |
| 3 |
Skonfiguruj punkt zaufania, w którym będzie przechowywany certyfikat Survivability Gateway. W pełni kwalifikowana nazwa domeny (FQDN) bramy musi używać tej samej wartości, której użyłeś podczas przypisywania bramie usługi przetrwania. |
| 4 |
Wygeneruj żądanie podpisania certyfikatu, uruchamiając polecenie Gdy pojawi się monit, wpisz Po wyświetleniu żądania CSR na ekranie użyj Notatnika, aby skopiować certyfikat do pliku, który możesz wysłać do obsługiwanego urzędu certyfikacji (CA). Jeśli dostawca podpisu certyfikatu wymaga CSR w formacie PEM (Privacy Enhanced Mail), przed wysłaniem należy dodać nagłówek i stopkę. Na przykład: |
| 5 |
Po wydaniu certyfikatu przez urząd certyfikacji należy uruchomić polecenie Gdy pojawi się monit, wklej bazę 64 CER/PEM wydawanie zawartości certyfikatu CA (nie certyfikatu urządzenia) w terminalu. |
| 6 |
Zaimportuj podpisany certyfikat hosta do punktu zaufania, używając polecenia Gdy pojawi się monit, wklej bazę 64 CER/PEM certyfikat do terminala. |
| 7 |
Sprawdź, czy certyfikat głównego urzędu certyfikacji jest dostępny: Rozwiązanie Webex Calling obsługuje wyłącznie publicznie znane urzędy certyfikacji. Prywatne i korporacyjne certyfikaty CA nie są obsługiwane. |
| 8 |
Jeśli certyfikat głównego urzędu certyfikacji nie jest dołączony do pakietu, zdobądź certyfikat i zaimportuj go do nowego punktu zaufania. Wykonaj ten krok, jeśli publicznie znany certyfikat główny urzędu certyfikacji nie jest dostępny dla Twojej bramy Cisco IOS XE. Gdy pojawi się monit, wklej bazę 64 CER/PEM zawartość certyfikatu do terminala. |
| 9 |
Używając trybu konfiguracji, określ domyślny punkt zaufania, wersję TLS i domyślne ustawienia SIP-UA za pomocą następujących poleceń. |
Importuj certyfikaty wraz z parami kluczy
Certyfikaty CA i pary kluczy można importować jako pakiet w formacie PKCS12 (.pfx lub .p12). Możesz zaimportować pakiet z lokalnego systemu plików lub zdalnego serwera. PKCS12 to specjalny typ formatu certyfikatu. Łączy w sobie cały łańcuch certyfikatów, od certyfikatu głównego, poprzez certyfikat tożsamości, wraz z parą kluczy RSA. Oznacza to, że importowany pakiet PKCS12 będzie zawierał parę kluczy, certyfikaty hosta i certyfikaty pośrednie. Zaimportuj pakiet PKCS12 dla następujących scenariuszy:
-
Eksportuj z innego routera Cisco IOS XE i importuj do routera Survivability Gateway
-
Generowanie pakietu PKCS12 poza routerem Cisco IOS XE przy użyciu OpenSSL
Aby utworzyć, wyeksportować i zaimportować certyfikaty oraz pary kluczy dla routera Survivability Gateway, wykonaj następujące czynności.
| 1 |
(Opcjonalnie) Wyeksportuj pakiet PKCS12 wymagany dla routera Survivability Gateway. Ten krok ma zastosowanie tylko w przypadku eksportowania z innego routera Cisco IOS XE. |
| 2 |
(Opcjonalnie) Utwórz pakiet PKCS12 przy użyciu OpenSSL. Ten krok ma zastosowanie tylko wtedy, gdy pakiet PKCS12 jest generowany poza systemem Cisco IOS XE przy użyciu OpenSSL. |
| 3 |
Zaimportuj pakiet plików w formacie PKCS12. Poniżej przedstawiono przykładową konfigurację polecenia i szczegóły dotyczące konfigurowalnych parametrów:
Polecenie crypto pki import automatycznie tworzy punkt zaufania, aby pomieścić certyfikat. |
| 4 |
Używając trybu konfiguracji, określ domyślny punkt zaufania, wersję TLS i domyślne ustawienia SIP-UA za pomocą następujących poleceń. |
Skonfiguruj bramę Survivability
Skonfiguruj bramę jako bramę przetrwania
Użyj pobranego wcześniej szablonu konfiguracji jako przewodnika po konfiguracji wiersza poleceń bramy. Uzupełnij obowiązkowe konfiguracje w szablonie.
Poniższe kroki zawierają przykładowe polecenia wraz z objaśnieniami. Edytuj ustawienia, aby dopasować je do wdrożenia. Kątowe nawiasy (na przykład ) wskazują ustawienia, w których należy wprowadzić wartości mające zastosowanie do wdrożenia. Różne ustawienia <tag> wykorzystują wartości liczbowe do identyfikacji i przypisywania zestawów konfiguracji.
- O ile nie zaznaczono inaczej, to rozwiązanie wymaga wykonania wszystkich konfiguracji opisanych w tej procedurze.
- Podczas stosowania ustawień z szablonu zastąp
%tokens%preferowanymi wartościami przed skopiowaniem do bramki. - Aby uzyskać więcej informacji na temat poleceń, zobacz Dokumentacja poleceń Webex Managed Gateway. Skorzystaj z tego przewodnika, chyba że opis polecenia odsyła do innego dokumentu.
| 1 |
Przejdź do trybu konfiguracji globalnej. Gdzie:
|
| 2 |
Wykonaj konfigurację usługi głosowej:
Wyjaśnienie poleceń:
|
| 3 |
Włącz funkcję przetrwania na routerze: Wyjaśnienie poleceń:
|
| 4 |
Skonfiguruj serwery NTP:
|
| 5 |
(Fakultatywny). Skonfiguruj ogólne uprawnienia wywołania klasy ograniczeń: Powyższy przykład tworzy zestaw niestandardowych klas ograniczeń o nazwie kategorie (na przykład |
| 6 |
Skonfiguruj listę preferowanych kodeków. Na przykład na poniższej liście preferowanym kodekiem jest g711ulaw, a po nim g711alaw. Wyjaśnienie poleceń:
|
| 7 |
Skonfiguruj domyślne pule rejestrów głosowych: Wyjaśnienie poleceń:
|
| 8 |
Konfigurowanie połączeń alarmowych: Wyjaśnienie poleceń:
Jeśli nakładka Wi-Fi nie jest dokładnie dopasowana do podsieci IP, wówczas połączenia alarmowe dla urządzeń nomadycznych mogą nie mieć prawidłowego mapowania ELIN. |
| 9 |
Skonfiguruj równorzędnych użytkowników dla sieci PSTN. Przykład konfiguracji połączenia równorzędnego można znaleźć w Przykłady połączeń PSTN. |
| 10 |
Opcjonalnie Włącz Muzykę oczekiwania na routerze. Musisz zapisać plik muzyczny w pamięci flash routera w formacie G.711. Plik może być w formacie .au lub .wav, ale format pliku musi zawierać dane 8-bitowe o częstotliwości 8 kHz (na przykład format danych ITU-T A-law lub mu-law). Wyjaśnienie poleceń:
|
Pełna synchronizacja na żądanie
Opcjonalnie Wykonaj tę procedurę tylko wtedy, gdy chcesz wykonać natychmiastową synchronizację na żądanie. Ta procedura nie jest obowiązkowa, ponieważ chmura Webex automatycznie synchronizuje dane połączeń z Survivability Gateway raz dziennie.
| 1 |
Zaloguj się do centrum sterowania. Jeśli jesteś organizacją partnerską, uruchomi się Partner Hub. Aby otworzyć Control Hub, kliknij widok Klient w Partner Hub i wybierz odpowiedniego klienta lub wybierz Moja organizacja, aby otworzyć ustawienia Control Hub dla organizacji partnerskiej. |
| 2 |
Przejdź do . |
| 3 |
Kliknij odpowiednią bramkę Survivability Gateway, aby otworzyć widok Usługa Survivability Service dla tej bramy. |
| 4 |
Kliknij przycisk Synchronizuj. |
| 5 |
Kliknij przycisk Przekaż. Synchronizacja może potrwać do 10 minut.
|
Edytuj właściwości bramy przetrwania
| 1 |
Zaloguj się do centrum sterowania. Jeśli jesteś organizacją partnerską, uruchomi się Partner Hub. Aby otworzyć Control Hub, kliknij widok Klient w Partner Hub i wybierz odpowiedniego klienta lub wybierz Moja organizacja, aby otworzyć ustawienia Control Hub dla organizacji partnerskiej. |
| 2 |
Przejdź do . |
| 3 |
Kliknij odpowiednią bramkę Survivability Gateway, aby otworzyć widok Usługa Survivability Service dla tej bramy. |
| 4 |
Kliknij przycisk Edytuj i zaktualizuj ustawienia następujących elementów.
|
| 5 |
Kliknij przycisk Przekaż. Aby usunąć bramkę Survivability Gateway z Control Hub, najpierw anuluj przypisanie usługi Survivability Gateway. Aby uzyskać więcej szczegółów, zobacz Przypisywanie usług do bram zarządzanych. |
Konfiguracje umożliwiające CDR-y na bramce zapewniającej przeżywalność
Łącznik automatycznie konfiguruje polecenia związane z CDR, aby ułatwić zbieranie danych o liczbie połączeń.
Pod koniec zdarzenia umożliwiającego przeżycie łącznik przetwarza rekordy połączeń (CDR) wygenerowane w czasie trwania zdarzenia, wraz z danymi konfiguracyjnymi, w celu zidentyfikowania różnych liczb wywołań. Metryki obejmują liczbę wszystkich połączeń, połączeń alarmowych i połączeń zewnętrznych i służą do monitorowania wykorzystania funkcji wewnętrznych. Do chmury Webex wysyłane są wyłącznie dane dotyczące liczby połączeń, rzeczywiste listy połączeń przychodzących nie są transmitowane.
Poniżej przedstawiono przykładową konfigurację:
!
gw-accounting file
primary ifs bootflash:guest-share/cdrs/
acct-template callhistory-detail
maximum cdrflush-timer 5
cdr-format detailed
!
Wyjaśnienie poleceń:
-
primary ifs bootflash:guest-share/cdrs/- To polecenie służy do przechowywania plików CDR w folderze guest-share, aby umożliwić dostęp do nich za pomocą łącznika. -
acct-template callhistory-detail- To polecenie jest wymagane, aby uwzględnić znacznik dial-peer w CDR. -
maximum cdrflush-timer 5- Domyślna wartość to 60 minut, ale ustawienie jej na 5 minut pozwala na szybsze rejestrowanie CDR w pliku. -
cdr-format detailed- To jest format domyślny. Kompaktowy format nie jest odpowiedni, ponieważ nie zawiera znacznika dial-peer.
Konfiguracje umożliwiające przekierowywanie połączeń
Funkcja przekierowywania połączeń jest częścią funkcji zapewniających ciągłą obsługę połączeń podczas przerw w sieci, gdy połączenie z chmurą Webex zostanie utracone. Brama Survivability pełni funkcję lokalnej bramy zapasowej, umożliwiając punktom końcowym lokalną rejestrację i utrzymanie podstawowych możliwości wywoływania.
-
Zachowaniem przekierowywania połączeń w trybie Survivability zarządza brama Survivability przy użyciu konfiguracji puli, konfiguracji dial-peer i zasad routingu, które obsługują połączenia lokalnie lub kierują je przez łącza PSTN lub SIP.
-
Bramka przetrwania tymczasowo wyłącza funkcje SIP REFER i SIP moved w celu zapewnienia dodatkowych usług przekazywania i transferu połączeń, ponieważ Webex Calling nie używa tych metod w trybie przetrwania.
Skonfiguruj pule rejestrów głosowych dla scenariuszy przekierowywania połączeń:
|
Aby skorzystać z funkcji przekierowywania połączeń, należy skonfigurować polecenie
|
Konfiguracje umożliwiające włączenie grupy polowań
Ta tabela przedstawia mapowanie konfiguracji funkcji grupy łowieckiej w Control Hub i przy użyciu poleceń bramy Survivability
| Funkcje grupy łowieckiej | Konfiguracja za pomocą Control Hub | Polecenia bramy przetrwania |
|---|---|---|
|
Wybierz wzorzec kierowania połączeń |
Top-Down/Simultaneous/Circular/Longest-idle | Sequential/Parallel/Peer/Longest-idle |
|
Dodaj grupę Hunt |
Dodaj grupę poszukiwawczą z nazwą i numerem telefonu dla każdej lokalizacji. | Aby dodać grupę łowiecką, użyj voice hunt-group . Następnie dodaj numer telefonu za pomocą polecenia pilot i nazwę grupy poszukiwawczej za pomocą polecenia description |
|
Wybierz użytkowników, obszary robocze lub linie wirtualne do dodania |
Wybierz agentów, którzy mają dołączyć do Hunt Group |
Skonfiguruj listę agentów za pomocą polecenia |
|
Przejdź po ustalonej liczbie dzwonków |
Konfiguruj za pomocą opcji Ustaw liczbę dzwonków |
Skonfiguruj za pomocą polecenia |
|
Przejdź, gdy zajęty |
Skonfiguruj za pomocą opcji Przesuń w razie zajętości |
Konfiguruj za pomocą polecenia |
|
Przekierowuj połączenia, gdy wszyscy agenci są nieosiągalni | Skonfiguruj za pomocą opcji Przekieruj połączenia, gdy wszyscy agenci są nieosiągalni |
Konfiguruj za pomocą polecenia |
|
Przekieruj połączenia, gdy wszyscy agenci są zajęci lub grupa poszukiwania jest zajęta |
Skonfiguruj za pomocą opcjiPrzekieruj połączenia, gdy wszyscy agenci są zajęci lub grupa przechwytująca jest zajęta |
Skonfiguruj za pomocą |
-
Skonfiguruj sekwencyjne pierścienie grupy Hunt
voice hunt-group 1 sequential pilot 1111 number 1 1001 number 2 1002 number 3 7089001 number 4 7089002 number 5 +1210903443 ..... ..... timeout 20 final 1009 statistics collect description present-call idle-phone -
Skonfiguruj równoległe pierścienie grupy Hunt
voice hunt-group 2 parallel pilot 2222 number 1 2001 number 2 2002 number 3 2089001 number 4 2089002 number 5 +12109034433 ..... ..... timeout 60 final 1009 statistics collect description
Opis poleceń:
-
voice hunt-group- To polecenie służy do definiowania i wprowadzania trybu konfiguracji grupy myśliwskiej. -
parallel- To słowo kluczowe określa metodę lub algorytm grupy poszukującej, którego system będzie używał do rozdzielania połączeń przychodzących pomiędzy członków tej grupy poszukującej. -
number- Tworzy listę extensions/e164 numbers/ESN którzy są członkami grupy polującej na głosy. Żaden numer na liście nie może być numerem pilotażowym innej grupy myśliwskiej. -
pilot- To jest główny numer lub numer katalogowy grupy poszukującej. Dzwoniący wybierają ten numer, aby połączyć się z grupą poszukiwawczą. -
timeout- Ustawia maksymalny czas (w sekundach), przez który grupa tropiąca będzie próbowała dzwonić do swoich członków przed podjęciem następnej akcji. -
final- To polecenie określa numer zapasowy. -
statistics collect- Umożliwia zbieranie statystyk operacyjnych dla grupy myśliwskiej. -
descriptin- opis grupy łowieckiej -
present-call idle-phone-Przedstawiaj połączenie tylko tym agentom, którzy są bezczynni.
Poniżej przedstawiono przykładowy wynik polecenia show voice hunt-group statistics. Wyniki obejmują bezpośrednie połączenia z numerem grupy wyszukiwania głosowego oraz połączenia z kolejki lub B-ACD.
Router# show voice hunt-group 1 statistics last 1 h
Wed 04:00 - 05:00
Max Agents: 3
Min Agents: 3
Total Calls: 9
Answered Calls: 7
Abandoned Calls: 2
Average Time to Answer (secs): 6
Longest Time to Answer (secs): 13
Average Time in Call (secs): 75
Longest Time in Call (secs): 161
Average Time before Abandon (secs): 8
Calls on Hold: 2
Average Time in Hold (secs): 16
Longest Time in Hold (secs): 21
Per agent statistics:
Agent: 5012
From Direct Call:
Total Calls Answered: 3
Average Time in Call (secs): 70
Longest Time in Call (secs): 150
Totals Calls on Hold: 1
Average Hold Time (secs): 21
Longest Hold Time (secs): 21
From Queue:
Total Calls Answered: 3
Average Time in Call (secs): 55
Longest Time in Call (secs): 78
Total Calls on Hold: 2
Average Hold Time (secs): 19
Longest Hold Time (secs): 26
Total Loged in Time (secs): 3000
Total Loged out Time (secs): 600
Agent: 5013
From Direct Call:
Total Calls Answered: 3
Average Time in Call (secs): 51
Longest Time in Call (secs): 118
Totals Calls on Hold: 1
Average Hold Time (secs): 11
Longest Hold Time (secs): 11
From Queue:
Total Calls Answered: 1
Average Time in Call (secs): 4
Longest Time in Call (secs): 4
Total Loged in Time (secs): 3000
Total Loged out Time (secs): 600
Agent: 5014
From Direct Call:
Total Calls Answered: 1
Average Time in Call (secs): 161
Longest Time in Call (secs): 161
From Queue:
Total Calls Answered: 1
Average Time in Call (secs): 658
Longest Time in Call (secs): 658
Total Loged in Time (secs): 3000
Total Loged out Time (secs): 600
Queue related statistics:
Total calls presented to the queue: 5
Calls handoff to IOS: 5
Number of calls in the queue: 0
Average time to handoff (secs): 2
Longest time to handoff (secs): 3
Number of abandoned calls: 0
Average time before abandon (secs): 0
Calls forwarded to voice mail: 0
Calls answered by voice mail: 0
Number of error calls: 0
Router# sh voice hunt-group
Group 1
type: sequential
pilot number: 4444, peer-tag 2147483647
list of numbers:
Member Used-by State Login/Logout
====== ======= ===== ============
1001 1001 up -
1003 1003 up -
preference: 0
preference (sec): 0
timeout: 15
final_number:
auto logout: no
stat collect: no
phone-display: no
hlog-block: no
calls in queue: 0
overwrite-dyn-stats: no
members logout: no
present-call idle-phone: no
webex-sgw-bgl14#
Konfiguracje umożliwiające podstawową automatyczną dystrybucję połączeń (B-ACD)
Podstawowa usługa automatycznej dystrybucji połączeń (B-ACD) i automatycznej sekretarki (AA) umożliwiają automatyczne odbieranie połączeń zewnętrznych z powitaniami i menu, które umożliwiają dzwoniącym wybór odpowiedniego działu lub wybieranie znanych numerów wewnętrznych.
B-ACD umożliwia automatyczne odbieranie i dystrybuowanie połączeń za pomocą interaktywnych menu i lokalnych grup poszukiwawczych. Aplikacja B-ACD składa się z usług automatycznej sekretarki (AA) i jednej usługi kolejkowania połączeń. Automatyczna sekretarka B-ACD obsługuje połączenia PSTN negocjowane z przychodzącym łączem SIP za pomocą kodeka g711ulaw
B-ACD obsługuje grupy wyszukiwania głosowego z sekwencyjnym, równoległym, równorzędnym, najdłuższym zalewem połączeń bezczynności, obsługą współdzielonych linii SIP i mieszanych linii współdzielonych.
W przypadku połączenia przychodzącego wybierany jest numer pilota B-ACD AA, po czym odtwarzany jest komunikat powitalny oraz instrukcje ułatwiające dzwoniącemu automatyczne przekierowanie połączenia.
Ograniczenia
Podczas przekazywania połączeń należy używać tego samego kodeka na połączeniach przychodzących i wychodzących. Używanie innych kodeków nie jest obsługiwane. System IOS nie będzie wywoływał transkodera dla połączeń obsługiwanych przez dowolną aplikację TCL.
Składniki B-ACD
Aplikacja B-ACD składa się z usługi kolejki połączeń i jednej lub więcej usług AA. Konfigurowalnymi komponentami tych usług są:
-
Numer pilota
-
Powitalny komunikat i inne pliki audio
-
Opcje menu
-
Wybierz przez numer wewnętrzny
Numer pilota
Każda usługa AA ma swój własny numer pilota AA, pod który dzwonią osoby dzwoniące, aby skontaktować się z AA. Liczba ta jest określona w poleceniu param aa-pilot. Numer pilota AA nie jest powiązany z żadnym numerem telefonu agenta ani numerem telefonu stacjonarnego, ale musisz zdefiniować numer równorzędny z numerem pilota AA jako numer do połączeń przychodzących, aby numer ten był dostępny dla osób dzwoniących z zewnątrz.
Komunikat powitalny i inne pliki audio
Komunikat powitalny to plik audio odtwarzany po odebraniu połączenia przez pilota. Ten plik audio jest jednym z wielu plików audio wykorzystywanych w usłudze B-ACD w celu informowania dzwoniących o ich statusie i ewentualnych działaniach. Możesz utworzyć spersonalizowane pliki audio opisujące opcje menu dostępne dla osób dzwoniących. Pliki audio B-ACD opisane są w poniższych sekcjach:
Ponowne nagrywanie domyślnych plików audio
Domyślne pliki audio są dostępne dla każdego punktu skryptu i przekazywane osobom dzwoniącym. Pobierasz domyślne pliki audio z łącza i kopiujesz je do miejsca, do którego ma dostęp router B-ACD, np. do pamięci flash lub serwera TFTP. Pliki audio i pliki skryptów są umieszczone na stronie internetowej w pliku tar. Domyślne pliki i ich komunikaty są wymienione w tabeli. Możesz nagrać ponownie spersonalizowane wiadomości w miejsce domyślnych, ale nie możesz zmienić nazw plików audio, z wyjątkiem sytuacji opisanych w Zmiana kodów językowych i nazw plików.
Aby ponownie nagrać i zainstalować domyślne komunikaty audio przed pierwszym użyciem usługi B-ACD, wykonaj czynności opisane w Pobieranie skryptów Tcl i komunikatów audio. Aby ponownie nagrać komunikaty audio w istniejącej usłudze B-ACD, wykonaj kroki opisane w Aktualizowanie parametrów skryptu i komunikatów audio (tylko wybieranie numeru wewnętrznego).
| Domyślna nazwa pliku | Domyślna zapowiedź | Długość domyślnego ogłoszenia |
|---|---|---|
en_bacd_welcome.au |
"Dziękuję za telefon." Zawiera dwusekundową pauzę po komunikacie. |
3 sekundy |
en_bacd_options_menu.au |
Aby rozpocząć sprzedaż, naciśnij 1 (pauza) Aby skontaktować się z obsługą klienta, naciśnij 2 (pauza) Aby wybrać numer wewnętrzny, naciśnij 3 (pauza) Aby porozmawiać z operatorem naciśnij zero. Zawiera czterosekundową pauzę po komunikacie. |
15seconds |
en_bacd_disconnect.au |
„Nie możemy w tej chwili odebrać Twojego połączenia. Spróbuj ponownie później. Dziękuję za telefon." Zawiera czterosekundową pauzę po komunikacie. |
10seconds |
en_bacd_invalidoption. au |
„Wprowadzono nieprawidłową opcję. Proszę spróbować ponownie.” Zawiera jednosekundową pauzę po komunikacie. Ten komunikat jest odtwarzany, gdy osoba dzwoniąca wybierze nieprawidłową opcję menu lub wybierze nieprawidłowy numer wewnętrzny. |
7seconds |
en_bacd_enter_dest.au |
„Proszę podać numer wewnętrzny, pod którym chcesz się połączyć.” Zawiera pięciosekundową pauzę po komunikacie. Ten komunikat jest odtwarzany, gdy osoba dzwoniąca wybierze opcję |
7seconds |
en_bacd_allagentsbusy. au |
Wszyscy agenci są obecnie zajęci pomaganiem innym klientom. Przytrzymaj, aby uzyskać pomoc. Wkrótce ktoś do ciebie dotrze. Zawiera dwusekundową pauzę po komunikacie. Ten komunikat jest również znany jako drugie powitanie. |
7seconds |
en_bacd_music_on_hol d.au |
Dzwoniącym korzystającym z funkcji B-ACD odtwarzana jest muzyka podczas oczekiwania (MOH). |
60seconds |
Jeśli zdecydujesz się na ponowne nagranie któregoś z plików audio, pamiętaj, że instrukcje B-ACD wymagają pliku audio w formacie G.711 (.au) z kodowaniem 8-bitowym, mu-law i 8 kHz. Polecamy następujące narzędzia audio lub inne o podobnej jakości:
-
Adobe Audition dla systemu Microsoft Windows firmy Adobe Systems Inc. (dawniej Cool Edit firmy Syntrillium Software Corp.)
-
AudioTool dla Solaris firmy Sun Microsystems Inc.
Skonfiguruj B-ACD
Oto kilka przykładów konfiguracji:
application
service aa bootflash:app-b-acd-aa-3.0.0.8.tcl
paramspace english index 1
param handoff-string aa
param dial-by-extension-option
paramspace english language en
param aa-pilot
paramspace english location flash:
param welcome-prompt _bacd_welcome.au
param voice-mail
param service-name queue
!
service queue bootflash:app-b-acd-3.0.0.8.tcl
param queue-len 30
param queue-manager-debugs 1
!
! SIP PSTN Dial-Peers for Auto Attendant(BACD) service called aa associated with incoming voice port
dial-peer voice 500 voip
description Inbound dial-peer for Auto Attendant
service aa
session protocol sipv2
incoming called-number
dtmf-relay rtp-nte
codec g711ulaw
no vad
!
! TDM PSTN Dial-Peers if not using SIP for Auto Attendant(BACD) service called aa associated with incoming voice pots
dial-peer voice 500 voip
description Inbound dial-peer for Auto Attendant
service aa
incoming called-number
port %tdm_port%
! | Polecenie | Wyjaśnienie |
|---|---|
param dial-by-extension-option |
Umożliwia dzwoniącym wybieranie numerów wewnętrznych po wybraniu określonego numeru menu. numer-menu—Identyfikator opcji menu. Zakres wynosi od 1 do 9. Nie ma wartości domyślnej. |
param aa-pilot |
Określa numer pilota powiązany z automatyczną sekretarką dial-peer |
param voice-mail |
Definiuje alternatywny adres docelowy dla połączeń, na które nie odpowiadają agenci AA |
paramspace english language en |
Definiuje kod języka plików audio używanych w dynamicznych komunikatach aplikacji IVR.
Kod języka musi odpowiadać dwuliterowemu prefiksowi języka używanemu w nazwach plików z komunikatami audio, niezależnie od języka faktycznie użytego w pliku. Aby uzyskać więcej informacji, zobacz Komunikat powitalny i inne pliki audio |
param welcome-prompt
audio-filename |
Przypisuje plik audio z powitaniem używanym przez tę usługę AA.
|
Zmiana kodów językowych i nazw plików
-
Prefiks dowolnej nazwy pliku można zmienić na ch, en, sp lub aa. Prefiks musi odpowiadać kodowi określonemu w parametrze language-code w poleceniu paramspace language, niezależnie od faktycznego języka użytego w pliku.
-
Po prefiksie nazwa pliku komunikatu powitalnego (domyślnie en_bacd_welcome.au) może mieć dowolną nazwę identyfikującą, zdefiniowaną w poleceniu
param welcome-prompt. -
Po prefiksie nazwa pliku monitu rozwijalnego (nie podano nazwy domyślnej) może mieć dowolną nazwę identyfikującą, zdefiniowaną w poleceniu
param drop-through-prompt.
W plikach audio możesz nagrać podpowiedź w dowolnym języku. Nie ma potrzeby zmiany prefiksu pliku zawierającego monit w innym języku, ponieważ prefiksy kodów języków są używane w przypadku funkcji, które nie są częścią usługi B-ACD. Ważne jest jednak, aby prefiksy kodów języka dla plików odpowiadały kodowi języka określonemu w parametrze language-code w poleceniu paramspace language, niezależnie od języka faktycznie użytego w pliku audio.
Nie należy zmieniać części identyfikatora w nazwie pliku audio, z wyjątkiem pliku _bacd_welcome.au. Skrypty identyfikują pliki audio, które mają takie same nazwy identyfikacyjne jak te w Tabeli i mają ten sam prefiks, który określono w poleceniu języka paramspace.
Dwoma wyjątkami od ogólnych zasad nazewnictwa plików są plik audio komunikatu powitalnego (domyślnie en_bacd_welcome.au) i plik audio komunikatu drop-through-option (nie określono domyślnego nazewnictwa). Części identyfikacyjne nazw plików tych dwóch komunikatów dźwiękowych są określane jawnie podczas konfiguracji i mogą być w pełni konfigurowalne przez użytkownika. Pliki te mogą używać dowolnych nazw, pod warunkiem, że będą one zgodne z następującymi konwencjami:
-
Część prefiksu nazwy pliku musi być taka sama, jak kod języka określony w poleceniu paramspace language. Na przykład en.
-
Część identyfikatora nazwy pliku musi zaczynać się od znaku podkreślenia. Na przykład,
_welcome_to_xyz.au.
Korzystanie z plików audio do opisywania opcji menu
Domyślnie dostarczane są dwa pliki audio, które mają na celu wstępne zorientowanie dzwoniącego i udzielenie mu wskazówek dotyczących dostępnych opcji menu: en_welcome_prompt.au I en_bacd_options_menu.au. Można ponownie nagrać dostosowane wiadomości zamiast domyślnych wiadomości dostarczonych w tych plikach, jak wyjaśniono w Tabeli.
Jeśli usługa B-ACD korzysta z pojedynczej usługi AA, zapisz powitanie w en_welcome_prompt.au i zapisz instrukcje dotyczące wyboru menu w en_bacd_options_menu.au.
Jeśli Twoja usługa B-ACD korzysta z wielu usług AA, będziesz potrzebować osobnych powitań i instrukcji dla każdej usługi AA, korzystając z następujących wytycznych:
-
Nagraj osobne powitanie dla każdego nabożeństwa AA, używając innej nazwy dla pliku audio dla każdego powitania. Na przykład:
en_welcome_aa1.auIen_welcome_aa2.au. Powitalne komunikaty, które zapiszesz w tych plikach, muszą zawierać zarówno powitanie, jak i instrukcje dotyczące opcji menu. -
Nagraj ciszę w pliku audio
en_bacd_options_menu.au. Należy zachować co najmniej jedną sekundę ciszy. Należy pamiętać, że plik ten nie zawiera instrukcji menu w przypadku istnienia wielu usług AA.
Opcje menu
Usługa B-ACD ma na celu automatyczne kierowanie połączeń do właściwego miejsca docelowego w Twojej organizacji. Interaktywne usługi AA umożliwiają udostępnianie osobom dzwoniącym opcji menu, dzięki którym mogą podejmować właściwe decyzje podczas połączeń. Rodzaje opcji menu dostępnych w B-ACD opisano w tabeli. Opcje menu są ogłaszane dzwoniącym za pomocą komunikatów dźwiękowych, które opisano w Komunikat powitalny i inne pliki dźwiękowe.
| Typ | Opis | Wymagania | Przykład |
|---|---|---|---|
Dial-by-extension |
Osoba dzwoniąca wybiera cyfrę, aby móc wybrać znany numer wewnętrzny. Numer menu używany dla tej opcji nie może być taki sam, jak numer menu (aa-hunt) używany w usłudze kolejki połączeń. |
Brak wymagań. |
Po usłyszeniu wyboru opcji z menu, dzwoniący wybiera cyfrę 4 i może wybrać wewnętrzny numer telefonu. |
Opcja wybierania numeru wewnętrznego
Usługa B-ACD może również oferować opcję wybierania numeru wewnętrznego, która umożliwia dzwoniącym wybieranie wewnętrznych numerów wewnętrznych, jeśli znają już numer wewnętrzny. Opcja wybierania numeru wewnętrznego jest wyświetlana jako opcja menu.
Opcję wybierania numeru wewnętrznego konfiguruje się, określając numer opcji menu dla parametru wybierania numeru wewnętrznego. Po użyciu poniższego polecenia dzwoniący mogą wybrać cyfrę 1, a następnie numer wewnętrzny.
param dial-by-extension-option 1 W ramach usługi kolejki połączeń B-ACD numer opcji wybierania według numeru wewnętrznego i numery opcji grupy poszukiwań muszą się wzajemnie wykluczać. To ograniczenie oznacza, że numer opcji używany w przypadku opcji wybierania numeru wewnętrznego nie może być taki sam, jak żaden z numerów opcji używanych w przypadku opcji aa-hunt. Na przykład, jeśli użyjesz od aa-hunt1 do aa-hunt5 w celu określenia grup polowania w konfiguracji usługi kolejki połączeń, możesz użyć opcji 6 dla opcji wybierania numeru wewnętrznego, ale nie żadnej z liczb od 1 do 5.
Jeżeli wszystkie dziesięć numerów aa-hunt zostanie wykorzystanych w grupach poszukiwań w usłudze kolejkowania połączeń, nie będzie możliwości skorzystania z opcji wybierania numeru wewnętrznego. Należy pamiętać, że ograniczenie to dotyczy wszystkich numerów opcji (numerów AA-hunt) używanych w usłudze kolejkowania połączeń, a nie numerów opcji używanych w aplikacji AA.
Pobieranie skryptów Tcl i komunikatów audio
Wykonaj poniższe kroki, aby przygotować pliki skryptów i pliki monitów niezbędne dla usługi B-ACD.
-
Skopiuj plik tar do flasha rozruchowego routera SGW
Rozpakuj pliki tcl i audio za pomocą polecenia:
archive tar /xtract bootflash:cme-b-acd-3.0.0.8.tar bootflash:- Jeżeli to konieczne, nagraj pliki audio ponownie.
Wyjaśnienie poleceń:
| Polecenie | Wyjaśnienie |
|---|---|
|
Pobierz plik tar B-ACD |
Pobierz plik tar B-ACD o nazwie Ten plik tar zawiera skrypt AA Tcl, skrypt kolejki połączeń Tcl i domyślne pliki audio potrzebne do usługi B-ACD |
enable |
Włącza tryb uprzywilejowanego EXEC na routerze SGW. Jeśli zostaniesz o to poproszony, wpisz hasło. |
archivetar/xtract flash: |
Rozpakowuje pliki w archiwum B-ACD i kopiuje je do pamięci flash. W pliku
|
|
W razie potrzeby nagraj | Nagraj ponownie pliki audio ze swoimi niestandardowymi wiadomościami, ale nie zmieniaj nazw plików audio. |
Przykłady
Poniższy przykład wyodrębnia pliki z archiwum o nazwie cme-b-acd-2.1.0.0 na serwerze pod adresem 192.168.1.1 i kopiuje je do pamięci flash routera B-ACD.
archive tar /xtract tftp://192.168.1.1/cme-b-acd-2.1.0.0.tar flash:Aktualizowanie parametrów skryptu i komunikatów audio (tylko wybieranie numeru wewnętrznego)
Parametry skryptu B-ACD można aktualizować, wprowadzając zmiany w konfiguracji Cisco IOS. Aby zmiany parametrów zostały zastosowane, musisz zatrzymać i ponownie załadować skrypty B-ACD, w których wprowadziłeś zmiany. Jeśli ponownie nagrywasz komunikaty audio, musisz ponownie wczytać pliki komunikatów audio, które uległy zmianie.
-
Określ identyfikatory sesji wszystkich aktywnych sesji-
Użyj polecenia
showcall application sessionsw trybie uprzywilejowanym EXEC, aby uzyskać numery identyfikatorów sesji (SID) usług AA i kolejki połączeń. Jeśli sesja AA nie ma aktywnych połączeń, nazwa skryptu AA nie jest wyświetlana w wynikach poleceniashow call application sessions. - W razie potrzeby zatrzymaj sesje usługi AA i kolejki połączeń B-ACD — korzystając z numerów identyfikacyjnych sesji z kroku 1, zatrzymaj sesje usługi AA i kolejki połączeń B-ACD. Użyj polecenia
call application session stopw trybie uprzywilejowanym EXEC, aby zatrzymać sesje AA i kolejki połączeń. - Załaduj ponownie skrypt AA i skrypty kolejki połączeń. Użyj polecenia
call application voice loadw trybie uprzywilejowanym EXEC, aby załadować ponownie skrypty. - Jeśli plik z komunikatem audio został zmieniony, załaduj go ponownie. Aby załadować ponownie plik audio, użyj polecenia
audio-prompt loadw trybie uprzywilejowanym EXEC. Powtórz to polecenie dla każdego zmienionego pliku audio.
Weryfikacja statusu B-ACD
Użyj polecenia show call application sessions, aby sprawdzić, czy B-ACD jest aktywny.
Poniższy przykład pokazuje sesję z aktywnymi aplikacjami AA i kolejki połączeń. Pole „Aplikacja” to nazwa usługi, a pole „Adres URL” to lokalizacja pliku skryptu dla aplikacji
Session ID 17
App: aa
Type: Service
Url: flash:app-b-acd-aa-2.1.0.0.tcl
Session ID 12
App: queue
Type: Service
Url: flash:app-b-acd-2.1.0.0.tcl Poniższy przykład pokazuje sesję z aktywną tylko aplikacją kolejki. Skrypt AA nie pojawia się w wynikach polecenia show call application sessions, ponieważ nie ma aktywnych wywołań. Nazwa usługi AA pojawia się na wyjściu tylko wtedy, gdy istnieje aktywne połączenie. Skrypt kolejki połączeń aktywuje się po pierwszym połączeniu przychodzącym i pozostaje aktywny nawet wtedy, gdy nie ma aktywnych połączeń.
Router# show call application sessions
Session ID 12
App: queue
Type: Service
Url: flash:app-b-acd-2.1.0.0.tclParametry skryptu B-ACD można aktualizować, wprowadzając zmiany w konfiguracji Cisco IOS. Aby zmiany parametrów zostały zastosowane, musisz zatrzymać i ponownie załadować skrypty B-ACD, w których wprowadziłeś zmiany, zgodnie z opisem w poniższych krokach. Jeśli ponownie nagrywasz komunikaty audio, musisz ponownie wczytać pliki komunikatów audio, które uległy zmianie.
-
Określ identyfikatory sesji wszystkich aktywnych sesji:
Użyj polecenia
show call application sessionsw trybie uprzywilejowanym EXEC, aby uzyskać numery identyfikatorów sesji (SID) usług AA i kolejki połączeń. Jeśli sesja AA nie ma aktywnych połączeń, nazwa skryptu AA nie jest wyświetlana w wynikach poleceniashow call application sessions.Poniższy przykład pokazuje sesję z aktywnymi połączeniami. Pole „Aplikacja” to nazwa usługi nadana skryptowi kolejki połączeń i skryptowi AA. Nazwy usług można również zobaczyć w wynikach polecenia show running-config.
Router# show call application sessions Session ID 17 App: aa Type: Service Url: bootflash:app-b-acd-aa-3.0.0.8.tcl Session ID 12 App: queue Type: Service Url: bootflash:app-b-acd-3.0.0.8.tcl - W razie potrzeby zatrzymaj sesje usługi AA i kolejki połączeń B-ACD
Używając numerów identyfikacyjnych sesji z kroku 1, zatrzymaj sesje usługi B-ACD AA i usługi kolejki połączeń. Użyj polecenia
call application session stopw trybie uprzywilejowanym EXEC, aby zatrzymać sesje AA i kolejki połączeń.Router# call application session stop id 17 Router# call application session stop id 12Po użyciu polecenia zatrzymania sesji aplikacji wywołania dla usługi AA wykonywane są następujące czynności:
Usługa AA została zatrzymana.
Wszystkie połączenia aktywnie nawiązane z usługą AA zostaną rozłączone.
Nazwa usługi AA została usunięta z wyników polecenia
show call application sessions.Aby wyeliminować możliwość rozłączenia połączeń, przed ponownym załadowaniem skryptu należy zaczekać, aż nie będzie żadnych połączeń przychodzących, np. po godzinach pracy.
Jeżeli nazwa usługi AA nie pojawia się w wynikach polecenia
show call application sessions, oznacza to, że nie ma żadnych sesji połączeń i nie trzeba wydawać dla niej poleceniacall application session stop. -
Załaduj ponownie skrypt AA i skrypty kolejki połączeń
Użyj polecenia
call application voice loadw trybie uprzywilejowanym EXEC, aby ponownie załadować skrypty.Router# call application voice load aa Router# call application voice load queue -
Jeśli plik z komunikatem audio został zmieniony, wczytaj go ponownie
Użyj polecenia
audio-prompt loadw trybie uprzywilejowanym EXEC, aby przeładować plik audio. Powtórz to polecenie dla każdego zmienionego pliku audio.Router# audio-prompt load flash:en_bacd_welcome.au Reload of flash:en_bacd_welcome.au successful
Ograniczenia i restrykcje
-
Dostępność usług publicznej sieci telefonicznej PSTN zależy od dostępności łączy SIP lub obwodów PSTN w przypadku awarii sieci.
-
Urządzenia z łącznością 4G i 5G (na przykład aplikacja Webex na urządzenia mobilne i tablety) będą mogły nadal rejestrować się w usłudze Webex Calling podczas przerw w dostawie prądu. W rezultacie podczas awarii nie będą mogli dzwonić na inne numery z tej samej lokalizacji.
-
W trybie przetrwania wzorce wybierania numerów mogą działać inaczej niż w trybie aktywnym.
-
Brama Survivability musi używać adresu IPv4. Protokół IPv6 nie jest obsługiwany.
-
Aktualizacja statusu synchronizacji na żądanie w Control Hub może potrwać do 30 minut.
-
Stacja dokująca Calling nie jest obsługiwana w trybie przetrwania.
-
Nie konfiguruj polecenia SIP bind w trybie konfiguracji usługi głosowej VoIP. Prowadzi to do niepowodzenia rejestracji telefonów MPP z Survivability Gateway.
-
Upewnij się, że numery ESN (Enterprise Significant Numbers) w różnych lokalizacjach fizycznych są unikalne. Pozwoli to uniknąć konfliktów i poprawić możliwość śledzenia, redundancję i niezawodność przełączania awaryjnego.
W trybie przetrwania obowiązują następujące ograniczenia:
-
Klawisze funkcyjne MPP: Takie klawisze funkcyjne jak Parkuj, Odparkuj, Wtrąć, Odbierz, Odbierz grupowo i Odbierz połączenie nie są obsługiwane, ale nie są wyświetlane jako wyłączone na urządzeniu.
-
Linie współdzielone: Połączenia wykonywane na linie współdzielone mogą być sygnalizowane dźwiękiem na wszystkich urządzeniach. Jednak inne funkcje linii współdzielonych, takie jak zdalne monitorowanie stanu linii, wstrzymywanie, wznawianie, zsynchronizowane ustawienie Nie przeszkadzać (DND) i przekierowywanie połączeń, nie są dostępne.
-
Konferencja: Konferencje i połączenia trójstronne nie są obsługiwane.
-
Podstawowa automatyczna dystrybucja połączeń (B-ACD): Usługa z kolokacją Survivability Gateway i Local Gateway nie jest obsługiwana.
-
Historia połączeń: Wykonane połączenia są zapisywane lokalnie w historii połączeń zarówno na urządzeniach MPP, jak i w aplikacji Webex.
-
Grupy łowieckie: Można skonfigurować maksymalnie 100 grup polowań, przy czym każda grupa może obsługiwać maksymalnie 32 użytkowników.
-
Ulepszony wygląd współdzielonych połączeń: Funkcje takie jak powiadomienie o stanie linii, linia współdzielona hold/remote wznawiania, a inne z podstawowymi połączeniami, grupami polowań lub przekierowaniem połączeń nie są obsługiwane.
-
Trasowanie połączeń grupy Hunt: Ważony wzorzec kierowania połączeń nie jest obsługiwany.
Doświadczenia użytkownika podczas przełączania awaryjnego
Jeśli jakaś lokalizacja w Twojej firmie utraci połączenie z Internetem, a Ty znajdujesz się w tej lokalizacji, możesz nadal nawiązywać i odbierać połączenia, zarówno połączenia wewnętrzne w firmie, jak i połączenia zewnętrzne do klientów. Zobacz Aplikacja Webex | Przeżywalność witryny.
Przykłady konfiguracji
Przykłady połączeń PSTN
W celu wykonywania połączeń zewnętrznych należy skonfigurować połączenie z siecią PSTN. W tym temacie opisano niektóre opcje i przedstawiono przykładowe konfiguracje. Dwiema głównymi opcjami są:
-
Połączenie karty interfejsu głosowego (VIC) z PSTN
-
SIP trunk do bramy PSTN
Podłączenie karty interfejsu głosowego do PSTN
Na routerze możesz zainstalować kartę interfejsu głosowego (VIC) i skonfigurować połączenie portu z siecią PSTN.
-
Szczegółowe informacje na temat instalacji modułu VIC na routerze znajdziesz w instrukcji instalacji sprzętu dotyczącej Twojego modelu routera.
-
Szczegółowe informacje na temat konfiguracji VIC wraz z przykładami można znaleźć w Przewodniku konfiguracji portu głosowego, Cisco IOS wersja 3S.
SIP trunk do bramy PSTN
Można skonfigurować połączenie SIP trunk wskazujące na bramkę PSTN. Aby skonfigurować połączenie magistralne na bramie, należy użyć konfiguracji voice-class-tenant. Poniżej przedstawiono przykładową konfigurację.
voice class tenant 300
sip-server ipv4::
session transport udp
bind all source-interface GigabitEthernet0/0/1
Konfiguracja równorzędna wybierania numeru
W przypadku połączeń międzymiastowych należy skonfigurować równorzędne połączenia przychodzące i wychodzące dla danego połączenia. Konfiguracja zależy od Twoich wymagań. Aby uzyskać szczegółowe informacje dotyczące konfiguracji, zobacz Dial Peer Configuration Guide, Cisco IOS Release 3S.
Poniżej przedstawiono przykładowe konfiguracje:
Połączenia wychodzące do PSTN z protokołami UDP i RTP
dial-peer voice 300 voip
description outbound to PSTN
destination-pattern +1[2-9]..[2-9]......$
translation-profile outgoing 300
rtp payload-type comfort-noise 13
session protocol sipv2
session target sip-server
voice-class codec 1
voice-class sip tenant 300
dtmf-relay rtp-nte
no vad
Połączenie przychodzące z PSTN przy użyciu protokołu UDP z RTP
voice class uri 350 sip
host ipv4:
!
dial-peer voice 190 voip
description inbound from PSTN
translation-profile incoming 350
rtp payload-type comfort-noise 13
session protocol sipv2
voice-class codec 1
voice-class sip tenant 300
dtmf-relay rtp-nte
no vad
Tłumaczenia liczbowe
W przypadku połączeń PSTN może zaistnieć konieczność użycia reguł translacji w celu przetłumaczenia wewnętrznych numerów wewnętrznych na numer E.164, który PSTN może kierować. Poniżej przedstawiono przykładowe konfiguracje:
Z reguły translacji PSTN z nie +E164
voice translation-rule 350
rule 1 /^\([2-9].........\)/ /+1\1/
voice translation-profile 300
translate calling 300
translate called 300
Z reguły tłumaczenia systemu telefonicznego z +E164
voice translation-rule 300
rule 1 /^\+1\(.*\)/ /\1/
voice translation-profile 300
translate calling 300
translate called 300
Przykład połączenia alarmowego
Poniższy przykład przedstawia konfigurację połączeń alarmowych.
Jeśli nakładka WiFi nie jest dokładnie dopasowana do podsieci IP, mapowanie ELIN dla połączeń alarmowych z urządzeń nomadycznych może nie być prawidłowe.
Lokalizacje reagowania kryzysowego (ERL)
voice emergency response location 1
elin 1 14085550100
subnet 1 192.168.100.0 /26
!
voice emergency response location 2
elin 1 14085550111
subnet 1 192.168.100.64 /26
!
voice emergency response zone 1
location 1
location 2
Wychodzące połączenia równorzędne
voice class e164-pattern-map 301
description Emergency services numbers
e164 911
e164 988
!
voice class e164-pattern-map 351
description Emergency ELINs
e164 14085550100
e164 14085550111
!
dial-peer voice 301 pots
description Outbound dial-peer for E911 call
emergency response zone 1
destination e164-pattern-map 301
!
dial-peer voice 301 pots
description Inbound dial-peer for E911 call
emergency response callback
incoming called e164-pattern-map 351
direct-inward-dial


